NetScaler Gateway configuration for Web/SaaS applications
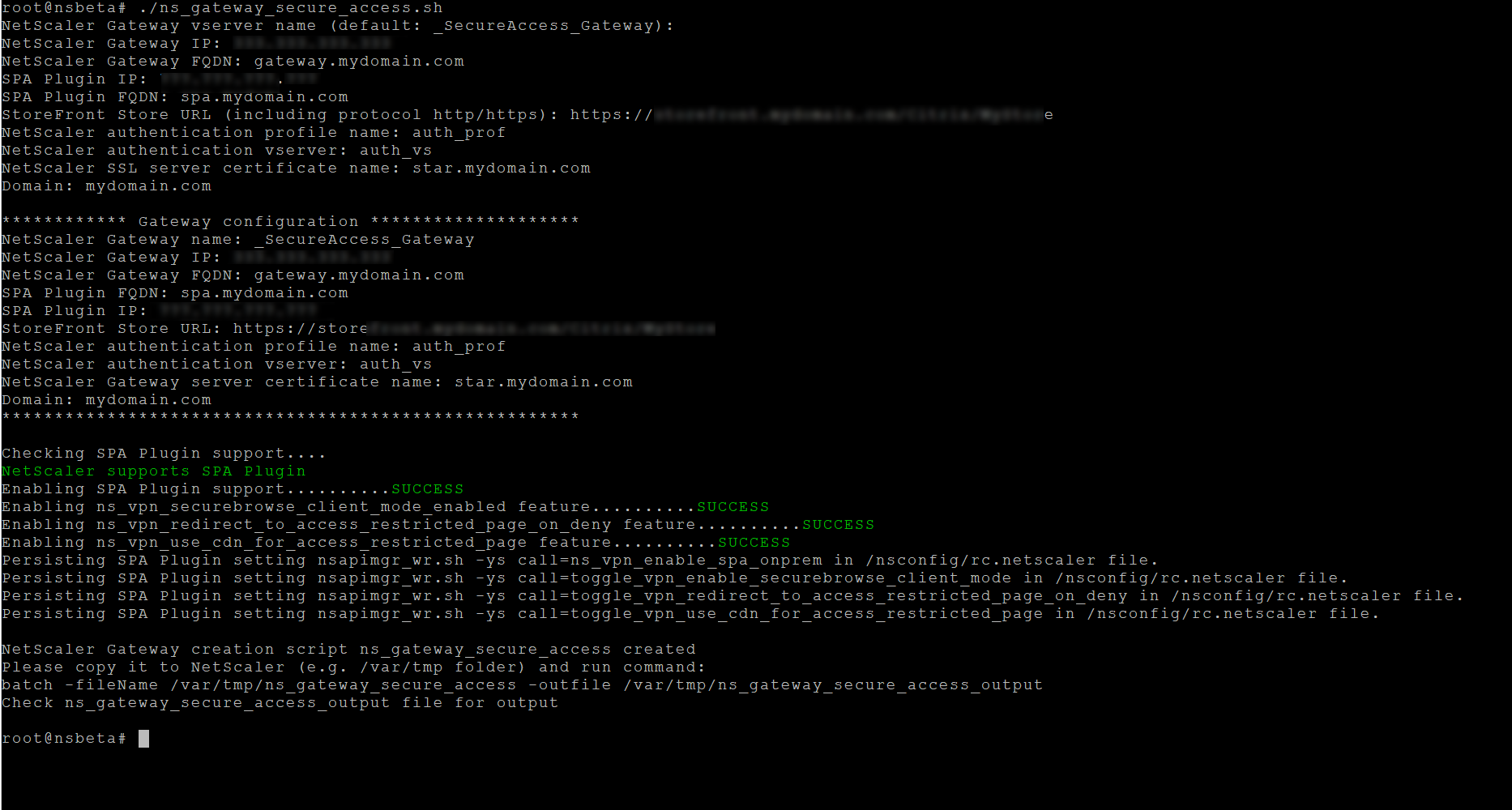
To create NetScaler Gateway for Web/SaaS applications, perform the following steps:
-
Download the latest script
*ns_gateway_secure_access.sh*.from https://www.citrix.com/downloads/citrix-secure-private-access/Shell-Script/Shell-Script-for-Gateway-Configuration.html. -
Upload these scripts to the NetScaler machine. You can use the WinSCP app or the SCP command. For example,
*scp ns_gateway_secure_access.sh nsroot@nsalfa.fabrikam.local:/var/tmp*.For example,
*scp ns_gateway_secure_access.sh nsroot@nsalfa.fabrikam.local:/var/tmp*Note:
- It’s recommended to use NetScaler /var/tmp folder to store temp data.
- Make sure that the file is saved with LF line endings. FreeBSD does not support CRLF.
- If you see the error
-bash: /var/tmp/ns_gateway_secure_access.sh: /bin/sh^M: bad interpreter: No such file or directory, it means that the line endings are incorrect. You can convert the script by using any rich text editor, such as Notepad++.
- SSH to NetScaler and switch to shell (type ‘shell’ on NetScaler CLI).
