Email strategy
Secure access to email from mobile devices is one of the main drivers behind any organization’s mobility management initiative. Deciding on the proper email strategy is often a key component of any Citrix Endpoint Management design. Citrix Endpoint Management offers several options to accommodate different use cases, based on security, user experience, and integration requirements. This article covers the typical design decision process and considerations for choosing the right solution, from client selection to mail traffic flow.
Choosing your email clients
Client selection is generally at the top of the list for the overall email strategy design. You can choose from several clients: Citrix Secure Mail, native mail that is included with a particular mobile platform operating system, or other third-party clients available through the public app stores. Depending on your needs, you can possibly support the user communities with a single (standard) client or you might have to use a combination of clients.
The following table outlines some design considerations for the different client options available:
| Topic | Citrix Secure Mail | Native (for example, iOS Mail) | Third-party mail |
| Configuration | Exchange account profiles configured via an MDX policy. | Exchange account profiles configured via an MDM policy. Android support is limited to: Android Enterprise. All other clients are considered third-party clients. | Generally requires manual configuration by the user. |
| Security | Secure by design, providing the highest security. Uses MDX policies with added data encryption levels. Citrix Secure Mail is a fully managed app via an MDX policy. Added layer of authentication with Citrix PIN. | Based on vendor/app feature set. Provides higher security. Uses device encryption settings. Relies on device-level authentication for access to the app. | Based on vendor/app feature set. Provides high security. |
| Integration | Allows interaction with managed (MDX) apps by default. Open web URLs with Citrix Secure Web. Save files to and attach files from Citrix Files. Directly join and dial in to GoToMeeting. | Can only interact with other unmanaged (non-MDX) apps by default. | Can only interact with other unmanaged (non-MDX) apps by default. |
| Deployment/ Licensing | You can push Citrix Secure Mail through MDM, directly from public app stores. Included with Citrix Endpoint Management Advanced and Enterprise licensing. | Client app included with platform operating system. No additional licensing requirements. | You can push via MDM, as an enterprise app or directly from public app stores. Associated licensing model/costs based on app vendor. |
| Support | Single vendor support for the client and EMM solution (Citrix). Embedded support contact info in Citrix Secure Hub/app debug logging capabilities. One client to support. | Vendor defined support (Apple/Google). Might have to support different clients based on device platform. | Vendor-defined support. One client to support, assuming that the third-party client is supported on all managed device platforms. |
Mail traffic flow and filtering considerations
This section discusses the three main scenarios and design considerations about the flow of mail (ActiveSync) traffic in the context of Citrix Endpoint Management.
Scenario 1: Exposed Exchange
Environments that support external clients commonly have Exchange ActiveSync services exposed to the internet. Mobile ActiveSync clients connect through this externally facing path through a reverse proxy (for example, NetScaler Gateway) or through an Edge Server. This option is required for the use of native or third-party mail clients, making these clients the popular choice for this scenario. Although not a common practice, you can also use the Citrix Secure Mail client in this scenario. By doing so, you benefit from the security features offered by the use of MDX policies and management of the app.
Scenario 2: Tunneled via NetScaler Gateway (micro VPN and STA)
This scenario is the default when using the Citrix Secure Mail client, because of its micro VPN capabilities. In this case, the Citrix Secure Mail client establishes a secure connection to ActiveSync via NetScaler Gateway. In essence, you can consider Citrix Secure Mail to be the client connecting directly to ActiveSync from the internal network. Citrix customers often standardize on Citrix Secure Mail as the mobile ActiveSync client of choice. That decision is part of an initiative to avoid exposing ActiveSync services to the internet on an exposed Exchange Server, as described in the first scenario.
Only apps that are MAM SDK enabled or MDX-wrapped can use the micro VPN function. This scenario does not apply to native clients if you use MDX wrapping. Even though it might be possible to wrap third-party clients with the MDX Toolkit, this practice is not common. The use of device-level VPN clients to allow tunneled access for native or third-party clients has proven to be cumbersome and not a feasible solution.
Scenario 3: Cloud-hosted Exchange services
Cloud-hosted Exchange services, such as Microsoft Office 365, are becoming more popular. In the context of Citrix Endpoint Management, this scenario might be treated in the same way as the first scenario, because the ActiveSync service is also exposed to the internet. In this case, cloud service provider requirements dictate client choices. The choices generally include support for most ActiveSync clients, such as Citrix Secure Mail and other native or third-party clients.