-
Make the uploaded script executable. Use the chmod command to do so.
chmod +x /var/tmp/ns_gateway_secure_access.sh -
Run the uploaded script on the NetScaler shell.
-
Enter N for the Enable TCP/UDP App type support parameter if you intend to configure gateway only for Web and SaaS applications.
-
Input the required parameters. For the list of parameters, see Prerequisites.
For the authentication profile and SSL certificate you have to provide names of existing resources on NetScaler.
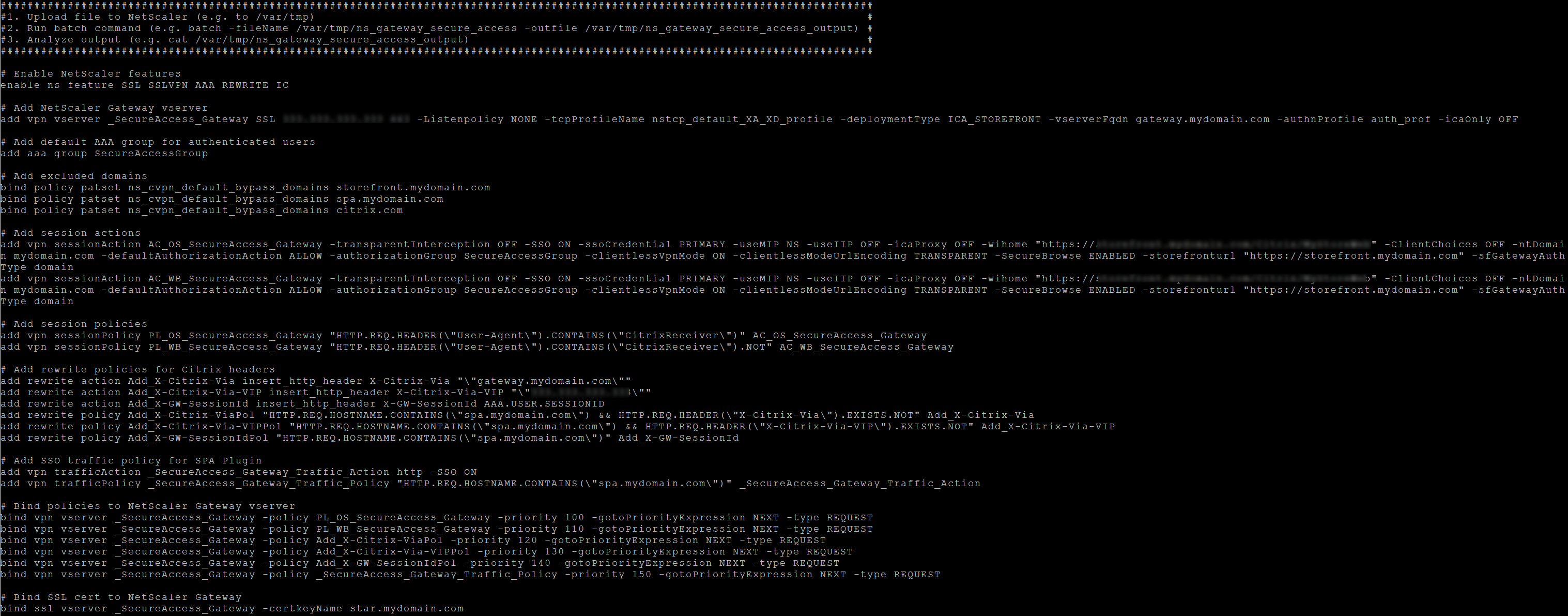
A new file with multiple NetScaler commands (the default is var/tmp/ns_gateway_secure_access) is generated.
Note:
During script execution, NetScaler and Secure Private Access plug-in compatibility is checked. If NetScaler supports the Secure Private Access plug-in, the script enables NetScaler features to support smart access tags sending improvements and redirection to a new Deny Page when access to a resource is restricted. For details about smart tags, see Support for smart access tags.
The Secure Private Access plug-in features persisted in the /nsconfig/rc.netscaler file allow to keep them enabled after NetScaler is restarted.
-
Switch to the NetScaler CLI and run the resultant NetScaler commands from the new file with the batch command. For example;
batch -fileName /var/tmp/ns_gateway_secure_access -outfile/var/tmp/ns_gateway_secure_access_outputNetScaler runs the commands from the file one by one. If a command fails, it continues with the next command.
A command can fail if a resource exists or one of the parameters entered in step 6 is incorrect.
- Ensure that all commands are successfully completed.
Note:
If there’s an error, NetScaler still runs the remaining commands and partially creates/updates/binds resources. Therefore, if you see an unexpected error because of one of the parameters being incorrect, it’s recommended to redo the configuration from the start.
Update existing NetScaler Gateway configuration for Web and SaaS apps
You can use the ns_gateway_secure_access_update.shscript on an existing NetScaler Gateway to update the configuration for Web and SaaS apps. However, if you want to update the existing configuration (NetScaler Gateway version 14.1–4.42 and later) manually, use the Example commands to update an existing NetScaler Gateway configuration. Also, you must update the NetScaler Gateway virtual server and session action settings.