Citrix Endpoint Management can add value in three areas for this scenario:
- Clients with MDX policies and app management with Citrix Secure Mail
- Client configuration with the use of an MDM policy on supported native email clients
- ActiveSync filtering options with the use of the Citrix Endpoint Management connector for Exchange ActiveSync
Mail traffic filtering considerations
As with most services exposed to the internet, you must secure the path and provide filtering for authorized access. The Citrix Endpoint Management solution includes two components designed specifically to provide ActiveSync filtering capabilities for native and third-party clients: NetScaler Gateway connector for Exchange ActiveSync and Citrix Endpoint Management connector for Exchange ActiveSync.
NetScaler Gateway connector for Exchange ActiveSync
NetScaler Gateway connector for Exchange ActiveSync provides ActiveSync filtering at the perimeter, by using NetScaler Gateway as a proxy for ActiveSync traffic. As a result, the filtering component sits in the path of mail traffic flow, intercepting mail as it enters or leaves the environment. The connector for Exchange ActiveSync acts an intermediary between NetScaler Gateway and Citrix Endpoint Management. When a device communicates with Exchange through the ActiveSync virtual server on the NetScaler Gateway, NetScaler Gateway does an HTTP callout to the connector for the Exchange ActiveSync service. That service then checks the device status with Citrix Endpoint Management. Based on the status of the device, the connector for Exchange ActiveSync replies to NetScaler Gateway to either allow or deny the connection. You might also configure static rules to filter access based on user, agent, and device type or ID.
This setup allows Exchange ActiveSync services to be exposed to the internet with an added layer of security to prevent unauthorized access. Design considerations include the following:
- Windows Server: The connector for the Exchange ActiveSync component requires a Windows Server.
- Filtering rule set: The connector for Exchange ActiveSync is designed for filtering based on device state and information, rather than user information. Although you might configure static rules to filter by user ID, no options exist for filtering based on Active Directory group membership, for example. If there is a requirement for Active Directory group filtering, you can use the Citrix Endpoint Management connector for Exchange ActiveSync instead.
- NetScaler Gateway scalability: Given the requirement to proxy ActiveSync traffic via NetScaler Gateway: Proper sizing of the NetScaler Gateway instance is critical to support the added workload of all ActiveSync SSL connections.
- NetScaler Gateway Integrated Caching: The connector for the Exchange ActiveSync configuration on the NetScaler Gateway uses the Integrated Caching function to cache responses from the connector. Becuase of that configuration, NetScaler Gateway doesn’t need to issue a request to the connector for every ActiveSync transaction in a given session. That configuration is also critical for adequate performance and scale. Integrated Caching is available with the NetScaler Gateway Platinum Edition.
- Custom filtering policies: You might have to create custom NetScaler Gateway policies to restrict certain ActiveSync clients outside of the standard native mobile clients. This configuration requires knowledge on ActiveSync HTTP requests and NetScaler Gateway responder policy creation.
- Citrix Secure Mail clients: Citrix Secure Mail has micro VPN capabilities which eliminate the need for filtering at the perimeter. The Citrix Secure Mail client might generally be treated as an internal (trusted) ActiveSync client when connected through the NetScaler Gateway. If support for both native and third-party (with the connector for Exchange ActiveSync) and Citrix Secure Mail clients is required: Citrix recommends that Citrix Secure Mail traffic does not flow via the NetScaler Gateway virtual server used for the connector. You can accomplish this traffic flow via DNS and keep the connector policy from affecting Citrix Secure Mail clients.
For a diagram of the NetScaler Gateway connector for Exchange ActiveSync in an Citrix Endpoint Management deployment, see Architecture.
Citrix Endpoint Management connector for Exchange ActiveSync
Citrix Endpoint Management connector for Exchange ActiveSync is an Citrix Endpoint Management component that provides ActiveSync filtering at the Exchange service level. As a result, filtering only occurs once the mail reaches the exchange service, rather than when it enters the Citrix Endpoint Management environment. Mail Manager uses PowerShell to query Exchange ActiveSync for device partnership information and control access through device quarantine actions. Those actions take devices in and out of quarantine based on the Citrix Endpoint Management connector for Exchange ActiveSync rule criteria.
Similar to NetScaler Gateway connector for Exchange ActiveSync, the connector for Exchange ActiveSync checks the device status with Citrix Endpoint Management to filter access based on device compliance. You might also configure static rules to filter access based on device type or ID, agent version, and Active Directory group membership.
This solution does not require the use of NetScaler Gateway. You can deploy the connector for Exchange ActiveSync without changes routing for the existing ActiveSync traffic. Design considerations include:
- Windows Server: The connector for Exchange ActiveSync requires you to deploy Windows Server.
- Filtering rule set: Just like the NetScaler Gateway connector for Exchange ActiveSync, the connector for Exchange ActiveSync includes filtering rules to evaluate device state. Also, the connector for Exchange ActiveSync also supports static rules to filter based on Active Directory group membership.
- Exchange integration: The connector for Exchange ActiveSync requires direct access to the Exchange Client Access Server (CAS) hosting the ActiveSync role and control over device quarantine actions. This requirement might present a challenge depending on the environment architecture and security posture. It is critical that you evaluate this technical requirement up front.
- Other ActiveSync clients: Because the connector for Exchange ActiveSync is filtering at the ActiveSync service level, consider other ActiveSync clients outside the Citrix Endpoint Management environment. You can configure the connector for Exchange ActiveSync static rules to avoid unintended impact to other ActiveSync clients.
- Extended Exchange functions: Through direct integration with Exchange ActiveSync, the connector for Exchange ActiveSync provides the ability for Citrix Endpoint Management to do an Exchange ActiveSync wipe on a mobile device. The connector for Exchange ActiveSync also allows Citrix Endpoint Management to access information about Blackberry devices and to do other control operations.
For a diagram of the Citrix Endpoint Management connector for Exchange ActiveSync in an Citrix Endpoint Management deployment, see Architecture.
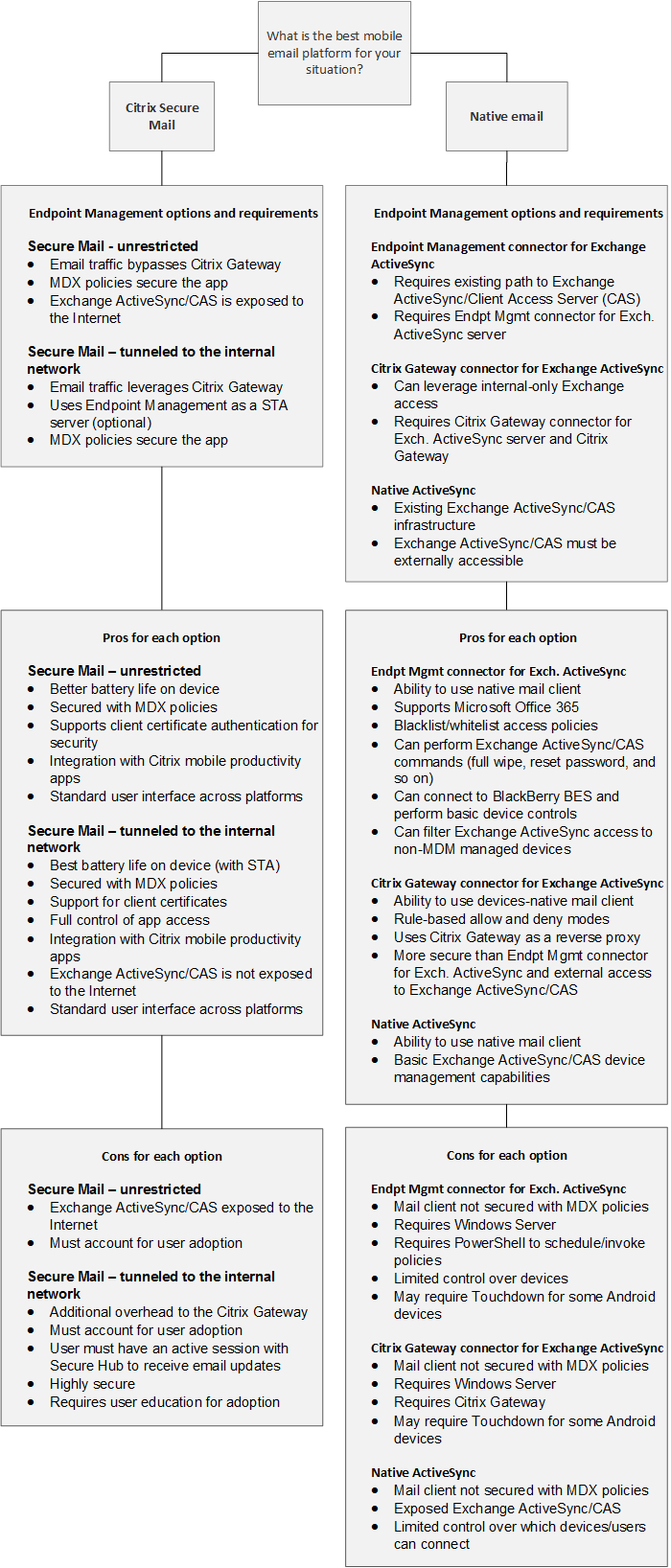
Email platform decision tree
The following figure helps you distinguish the pros and cons between using native email or Citrix Secure Mail solutions in your Citrix Endpoint Management deployment. Each choice allows for associated Citrix Endpoint Management options and requirements to enable server, network, and database access. The pros and cons include details on security, policy, and user interface considerations.