Note:
Starting from NetScaler Gateway 14.1–25.56 and later, you can enable the Secure Private Access plug-in on NetScaler Gateway by using the NetScaler Gateway CLI or the GUI. For details, see Enable Secure Private Access plug-in on NetScaler Gateway.
You can also use the scripts on an existing NetScaler Gateway to support Secure Private Access. However, the script does not update the following:
- Existing NetScaler Gateway virtual server
- Existing session actions and session policies bound to NetScaler Gateway
Ensure that you review each command before execution and create backups of the gateway configuration.
NetScaler Gateway virtual server settings
When you add or update the existing NetScaler Gateway virtual server, ensure that the following parameters are set to the defined values. For sample commands, see Example commands to update an existing NetScaler Gateway configuration.
Add a virtual server:
- tcpProfileName: nstcp_default_XA_XD_profile
- deploymentType: ICA_STOREFRONT (available only with the
add vpn vservercommand) - icaOnly: OFF
Update a virtual server:
- tcpProfileName: nstcp_default_XA_XD_profile
- icaOnly: OFF
NetScaler Gateway session policy settings
Session action is bound to a gateway virtual server with session policies. When you create or update a session action, ensure that the following parameters are set to the defined values. For sample commands, see Example commands to update an existing NetScaler Gateway configuration.
-
transparentInterception: OFF -
SSO: ON -
ssoCredential: PRIMARY -
useMIP: NS -
useIIP: OFF -
icaProxy: OFF -
wihome:"https://storefront.mydomain.com/Citrix/MyStoreWeb"- replace with real store URL. Path to Store/Citrix/MyStoreWebis optional. -
ClientChoices: OFF -
ntDomain: mydomain.com - used for SSO (optional) -
defaultAuthorizationAction: ALLOW -
authorizationGroup: SecureAccessGroup (Make sure that this group is created, it’s used to bind Secure Private Access specific authorization policies) -
clientlessVpnMode: ON -
clientlessModeUrlEncoding: TRANSPARENT -
SecureBrowse: ENABLED -
Storefronturl:"https://storefront.mydomain.com" -
sfGatewayAuthType: domain
Example commands to update an existing NetScaler Gateway configuration
Add/update a virtual server:
add vpn vserver SecureAccess_Gateway SSL 999.999.999.999 443 -Listenpolicy NONE -tcpProfileName nstcp_default_XA_XD_profile -deploymentType ICA_STOREFRONT -vserverFqdn gateway.mydomain.com -authnProfile auth_prof_name -icaOnly OFFset vpn vserver SecureAccess_Gateway -icaOnly OFF
Add a session action:
add vpn sessionAction AC_OSspaonprem -transparentInterception OFF -defaultAuthorizationAction ALLOW -authorizationGroup SecureAccessGroup -SSO ON -ssoCredential PRIMARY -useMIP NS -useIIP OFF -icaProxy OFF -wihome "https://storefront.example.corp/Citrix/SPAWeb" -ClientChoices OFF -ntDomain example.corp -clientlessVpnMode ON -clientlessModeUrlEncoding TRANSPARENT -SecureBrowse ENABLED -storefronturl "https://storefront.example.corp" -sfGatewayAuthType domainadd vpn sessionAction AC_WBspaonprem -transparentInterception OFF -defaultAuthorizationAction ALLOW -authorizationGroup SecureAccessGroup -SSO ON -ssoCredential PRIMARY -useMIP NS -useIIP OFF -icaProxy OFF -wihome "https://storefront.example.corp/Citrix/SPAWeb" -ClientChoices OFF -ntDomain example.corp -clientlessVpnMode ON -clientlessModeUrlEncoding TRANSPARENT -SecureBrowse ENABLED -storefronturl "https://storefront.example.corp" -sfGatewayAuthType domain
Add a session policy:
add vpn sessionPolicy PL_OSspaonprem "HTTP.REQ.HEADER(\"User-Agent\").CONTAINS(\"CitrixReceiver\")" AC_OSspaonpremadd vpn sessionPolicy PL_WBspaonprem "HTTP.REQ.HEADER(\"User-Agent\").CONTAINS(\"CitrixReceiver\").NOT && HTTP.REQ.HEADER(\"User-Agent\").CONTAINS(\"plugin\").NOT" AC_WBspaonprem
Bind the session policy to the VPN virtual server:
bind vpn vserver SecureAccess_Gateway -policy PL_OSspaonprem -priority 111 -gotoPriorityExpression NEXT -type REQUESTbind vpn vserver SecureAccess_Gateway -policy PL_WBspaonprem -priority 110 -gotoPriorityExpression NEXT -type REQUEST
Bind the Secure Private Access plug-in to the VPN virtual server:
bind vpn vserver spaonprem -appController "https://spa.example.corp"
For details on session action parameters, vpn-sessionAction.
Additional information
For additional information on NetScaler Gateway for Secure Private Access, see the following topics: