Citrix ADC VPX on AWS Deployment Guide
Overview
Citrix ADC is an application delivery and load balancing solution that provides a high-quality user experience for web, traditional, and cloud-native applications regardless of where they are hosted. It comes in a wide variety of form factors and deployment options without locking users into a single configuration or cloud. Pooled capacity licensing enables the movement of capacity among cloud deployments.
As an undisputed leader of service and application delivery, Citrix ADC is deployed in thousands of networks around the world to optimize, secure, and control the delivery of all enterprise and cloud services. Deployed directly in front of web and database servers, Citrix ADC combines high-speed load balancing and content switching, HTTP compression, content caching, SSL acceleration, application flow visibility, and a powerful application firewall into an integrated, easy-to-use platform. Meeting SLAs is greatly simplified with end-to-end monitoring that transforms network data into actionable business intelligence. Citrix ADC allows policies to be defined and managed using a simple declarative policy engine with no programming expertise required.
Citrix ADC VPX
The Citrix ADC VPX product is a virtual appliance that can be hosted on a wide variety of virtualization and cloud platforms.
This deployment guide focuses on Citrix ADC VPX on Amazon Web Services.
Amazon Web Services
Amazon Web Services (AWS) is a comprehensive, evolving cloud computing platform provided by Amazon that includes a mixture of infrastructure as a service (IaaS), platform as a service (PaaS) and packaged software as a service (SaaS) offerings. AWS services offer tools such as compute power, database storage, and content delivery services.
AWS offers the following essential services:
-
AWS Compute Services
-
Migration Services
-
Storage
-
Database Services
-
Management Tools
-
Security Services
-
Analytics
-
Networking
-
Messaging
-
Developer Tools
-
Mobile Services
AWS Terminology
Here is a brief description of key terms used in this document that users must be familiar with:
-
Elastic Network Interface (ENI) – A virtual network interface that users can attach to an instance in a Virtual Private Cloud (VPC).
-
Elastic IP (EIP) address – A static, public IPv4 address that users have allocated in Amazon EC2 or Amazon VPC and then attached to an instance. Elastic IP addresses are associated with user accounts, not a specific instance. They are elastic because users can easily allocate, attach, detach, and free them as their needs change.
-
Subnet – A segment of the IP address range of a VPC with which EC2 instances can be attached. Users can create subnets to group instances according to security and operational needs.
-
Virtual Private Cloud (VPC) – A web service for provisioning a logically isolated section of the AWS cloud where users can launch AWS resources in a virtual network that they define.
Here is a brief description of other terms used in this document that users should be familiar with:
-
Amazon Machine Image (AMI) – A machine image, which provides the information required to launch an instance, which is a virtual server in the cloud.
-
Elastic Block Store – Provides persistent block storage volumes for use with Amazon EC2 instances in the AWS Cloud.
-
Simple Storage Service (S3) – Storage for the Internet. It is designed to make web-scale computing easier for developers.
-
Elastic Compute Cloud (EC2) – A web service that provides secure, resizable compute capacity in the cloud. It is designed to make web-scale cloud computing easier for developers.
-
Elastic Kubernetes Service (EKS) – Amazon EKS is a managed service that makes it easy for users to run Kubernetes on AWS without needing to stand up or maintain their own Kubernetes control plane. … Amazon EKS runs Kubernetes control plane instances across multiple Availability Zones to ensure high availability. Amazon EKS is a managed service that makes it easy for users to run Kubernetes on AWS without needing to install and operate their own Kubernetes clusters.
-
Application Load Balancing (ALB) – Amazon ALB operates at layer 7 of the OSI stack so it’s employed when users want to route or select traffic based on elements of the HTTP or HTTPS connection, whether host-based or path-based. The ALB connection is context-aware and can have direct requests based on any single variable. Applications are load balanced based on their peculiar behavior not solely on server (operating system or virtualization layer) information.
-
Elastic Load Balancing (ALB/ELB/NLB) – Amazon ELB Distributes incoming application traffic across multiple EC2 instances, in multiple Availability Zones. This increases the fault tolerance of user applications.
-
Network Load Balancing (NLB) – Amazon NLB operates at layer 4 of the OSI stack and below and is not designed to consider anything at the application layer such as content type, cookie data, custom headers, user location, or application behavior. It is context-less, caring only about the network-layer information contained within the packets it is directing. It distributes traffic based on network variables such as IP address and destination ports.
-
Instance type – Amazon EC2 provides a wide selection of instance types optimized to fit different use cases. Instance types comprise varying combinations of CPU, memory, storage, and networking capacity and give users the flexibility to choose the appropriate mix of resources for their applications.
-
Identity and Access Management (IAM) – An AWS identity with permission policies that determine what the identity can and cannot do in AWS. Users can use an IAM role to enable applications running on an EC2 instance to securely access their AWS resources. IAM role is required for deploying VPX instances in a high-availability setup.
-
Internet Gateway – Connects a network to the Internet. Users can route traffic for IP addresses outside their VPC to the Internet gateway.
-
Key pair – A set of security credentials with which users prove their identity electronically. A key pair consists of a private key and a public key.
-
Route table – A set of routing rules that controls the traffic leaving any subnet that is associated with the route table. Users can associate multiple subnets with a single route table, but a subnet can be associated with only one route table at a time.
-
Auto Scale Groups – A web service to launch or terminate Amazon EC2 instances automatically based on user-defined policies, schedules, and health checks.
-
CloudFormation – A service for writing or changing templates that creates and deletes related AWS resources together as a unit.
-
Web Application Firewall (WAF) – WAF is defined as a security solution protecting the web application layer in the OSI network model. A WAF does not depend on the application it is protecting. This document focuses on the exposition and evaluation of the security methods and functions provided specifically by Citrix WAF.
-
Bot – Bot is defined as an autonomous device, program, or piece of software on a network (especially the internet) that can interact with computer systems or users to run commands, reply to messages, or perform routine tasks. A bot is a software program on the internet that performs repetitive tasks. Some bots can be good, while others can have a huge negative impact on a website or application.
Sample Citrix WAF on AWS Architecture
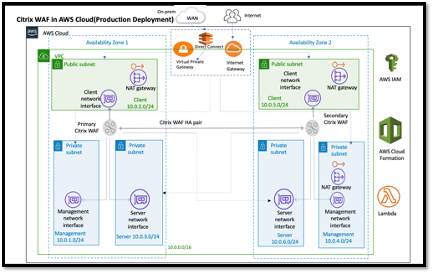
The preceding image shows a virtual private cloud (VPC) with default parameters that builds a Citrix WAF environment in the AWS Cloud.
In a production deployment, the following parameters are set up for the Citrix WAF environment:
-
This architecture assumes the use of an AWS CloudFormation Template and an AWS Quick Start Guide, which can be found here: GitHub/AWS-Quickstart/Quickstart-Citrix-ADC-VPX.
-
A VPC that spans two Availability Zones, configured with two public and four private subnets, according to AWS best practices, to provide you with your own virtual network on AWS with a /16 Classless Inter-Domain Routing (CIDR) block (a network with 65,536 private IP addresses). *
-
Two instances of Citrix WAF (Primary and Secondary), one in each Availability Zone.
-
Three security groups, one for each network interface (Management, Client, Server), that acts as virtual firewalls to control the traffic for their associated instances.
-
Three subnets, for each instance- one for management, one for client, and one for back-end server.
-
An internet gateway attached to the VPC, and a Public Subnets route table which is associated with public subnets so as to allow access to the internet. This gateway is used by the WAF host to send and receive traffic. For more information on Internet Gateways, see: Internet Gateways. *
-
5 Route tables-one public route table associated with client subnets of both primary and secondary WAF. The remaining 4 route tables link to each of the 4 private subnets (management and server-side subnets of primary and secondary WAF). *
-
AWS Lambda in WAF takes care of the following:
-
Configuring two WAF in each availability zone of HA mode
-
Creating a sample WAF Profile and thus pushing this configuration with respect to WAF
-
-
AWS Identity and Access Management (IAM) to securely control access to AWS services and resources for your users. By default, the CloudFormation Template (CFT) creates the required IAM role. However, users can provide their own IAM role for Citrix ADC instances.
-
In the public subnets, two managed Network Address Translation (NAT) gateways to allow outbound internet access for resources in public subnets.
Note:
The CFT WAF template that deploys the Citrix WAF into an existing VPC skips the components marked by asterisks and prompts users for their existing VPC configuration.
Backend servers are not deployed by the CFT.
Logical Flow of Citrix WAF on AWS
Logical Flow
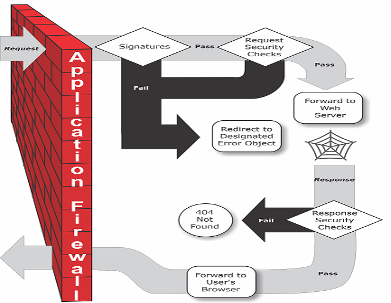
The Web Application Firewall can be installed as either a Layer 3 network device or a Layer 2 network bridge between customer servers and customer users, usually behind the customer company’s router or firewall. It must be installed in a location where it can intercept traffic between the web servers that users want to protect and the hub or switch through which users access those web servers. Users then configure the network to send requests to the Web Application Firewall instead of directly to their web servers, and responses to the Web Application Firewall instead of directly to their users. The Web Application Firewall filters that traffic before forwarding it to its final destination, using both its internal rule set and the user additions and modifications. It blocks or renders harmless any activity that it detects as harmful, and then forwards the remaining traffic to the web server. The preceding image provides an overview of the filtering process.
Note:
The diagram omits the application of a policy to incoming traffic. It illustrates a security configuration in which the policy is to process all requests. Also, in this configuration, a signatures object has been configured and associated with the profile, and security checks have been configured in the profile.
As the diagram shows, when a user requests a URL on a protected website, the Web Application Firewall first examines the request to ensure that it does not match a signature. If the request matches a signature, the Web Application Firewall either displays the error object (a webpage that is located on the Web Application Firewall appliance and which users can configure by using the imports feature) or forwards the request to the designated error URL (the error page).
If a request passes signature inspection, the Web Application Firewall applies the request security checks that have been enabled. The request security checks verify that the request is appropriate for the user website or web service and does not contain material that might pose a threat. For example, security checks examine the request for signs indicating that it might be of an unexpected type, request unexpected content, or contain unexpected and possibly malicious web form data, SQL commands, or scripts. If the request fails a security check, the Web Application Firewall either sanitizes the request and then sends it back to the Citrix ADC appliance (or Citrix ADC virtual appliance), or displays the error object. If the request passes the security checks, it is sent back to the Citrix ADC appliance, which completes any other processing and forwards the request to the protected web server.
When the website or web service sends a response to the user, the Web Application Firewall applies the response security checks that have been enabled. The response security checks examine the response for leaks of sensitive private information, signs of website defacement, or other content that should not be present. If the response fails a security check, the Web Application Firewall either removes the content that should not be present or blocks the response. If the response passes the security checks, it is sent back to the Citrix ADC appliance, which forwards it to the user.
Cost and Licensing
Users are responsible for the cost of the AWS services used while running AWS deployments. The AWS CloudFormation templates that can be used for this deployment include configuration parameters that users can customize as necessary. Some of those settings, such as instance type, affect the cost of deployment. For cost estimates, users should refer to the pricing pages for each AWS service they are using. Prices are subject to change.
A Citrix ADC WAF on AWS requires a license. To license Citrix WAF, users must place the license key in an S3 bucket and specify its location when they launch the deployment.
Note:
When users elect the Bring your own license (BYOL) licensing model, they should ensure that they have an AppFlow feature enabled. For more information on BYOL licensing, see: AWS Marketplace/Citrix ADC VPX - Customer Licensed.
The following licensing options are available for Citrix ADC WAF running on AWS. Users can choose an AMI (Amazon Machine Image) based on a single factor such as throughput.
-
License model: Pay as You Go (PAYG, for the production licenses) or Bring Your Own License (BYOL, for the Customer Licensed AMI - Citrix ADC Pooled Capacity). For more information on Citrix ADC Pooled Capacity, see: Citrix ADC Pooled Capacity.
-
For BYOL, there are 3 licensing modes:
-
Configure Citrix ADC Pooled Capacity: Configure Citrix ADC Pooled Capacity
-
Citrix ADC VPX Check-in and Check-out Licensing (CICO): Citrix ADC VPX Check-in and Check-out Licensing
Tip:
If users elect CICO Licensing with VPX-200, VPX-1000, VPX-3000, VPX-5000, or VPX-8000 application platform type, they should ensure that they have the same throughput license present in their ADM licensing server.
- Citrix ADC virtual CPU Licensing: Citrix ADC virtual CPU Licensing
-
-
Note:
If users want to dynamically modify the bandwidth of a VPX instance, they should elect a BYOL option, for example Citrix ADC pooled capacity where they can allocate the licenses from Citrix ADM, or they can check out the licenses from Citrix ADC instances according to the minimum and maximum capacity of the instance on demand and without a restart. A restart is required only if users want to change the license edition.
-
Throughput: 200 Mbps or 1 Gbps
-
Bundle: Premium
Deployment Options
This deployment guide provides two deployment options:
-
The first option is to deploy using a Quick Start Guide format and the following options:
-
Deploy Citrix WAF into a new VPC (end-to-end deployment). This option builds a new AWS environment consisting of the VPC, subnets, security groups, and other infrastructure components, and then deploys Citrix WAF into this new VPC.
-
Deploy Citrix WAF into an existing VPC. This option provisions Citrix WAF in the user existing AWS infrastructure.
-
-
The second option is to deploy using WAF StyleBooks using Citrix ADM
Deployment Steps using a Quick Start Guide
Step 1: Sign in to the User AWS Account
-
Sign in to the user account at AWS: AWS with an IAM (Identity and Access Management) user role that has the necessary permissions to create an Amazon Account (if necessary) or sign in to an Amazon Account.
-
Use the region selector in the navigation bar to choose the AWS Region where users want to deploy High Availability across AWS Availability Zones.
-
Ensure that the user AWS account is configured correctly, refer to the Technical Requirements section of this document for more information.
Step 2: Subscribe to the Citrix WAF AMI
-
This deployment requires a subscription to the AMI for Citrix WAF in the AWS Marketplace.
-
Sign in to the user AWS account.
-
Open the page for the Citrix WAF offering by choosing one of the links in the following table.
- When users launch the Quick Start Guide in to deploy Citrix WAF in Step 3 below, they use the Citrix WAF Image parameter to select the bundle and throughput option that matches their AMI subscription. The following list shows the AMI options and corresponding parameter settings. The VPX AMI instance requires a minimum of 2 virtual CPUs and 2 GB of memory.
Note:
To retrieve the AMI ID, refer to the Citrix Products on AWS Marketplace page on GitHub: Citrix Products on AWS Marketplace.
-
AWS Marketplace AMI
-
Citrix Web Application Firewall (WAF) - 200 Mbps: Citrix Web App Firewall (WAF) - 200 Mbps
-
Citrix Web Application Firewall (WAF) - 1000 Mbps: Citrix Web App Firewall (WAF) - 1000 Mbps
-
-
On the AMI page, choose Continue to Subscribe.
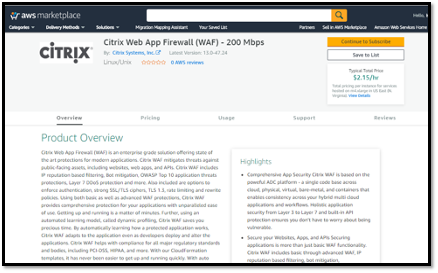
- Review the terms and conditions for software usage, and then choose Accept Terms.
Note:
Users receive a confirmation page, and an email confirmation is sent to the account owner. For detailed subscription instructions, see Getting Started in the AWS Marketplace Documentation: Getting Started.
- When the subscription process is complete, exit out of AWS Marketplace without further action. Do not provision the software from AWS Marketplace—users will deploy the AMI with the Quick Start Guide.
Step 3: Launch the Quick Start Guide to Deploy the AMI
-
Sign in to the user AWS account, and choose one of the following options to launch the AWS CloudFormation template. For help with choosing an option, see deployment options earlier in this guide.
-
Deploy Citrix VPX into a new VPC on AWS using one of the AWS CloudFormation Templates located here:
-
Deploy Citrix WAF into a new or existing VPC on AWS using the AWS Quickstart template located here: AWS-Quickstart/Quickstart-Citrix-ADC- WAF
-
Important:
If users are deploying Citrix WAF into an existing VPC, they must ensure that their VPC spans across two Availability Zones, with one public and two private subnets in each Availability Zone for the workload instances, and that the subnets are not shared. This deployment guide does not support shared subnets, see Working with Shared VPCs: Working with Shared VPCs. These subnets require NAT Gateways in their route tables to allow the instances to download packages and software without exposing them to the internet. For more information about NAT Gateways, see: NAT Gateways. Configure the subnets so there is no overlapping of subnets.
Also, users should ensure that the domain name option in the DHCP options is configured as explained in the Amazon VPC documentation found here: DHCP Options Sets: DHCP Options Sets. Users are prompted for their VPC settings when they launch the Quick Start Guide.
-
Each deployment takes about 15 minutes to complete.
-
Check the AWS Region that is displayed in the upper-right corner of the navigation bar, and change it if necessary. This is where the network infrastructure for Citrix WAF will be built. The template is launched in the US East (Ohio) Region by default.
Note:
This deployment includes Citrix WAF, which isn’t currently supported in all AWS Regions. For a current list of supported Regions, see the AWS Service Endpoints: AWS Service Endpoints.
-
On the Select Template page, keep the default setting for the template URL, and then choose Next.
-
On the Specify Details page, specify the stack name as per user convenience. Review the parameters for the template. Provide values for the parameters that require input. For all other parameters, review the default settings and customize them as necessary.
-
In the following table, parameters are listed by category and described separately for the deployment option:
-
Parameters for deploying Citrix WAF into a new or existing VPC (Deployment Option 1)
-
When users finish reviewing and customizing the parameters, they should choose Next.
Parameters for Deploying Citrix WAF into a new VPC
VPC Network Configuration
For reference information on this deployment refer to the CFT template here: AWS-Quickstart/Quickstart-Citrix-ADC-WAF/Templates.
| Parameter label (name) | Default | Description |
|---|---|---|
| Primary Availability Zone (PrimaryAvailabilityZone) | Requires input | The Availability Zone for Primary Citrix WAF deployment |
| Secondary Availability Zone (SecondaryAvailabilityZone) | Requires input | The Availability Zone for Secondary Citrix WAF deployment |
| VPC CIDR (VPCCIDR) | 10.0.0.0/16 | The CIDR block for the VPC. Must be a valid IP CIDR range of the form x.x.x.x/x. |
| Remote SSH CIDR IP(Management) (RestrictedSSHCIDR) | Requires input | The IP address range that can SSH to the EC2 instance (port: 22). |
| Remote HTTP CIDR IP(Client) (RestrictedWebAppCIDR) | 0.0.0.0/0 | The IP address range that can HTTP to the EC2 instance (port: 80) |
| Remote HTTP CIDR IP(Client) (RestrictedWebAppCIDR) | 0.0.0.0/0 | The IP address range that can HTTP to the EC2 instance (port: 80) |
| Primary Management Private Subnet CIDR (PrimaryManagementPrivateSubnetCIDR) | 10.0.1.0/24 | The CIDR block for Primary Management Subnet located in Availability Zone 1. |
| Primary Management Private IP (PrimaryManagementPrivateIP) | — | Private IP assigned to the Primary Management ENI (last octet has to be between 5 and 254) from the Primary Management Subnet CIDR. |
| Primary Client Public Subnet CIDR (PrimaryClientPublicSubnetCIDR) | 10.0.2.0/24 | The CIDR block for Primary Client Subnet located in Availability Zone 1. |
| Primary Client Private IP (PrimaryClientPrivateIP) | — | Private IP assigned to the Primary Client ENI (last octet has to be between 5 and 254) from Primary Client IP from the Primary Client Subnet CIDR. |
| Primary Server Private Subnet CIDR (PrimaryServerPrivateSubnetCIDR) | 10.0.3.0/24 | The CIDR block for Primary Server located in Availability Zone 1. |
| Primary Server Private IP (PrimaryServerPrivateIP) | — | Private IP assigned to the Primary Server ENI (last octet has to be between 5 and 254) from the Primary Server Subnet CIDR. |
| Secondary Management Private Subnet CIDR (SecondaryManagementPrivateSubnetCIDR) | 10.0.4.0/24 | The CIDR block for Secondary Management Subnet located in Availability Zone 2. |
| Secondary Management Private IP (SecondaryManagementPrivateIP) | — | Private IP assigned to the Secondary Management ENI (last octet has to be between 5 and 254). It would allocate Secondary Management IP from the Secondary Management Subnet CIDR. |
| Secondary Client Public Subnet CIDR (SecondaryClientPublicSubnetCIDR) | 10.0.5.0/24 | The CIDR block for Secondary Client Subnet located in Availability Zone 2. |
| Secondary Client Private IP (SecondaryClientPrivateIP) | — | Private IP assigned to the Secondary Client ENI (last octet has to be between 5 and 254). It would allocate Secondary Client IP from the Secondary Client Subnet CIDR. |
| Secondary Server Private Subnet CIDR (SecondaryServerPrivateSubnetCIDR) | 10.0.6.0/24 | The CIDR block for Secondary Server Subnet located in Availability Zone 2. |
| Secondary Server Private IP (SecondaryServerPrivateIP) | — | Private IP assigned to the Secondary Server ENI (last octet has to be between 5 and 254). It would allocate Secondary Server IP from the Secondary Server Subnet CIDR. |
VPC Tenancy attribute (VPCTenancy) |
default | The allowed tenancy of instances launched into the VPC. Choose Dedicated tenancy to launch EC2 instances dedicated to a single customer. |
Bastion host configuration
| Parameter label (name) | Default | Description |
|---|---|---|
| Bastion Host required (LinuxBastionHostEIP) | No | By default, no bastion host will be configured. But if users want to opt for sandbox deployment select “yes” from the menu which would deploy a Linux Bastion Host in the public subnet with an EIP that would give users access to the components in the private and public subnet. |
Citrix WAF Configuration
| Parameter label (name) | Default | Description |
|---|---|---|
| Key pair name (KeyPairName) | Requires input | A public/private key pair, which allows users to connect securely to the user instance after it launches. This is the key pair users created in their preferred AWS Region; see the Technical Requirements section. |
| Citrix ADC Instance Type (CitrixADCInstanceType) | m4.xlarge | The EC2 instance type to use for the ADC instances. Ensure that the instance type opted for aligns with the instance types available in the AWS marketplace or else the CFT might fail. |
| Citrix ADC AMI ID (CitrixADCImageID) | — | The AWS Marketplace AMI to be used for Citrix WAF deployment. This must match the AMI users subscribed to in step 2. |
Citrix ADC VPX IAM role (iam:GetRole) |
— | This Template: AWS-Quickstart/Quickstart-Citrix-ADC-VPX/Templates creates the IAM role and the Instance Profile required for Citrix ADC VPX. If left empty, CFT creates the required IAM role. |
| Client PublicIP(EIP) (ClientPublicEIP) | No | Select “Yes” if users want to assign a public EIP to the user Client Network interface. Otherwise, even after the deployment, users still have the option of assigning it later if necessary. |
Pooled Licensing configuration
| Parameter label (name) | Default | Description |
|---|---|---|
| ADM Pooled Licensing | No | If choosing the BYOL option for licensing, select yes from the list. This allows users to upload their already purchased licenses. |
| Before users begin, they should Configure Citrix ADC Pooled Capacity to ensure ADM pooled licensing is available, see: Configure Citrix ADC Pooled Capacity. | ||
| Reachable ADM / ADM Agent IP | Requires input | For the Customer Licensed option, whether users deploy Citrix ADM on-prem or an agent in the cloud, make sure to have a reachable ADM IP which would then be used as an input parameter. |
| Licensing Mode | Optional | Users can choose from the 3 licensing modes |
- Configure Citrix ADC Pooled Capacity: Configure Citrix ADC Pooled Capacity
- Citrix ADC VPX Check-in and Check-out Licensing (CICO): Citrix ADC VPX Check-in and Check-out Licensing * Citrix ADC virtual CPU Licensing: [Citrix ADC virtual CPU Licensing](https://docs.citrix.com/en-us/citrix-application-delivery-management-software/13/license-server/adc-virtual-cpu-licensing.html)| |**License Bandwidth in Mbps**|0 Mbps|Only if the licensing mode is Pooled-Licensing, then this field comes into the picture. It allocates an initial bandwidth of the license in Mbps to be allocated after BYOL ADCs are created. It should be a multiple of 10 Mbps.| |**License Edition**|Premium|License Edition for Pooled Capacity Licensing Mode is **Premium**| |**Appliance Platform Type**|Optional|Choose the required Appliance Platform Type, **only** if users opt for CICO licensing mode. Users get the options listed: VPX-200, VPX-1000, VPX-3000, VPX-5000, VPX-8000| |**License Edition**|Premium|License Edition for vCPU based Licensing is **Premium**.|
AWS Quick Start Guide Configuration
Note:
We recommend that users keep the default settings for the following two parameters, unless they are customizing the Quick Start Guide templates for their own deployment projects. Changing the settings of these parameters will automatically update code references to point to a new Quick Start Guide location. For more details, see the AWS Quick Start Guide Contributor’s Guide located here: AWS Quick Starts/Option 1 - Adopt a Quick Start.
| Parameter label (name) | Default | Description |
|---|---|---|
| Quick Start Guide S3 bucket name (QSS3BucketName) | aws-quickstart |
The S3 bucket users created for their copy of Quick Start Guide assets, if users decide to customize or extend the Quick Start Guide for their own use. The bucket name can include numbers, lowercase letters, uppercase letters, and hyphens, but should not start or end with a hyphen. |
| Quick Start Guide S3 key prefix (QSS3KeyPrefix) | quickstart-citrix-adc-vpx/ | The S3 key name prefix, from the Object Key and Metadata: Object Key and Metadata, is used to simulate a folder for the user copy of Quick Start Guide assets, if users decide to customize or extend the Quick Start Guide for their own use. This prefix can include numbers, lowercase letters, uppercase letters, hyphens, and forward slashes. |
-
On the Options page, users can specify a Resource Tag or key-value pair for resources in your stack and set advanced options. For more information on Resource Tags, see: Resource Tag. For more information on setting AWS CloudFormation Stack Options, see: Setting AWS CloudFormation Stack Options. When users are done, they should choose Next.
-
On the Review page, review and confirm the template settings. Under Capabilities, select the two check boxes to acknowledge that the template creates IAM resources and that it might require the capability to auto-expand macros.
-
Choose Create to deploy the stack.
-
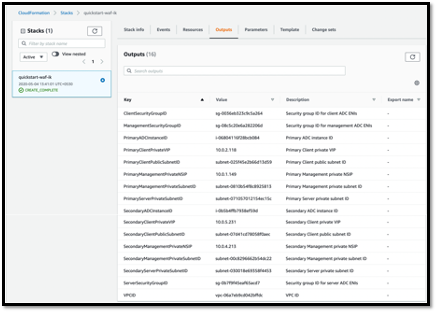
Monitor the status of the stack. When the status is CREATE_COMPLETE, the Citrix WAF instance is ready.
-
Use the URLs displayed in the Outputs tab for the stack to view the resources that were created.
Step 4: Test the Deployment
We refer to the instances in this deployment as primary and secondary. Each instance has different IP addresses associated with it. When the Quick Start has been deployed successfully, traffic goes through the primary Citrix WAF instance configured in Availability Zone 1. During failover conditions, when the primary instance does not respond to client requests, the secondary WAF instance takes over.
The Elastic IP address of the virtual IP address of the primary instance migrates to the secondary instance, which takes over as the new primary instance.
In the failover process, Citrix WAF does the following:
-
Citrix WAF checks the virtual servers that have IP sets attached to them.
-
Citrix WAF finds the IP address that has an associated public IP address from the two IP addresses that the virtual server is listening on. One that is directly attached to the virtual server, and one that is attached through the IP set.
-
Citrix WAF reassociates the public Elastic IP address to the private IP address that belongs to the new primary virtual IP address.
To validate the deployment, perform the following:
- Connect to the primary instance
For example, with a proxy server, jump host (a Linux/Windows/FW instance running in AWS, or the bastion host), or another device reachable to that VPC or a Direct Connect if dealing with on-prem connectivity.
- Perform a trigger action to force failover and check whether the secondary instance takes over.
Tip:
To further validate the configuration with respect to Citrix WAF, run the following command after connecting to the Primary Citrix WAF instance:
Sh appfw profile QS-Profile
Connect to Citrix WAF HA Pair using Bastion Host
If users are opting for Sandbox deployment (for example, as part of CFT, users opt for configuring a Bastion Host), a Linux bastion host deployed in a public subnet will be configured to access the WAF interfaces.
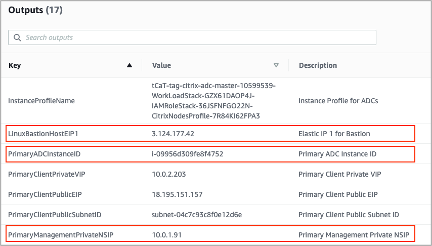
In the AWS CloudFormation console, which is accessed by signing in here: Sign in, choose the master stack, and on the Outputs tab, find the value of LinuxBastionHostEIP1.
-
PrivateManagementPrivateNSIP and PrimaryADCInstanceID key’s value to be used in the later steps to SSH into the ADC.
-
Choose Services.
-
On the Compute tab, select EC2.
-
Under Resources, choose Running Instances.
-
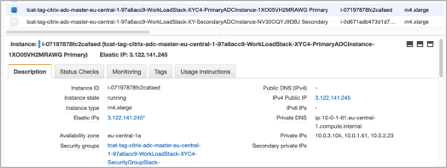
On the Description tab of the primary WAF instance, note the IPv4 public IP address. Users need that IP address to construct the SSH command.
-
- To store the key in the user keychain, run the command
ssh-add -K [your-key-pair].pem
On Linux, users might need to omit the -K flag.
- Log in to the bastion host using the following command, using the value for LinuxBastionHostEIP1 that users noted in step 1.
ssh -A ubuntu@[LinuxBastionHostEIP1]
- From the bastion host, users can connect to the primary WAF instance by using SSH.
ssh nsroot@[Primary Management Private NSIP]
Password: [Primary ADC Instance ID]
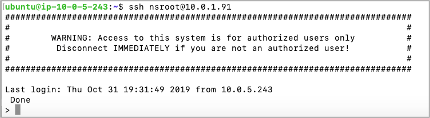
Now users are connected to the primary Citrix WAF instance. To see the available commands, users can run the help command. To view the current HA configuration, users can run the show HA node command.
Citrix Application Delivery Management
Citrix Application Delivery Management Service (Citrix ADM) provides an easy and scalable solution to manage Citrix ADC deployments that include Citrix ADC MPX, Citrix ADC VPX, Citrix Gateway, Citrix Secure Web Gateway™, Citrix ADC SDX, Citrix ADC CPX, and Citrix SD-WAN appliances that are deployed on-premises or on the cloud.
Users can use this cloud solution to manage, monitor, and troubleshoot the entire global application delivery infrastructure from a single, unified, and centralized cloud-based console. Citrix ADM Service provides all the capabilities required to quickly set up, deploy, and manage application delivery in Citrix ADC deployments and with rich analytics of application health, performance, and security.
Citrix ADM Service provides the following benefits:
-
Agile – Easy to operate, update, and consume. The service model of Citrix ADM Service is available over the cloud, making it easy to operate, update, and use the features provided by Citrix ADM Service. The frequency of updates, combined with the automated update feature, quickly enhances user Citrix ADC deployment.
-
Faster time to value – Quicker business goals achievement. Unlike with the traditional on-premises deployment, users can use their Citrix ADM Service with a few clicks. Users not only save the installation and configuration time, but also avoid wasting time and resources on potential errors.
-
Multi-Site Management – Single Pane of Glass for instances across Multi-Site data centers. With the Citrix ADM Service, users can manage and monitor Citrix ADCs that are in various types of deployments. Users have one-stop management for Citrix ADCs deployed on-premises and in the cloud.
-
Operational Efficiency – Optimized and automated way to achieve higher operational productivity. With the Citrix ADM Service, user operational costs are reduced by saving user time, money, and resources on maintaining and upgrading the traditional hardware deployments.
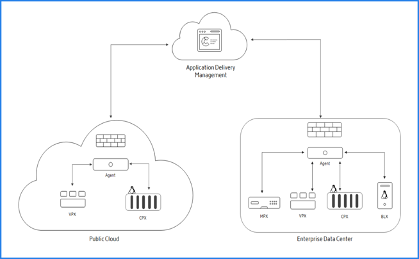
How Citrix ADM Service Works
Citrix ADM Service is available as a service on the Citrix Cloud. After users sign up for Citrix Cloud and start using the service, install agents in the user network environment or initiate the built-in agent in the instances. Then, add the instances users want to manage to the service.
An agent enables communication between the Citrix ADM Service and the managed instances in the user data center. The agent collects data from the managed instances in the user network and sends it to the Citrix ADM Service.
When users add an instance to the Citrix ADM Service, it implicitly adds itself as a trap destination and collects an inventory of the instance.
The service collects instance details such as:
-
Host name
-
Software version
-
Running and saved configuration
-
Certificates
-
Entities configured on the instance, and so on.
Citrix ADM Service periodically polls managed instances to collect information.
The following image illustrates the communication between the service, the agents, and the instances:
Documentation Guide
The Citrix ADM Service documentation includes information about how to get started with the service, a list of features supported on the service, and configuration specific to this service solution.
Deploying Citrix ADC VPX Instances on AWS using Citrix ADM
When customers move their applications to the cloud, the components that are part of their application increase, become more distributed, and need to be dynamically managed.
With Citrix ADC VPX instances on AWS, users can seamlessly extend their L4-L7 network stack to AWS. With Citrix ADC VPX, AWS becomes a natural extension of their on-premises IT infrastructure. Customers can use Citrix ADC VPX on AWS to combine the elasticity and flexibility of the cloud, with the same optimization, security, and control features that support the most demanding websites and applications in the world.
With Citrix Application Delivery Management (ADM) monitoring their Citrix ADC instances, users gain visibility into the health, performance, and security of their applications. They can automate the setup, deployment, and management of their application delivery infrastructure across hybrid multi-cloud environments.
Architecture Diagram
The following image provides an overview of how Citrix ADM connects with AWS to provision Citrix ADC VPX instances in AWS.
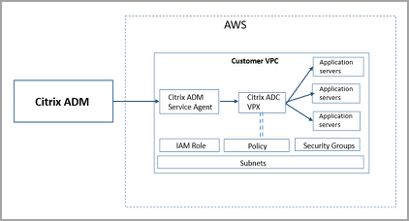
Configuration Tasks
Perform the following tasks on AWS before provisioning Citrix ADC VPX instances in Citrix ADM:
-
Create subnets
-
Create security groups
-
Create an IAM role and define a policy
Perform the following tasks on Citrix ADM to provision the instances on AWS:
-
Create site
-
Provision Citrix ADC VPX instance on AWS
To Create Subnets
Create three subnets in a VPC. The three subnets that are required to provision Citrix ADC VPX instances in a VPC - are management, client, and server. Specify an IPv4 CIDR block from the range that is defined in the VPC for each of the subnets. Specify the availability zone in which the subnet is to reside. Create all the three subnets in the same availability zone. The following image illustrates the three subnets created in the customer region and their connectivity to the client system.
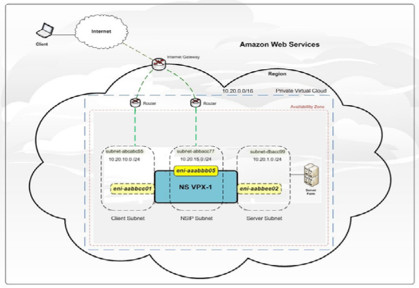
For more information on VPC and subnets, see VPCs and Subnets.
To Create Security Groups
Create a security group to control inbound and outbound traffic in the Citrix ADC VPX instance. A security group acts as a virtual firewall for a user instance. Create security groups at the instance level, and not at the subnet level. It is possible to assign each instance in a subnet in the user VPC to a different set of security groups. Add rules for each security group to control the inbound traffic that is passing through the client subnet to instances. Users can also add a separate set of rules that control the outbound traffic that passes through the server subnet to the application servers. Although users can use the default security group for their instances, they might want to create their own groups. Create three security groups - one for each subnet. Create rules for both incoming and outgoing traffic that users want to control. Users can add as many rules as they want.
For more information on security groups, see: Security Groups for your VPC.
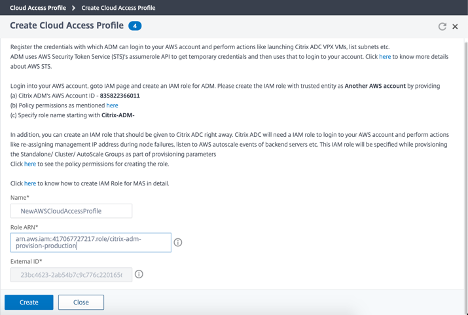
To Create an IAM Role and Define a Policy
Create an IAM role so that customers can establish a trust relationship between their users and the Citrix trusted AWS account and create a policy with Citrix permissions.
-
In AWS, click Services. In the left side navigation pane, select IAM > Roles, and click Create role.
-
Users are connecting their AWS account with the AWS account in Citrix ADM. So, select Another AWS account to allow Citrix ADM to perform actions in the AWS account.
Type in the 12-digit Citrix ADM AWS account ID. The Citrix ID is 835822366011. Users can also find the Citrix ID in Citrix ADM when they create the cloud access profile.
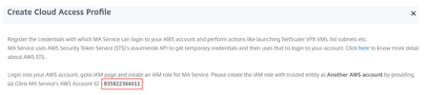
-
Enable Require external ID to connect to a third-party account. Users can increase the security of their roles by requiring an optional external identifier. Type an ID that can be a combination of any characters.
-
Click Permissions.
-
In Attach permissions policies page, click Create policy.
-
Users can create and edit a policy in the visual editor or by using JSON.
The list of permissions from Citrix is provided in the following box:
{
"Version": "2012-10-17",
"Statement":
[
{
"Effect": "Allow",
"Action": [
"ec2:DescribeInstances",
"ec2:DescribeImageAttribute",
"ec2:DescribeInstanceAttribute",
"ec2:DescribeRegions",
"ec2:DescribeDhcpOptions",
"ec2:DescribeSecurityGroups",
"ec2:DescribeHosts",
"ec2:DescribeImages",
"ec2:DescribeVpcs",
"ec2:DescribeSubnets",
"ec2:DescribeNetworkInterfaces",
"ec2:DescribeAvailabilityZones",
"ec2:DescribeNetworkInterfaceAttribute",
"ec2:DescribeInstanceStatus",
"ec2:DescribeAddresses",
"ec2:DescribeKeyPairs",
"ec2:DescribeTags",
"ec2:DescribeVolumeStatus",
"ec2:DescribeVolumes",
"ec2:DescribeVolumeAttribute",
"ec2:CreateTags",
"ec2:DeleteTags",
"ec2:CreateKeyPair",
"ec2:DeleteKeyPair",
"ec2:ResetInstanceAttribute",
"ec2:RunScheduledInstances",
"ec2:ReportInstanceStatus",
"ec2:StartInstances",
"ec2:RunInstances",
"ec2:StopInstances",
"ec2:UnmonitorInstances",
"ec2:MonitorInstances",
"ec2:RebootInstances",
"ec2:TerminateInstances",
"ec2:ModifyInstanceAttribute",
"ec2:AssignPrivateIpAddresses",
"ec2:UnassignPrivateIpAddresses",
"ec2:CreateNetworkInterface",
"ec2:AttachNetworkInterface",
"ec2:DetachNetworkInterface",
"ec2:DeleteNetworkInterface",
"ec2:ResetNetworkInterfaceAttribute",
"ec2:ModifyNetworkInterfaceAttribute",
"ec2:AssociateAddress",
"ec2:AllocateAddress",
"ec2:ReleaseAddress",
"ec2:DisassociateAddress",
"ec2:GetConsoleOutput"
],
"Resource": "*"
}
]
}
<!--NeedCopy-->
-
Copy and paste the list of permissions in the JSON tab and click Review policy.
-
In the Review policy page, type a name for the policy, enter a description, and click Create policy.
To Create a Site in Citrix ADM
Create a site in Citrix ADM and add the details of the VPC associated with the AWS role.
-
In Citrix ADM, navigate to Networks > Sites.
-
Click Add.
-
Select the service type as AWS and enable Use existing VPC as a site.
-
Select the cloud access profile.
-
If the cloud access profile does not exist in the field, click Add to create a profile.
-
In the Create Cloud Access Profile page, type the name of the profile with which users want to access AWS.
-
Type the ARN associated with the role that users have created in AWS.
-
Type the external ID that users provided while creating an Identity and Access Management (IAM) role in AWS. See step 4 in “To create an IAM role and define a policy” task. Ensure that the IAM role name specified in AWS starts with
Citrix-ADM-and it correctly appears in the Role ARN.
-
The details of the VPC, such as the region, VPC ID, name and CIDR block, associated with your IAM role in AWS are imported in Citrix ADM.
-
Type a name for the site.
-
Click Create.
To Provision Citrix ADC VPX on AWS
Use the site that users created earlier to provision the Citrix ADC VPX instances on AWS. Provide Citrix ADM service agent details to provision those instances that are bound to that agent.
-
In Citrix ADM, navigate to Networks > Instances > Citrix ADC.
-
In the VPX tab, click Provision.
This option displays the Provision Citrix ADC VPX on Cloud page.
-
Select Amazon Web Services (AWS) and click Next.
-
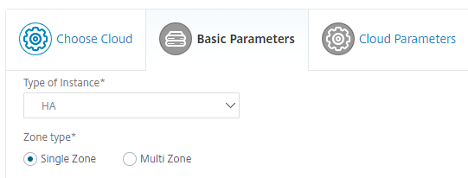
In Basic Parameters,
-
Select the Type of Instance from the list.
-
Standalone: This option provisions a standalone Citrix ADC VPX instance on AWS.
-
HA: This option provisions the high availability Citrix ADC VPX instances on AWS.
To provision the Citrix ADC VPX instances in the same zone, select the Single Zone option under Zone Type.
To provision the Citrix ADC VPX instances across multiple zones, select the Multi Zone option under Zone type. In the Cloud Parameters tab, make sure to specify the network details for each zone that is created on AWS.
-
-
Specify the name of the Citrix ADC VPX instance.
-
In Site, select the site that you created earlier.
-
In Agent, select the agent that is created to manage the Citrix ADC VPX instance.
-
In Cloud Access Profile, select the cloud access profile created during site creation.
-
In Device Profile, select the profile to provide authentication.
Citrix ADM uses the device profile when it requires to log on to the Citrix ADC VPX instance.
- Click Next.
-
-
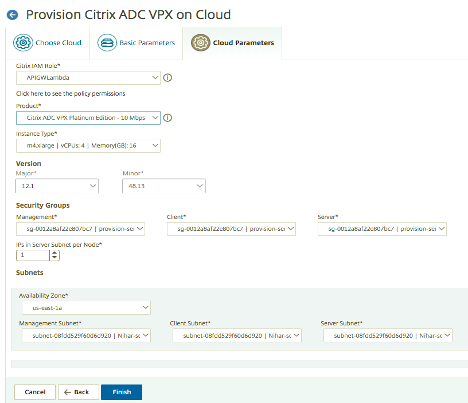
In Cloud Parameters,
-
Select the Citrix IAM Role created in AWS. An IAM role is an AWS identity with permission policies that determine what the identity can and cannot do in AWS.
-
In the Product field, select the Citrix ADC product version that users want to provision.
-
Select the EC2 instance type from the Instance Type list.
-
Select the Version of Citrix ADC that users want to provision. Select both Major and Minor version of Citrix ADC.
-
In Security Groups, select the Management, Client, and Server security groups that users created in their virtual network.
-
In IPs in server Subnet per Node, select the number of IP addresses in server subnet per node for the security group.
-
In Subnets, select the Management, Client, and Server subnets for each zone that are created in AWS. Users can also select the region from the Availability Zone list.
-
Click Finish.
-
The Citrix ADC VPX instance is now provisioned on AWS.
Note:
Citrix ADM doesn’t support deprovisioning of Citrix ADC instances from AWS.
To View the Citrix ADC VPX Provisioned in AWS
-
From the AWS home page, navigate to Services and click EC2.
-
On the Resources page, click Running Instances.
-
Users can view the Citrix ADC VPX provisioned in AWS.
The name of the Citrix ADC VPX instance is the same name users provided while provisioning the instance in Citrix ADM.
To View the Citrix ADC VPX Provisioned in Citrix ADM
-
In Citrix ADM, navigate to Networks > Instances > Citrix ADC.
-
Select Citrix ADC VPX tab.
-
The Citrix ADC VPX instance provisioned in AWS is listed here.
Citrix ADC WAF and OWASP Top 10 – 2017
The Open Web Application Security Project: OWASP released the OWASP Top 10 for 2017 for web application security. This list documents the most common web application vulnerabilities and is a great starting point to evaluate web security. Here we detail how to configure the Citrix ADC Web Application Firewall (WAF) to mitigate these flaws. WAF is available as an integrated module in the Citrix ADC (Premium Edition) as well as a complete range of appliances.
The full OWASP Top 10 document is available at OWASP Top Ten.
| OWASP Top-10 2017 | Citrix ADC WAF Features |
|---|---|
| A1:2017- Injection | Injection attack prevention (SQL or any other custom injections such as OS Command injection, XPath injection, and LDAP Injection), auto update signature feature |
| A2:2017 - Broken Authentication | Citrix ADC AAA, Cookie Tampering protection, Cookie Proxying, Cookie Encryption, CSRF tagging, Use SSL |
| A3:2017 - Sensitive Data Exposure | Credit Card protection, Safe Commerce, Cookie proxying, and Cookie Encryption |
| A4:2017 XML External Entities (XXE) | XML protection including WSI checks, XML message validation & XML SOAP fault filtering check |
| A5:2017 Broken Access Control | Citrix ADC AAA, Authorization security feature within Citrix ADC AAA module of NetScaler, Form protections, and Cookie tampering protections, StartURL, and ClosureURL |
| A6:2017 - Security Misconfiguration | PCI reports, SSL features, Signature generation from vulnerability scan reports such as Cenznic, Qualys, AppScan, WebInspect, Whitehat. Also, specific protections such as Cookie encryption, proxying, and tampering |
| A7:2017 - Cross Site Scripting (XSS) | XSS Attack Prevention, Blocks all OWASP XSS cheat sheet attacks |
| A8:2017 – Insecure Deserialization | XML Security Checks, GWT content type, custom signatures, Xpath for JSON and XML |
| A9:2017 - Using Components with known Vulnerabilities | Vulnerability scan reports, Application Firewall Templates, and Custom Signatures |
| A10:2017 – Insufficient Logging & Monitoring | User configurable custom logging, Citrix ADC Management and Analytics System |
A1:2017- Injection
Injection flaws, such as SQL, NoSQL, OS, and LDAP injection, occur when untrusted data is sent to an interpreter as part of a command or query. The attacker’s hostile data can trick the interpreter into running unintended commands or accessing data without proper authorization.
ADC WAF Protections
-
SQL Injection prevention feature protects against common injection attacks. Custom injection patterns can be uploaded to protect against any type of injection attack including XPath and LDAP. This is applicable for both HTML and XML payloads.
-
The auto update signature feature keeps the injection signatures up to date.
-
Field format protection feature allows the administrator to restrict any user parameter to a regular expression. For instance, you can enforce that a zip-code field contains integers only or even 5-digit integers.
-
Form field consistency: Validate each submitted user form against the user session form signature to ensure the validity of all form elements.
-
Buffer overflow checks ensure that the URL, headers, and cookies are in the right limits blocking any attempts to inject large scripts or code.
A2:2017 – Broken Authentication
Application functions related to authentication and session management are often implemented incorrectly, allowing attackers to compromise passwords, keys, or session tokens, or to exploit other implementation flaws to assume other users’ identities temporarily or permanently.
ADC WAF Protections
-
Citrix ADC AAA module performs user authentication and provides Single Sign-On functionality to back end applications. This is integrated into the Citrix ADC AppExpert policy engine to allow custom policies based on user and group information.
-
Using SSL offloading and URL transformation capabilities, the firewall can also help sites to use secure transport layer protocols to prevent stealing of session tokens by network sniffing.
-
Cookie Proxying and Cookie Encryption can be employed to completely mitigate cookie stealing.
A3:2017 - Sensitive Data Exposure
Many web applications and APIs do not properly protect sensitive data, such as financial, healthcare, and PII. Attackers may steal or modify such poorly protected data to conduct credit card fraud, identity theft, or other crimes. Sensitive data may be compromised without extra protection, such as encryption at rest or in transit, and requires special precautions when exchanged with the browser.
ADC WAF Protections
-
Application Firewall protects applications from leaking sensitive data like credit card details.
-
Sensitive data can be configured as Safe objects in Safe Commerce protection to avoid exposure.
-
Any sensitive data in cookies can be protected by Cookie Proxying and Cookie Encryption.
A4:2017 XML External Entities (XXE)
Many older or poorly configured XML processors evaluate external entity references within XML documents. External entities can be used to disclose internal files using the file URI handler, internal file shares, internal port scanning, remote code execution, and denial of service attacks.
ADC WAF Protections
-
In addition to detecting and blocking common application threats that can be adapted for attacking XML-based applications (that is, cross-site scripting, command injection, and so forth).
-
ADC Application Firewall includes a rich set of XML-specific security protections. These include schema validation to thoroughly verify SOAP messages and XML payloads, and a powerful XML attachment check to block attachments containing malicious executables or viruses.
-
Automatic traffic inspection methods block XPath injection attacks on URLs and forms aimed at gaining access.
-
ADC Application Firewall also thwarts various DoS attacks, including external entity references, recursive expansion, excessive nesting, and malicious messages containing either long or a large number of attributes and elements.
A5:2017 Broken Access Control
Restrictions on what authenticated users are allowed to do are often not properly enforced. Attackers can exploit these flaws to access unauthorized functionality and data, such as access other users’ accounts, view sensitive files, modify other users’ data, change access rights, and so on.
ADC WAF Protections
-
Citrix ADC AAA feature that supports authentication, authorization, and auditing for all application traffic allows a site administrator to manage access controls with the ADC appliance.
-
The Authorization security feature within the Citrix ADC AAA module of the ADC appliance enables the appliance to verify, which content on a protected server it should allow each user to access.
-
Form field consistency: If object references are stored as hidden fields in forms, then using form field consistency you can validate that these fields are not tampered on subsequent requests.
-
Cookie Proxying and Cookie consistency: Object references that are stored in cookie values can be validated with these protections.
-
Start URL check with URL closure: Allows user access to a predefined allow list of URLs. URL closure builds a list of all URLs seen in valid responses during the user session and automatically allows access to them during that session.
A6:2017 - Security Misconfiguration
Security misconfiguration is the most commonly seen issue. This is commonly a result of insecure default configurations, incomplete or improvised configurations, open cloud storage, misconfigured HTTP headers, and verbose error messages containing sensitive information. Not only must all operating systems, frameworks, libraries, and applications be securely configured, but they must be patched and upgraded in a timely fashion.
ADC WAF Protections
-
The PCI-DSS report generated by the Application Firewall, documents the security settings on the Firewall device.
-
Reports from the scanning tools are converted to ADC WAF Signatures to handle security misconfigurations.
-
ADC WAF supports Cenzic, IBM AppScan (Enterprise and Standard), Qualys, TrendMicro, WhiteHat, and custom vulnerability scan reports.
A7:2017 - Cross Site Scripting (XSS)
XSS flaws occur whenever an application includes untrusted data in a new web page without proper validation or escaping, or updates an existing webpage with user-supplied data using a browser API that can create HTML or JavaScript. Cross-site scripting allows attackers to run scripts in the victim’s browser which can hijack user sessions, deface websites, or redirect the user to malicious sites.
ADC WAF Protections
-
Cross-site scripting protection protects against common XSS attacks. Custom XSS patterns can be uploaded to modify the default list of allowed tags and attributes. The ADC WAF uses an allow list of allowed HTML attributes and tags to detect XSS attacks. This is applicable for both HTML and XML payloads.
-
ADC WAF blocks all the attacks listed in the OWASP XSS Filter Evaluation Cheat Sheet.
-
Field format check prevents an attacker from sending inappropriate web form data which can be a potential XSS attack.
-
Form field consistency.
A8:2017 - Insecure Deserialization
Insecure deserialization often leads to remote code execution. Even if deserialization flaws do not result in remote code execution, they can be used to perform attacks, including replay attacks, injection attacks, and privilege escalation attacks.
ADC WAF Protections
-
JSON payload inspection with custom signatures.
-
XML security: protects against XML denial of service (xDoS), XML SQL and Xpath injection and cross site scripting, format checks, WS-I basic profile compliance, XML attachments check.
-
Field Format checks in addition to Cookie Consistency and Field Consistency can be used.
A9:2017 - Using Components with Known Vulnerabilities
Components, such as libraries, frameworks, and other software modules, run with the same privileges as the application. If a vulnerable component is exploited, such an attack can facilitate serious data loss or server takeover. Applications and APIs using components with known vulnerabilities may undermine application defenses and enable various attacks and impacts.
ADC WAF Protections
-
Citrix recommends having the third-party components up to date.
-
Vulnerability scan reports that are converted to ADC Signatures can be used to virtually patch these components.
-
Application Firewall templates that are available for these vulnerable components can be used.
-
Custom Signatures can be bound with the firewall to protect these components.
A10:2017 - Insufficient Logging & Monitoring
Insufficient logging and monitoring, coupled with missing or ineffective integration with incident response, allows attackers to further attack systems, maintain persistence, pivot to more systems, and tamper, extract, or destroy data. Most breach studies show that the time to detect a breach is over 200 days, typically detected by external parties rather than internal processes or monitoring.
ADC WAF Protections
-
When the log action is enabled for security checks or signatures, the resulting log messages provide information about the requests and responses that the application firewall has observed while protecting your websites and applications.
-
The application firewall offers the convenience of using the built-in ADC database for identifying the locations corresponding to the IP addresses from which malicious requests are originating.
-
Default format (PI) expressions give the flexibility to customize the information included in the logs with the option to add the specific data to capture in the application firewall generated log messages.
-
The application firewall supports CEF logs.
Application Security Protection
Citrix ADM
Citrix Application Delivery Management Service (Citrix ADM) provides a scalable solution to manage Citrix ADC deployments that include Citrix ADC MPX, Citrix ADC VPX, Citrix Gateway, Citrix Secure Web™ Gateway, Citrix ADC SDX, Citrix ADC CPX, and Citrix SD-WAN appliances that are deployed on-premises or on the cloud.
Citrix ADM Application Analytics and Management Features
The following features are key to the ADM role in App Security.
Application Analytics and Management
The Application Analytics and Management feature of Citrix ADM strengthens the application-centric approach to help users address various application delivery challenges. This approach gives users visibility into the health scores of applications, helps users determine the security risks, and helps users detect anomalies in the application traffic flows and take corrective actions. The most important among these roles for App Security is Application Security Analytics:
- Application security analytics: Application Security Analytics. The App Security Dashboard provides a holistic view of the security status of user applications. For example, it shows key security metrics such as security violations, signature violations, threat indexes. The App Security dashboard also displays attack related information such as SYN attacks, small window attacks, and DNS flood attacks for the discovered Citrix ADC instances.
StyleBooks
StyleBooks simplify the task of managing complex Citrix ADC configurations for user applications. A StyleBook is a template that users can use to create and manage Citrix ADC configurations. Here users are primarily concerned with the StyleBook used to deploy the Web Application Firewall. For more information on StyleBooks, see: StyleBooks.
Analytics
Provides an easy and scalable way to look into the various insights of the Citrix ADC instances’ data to describe, predict, and improve application performance. Users can use one or more analytics features simultaneously. Most important among these roles for App Security are:
-
Security Insight: Security Insight. Provides a single-pane solution to help users assess user application security status and take corrective actions to secure user applications.
-
Bot Insight
-
For more information on analytics, see Analytics: Analytics.
Other features that are important to ADM functionality are:
Event Management
Events represent occurrences of events or errors on a managed Citrix ADC instance. For example, when there is a system failure or change in configuration, an event is generated and recorded on Citrix ADM. Following are the related features that users can configure or view by using Citrix ADM:
-
Creating event rules: Create Event Rules
-
View and export syslog messages: View and Export Syslog Messages
For more information on event management, see: Events.
Instance Management
Enables users to manage the Citrix ADC, Citrix Gateway, Citrix Secure Web Gateway, and Citrix SD-WAN instances. For more information on instance management, see: Adding Instances.
License Management
Allows users to manage Citrix ADC licenses by configuring Citrix ADM as a license manager.
-
Citrix ADC pooled capacity: Pooled Capacity. A common license pool from which a user Citrix ADC instance can check out one instance license and only as much bandwidth as it needs. When the instance no longer requires these resources, it checks them back in to the common pool, making the resources available to other instances that need them.
-
Citrix ADC VPX check-in and check-out licensing: Citrix ADC VPX Check-in and Check-out Licensing. Citrix ADM allocates licenses to Citrix ADC VPX instances on demand. A Citrix ADC VPX instance can check out the license from the Citrix ADM when a Citrix ADC VPX instance is provisioned, or check back in its license to Citrix ADM when an instance is removed or destroyed.
-
For more information on license management, see: Pooled Capacity.
Configuration Management
Citrix ADM allows users to create configuration jobs that help them perform configuration tasks, such as creating entities, configuring features, replication of configuration changes, system upgrades, and other maintenance activities with ease on multiple instances. Configuration jobs and templates simplify the most repetitive administrative tasks to a single task on Citrix ADM. For more information on configuration management, see Configuration jobs: Configuration Jobs.
Configuration Audit
Enables users to monitor and identify anomalies in the configurations across user instances.
-
Configuration advice: Get Configuration Advice on Network Configuration. Allows users to identify any configuration anomaly.
-
Audit template: Create Audit Templates. Allows users to monitor the changes across a specific configuration.
-
For more information on configuration audit, see: Configuration Audit.
Signatures provide the following deployment options to help users to optimize the protection of user applications:
-
Negative Security Model: With the negative security model, users employ a rich set of preconfigured signature rules to apply the power of pattern matching to detect attacks and protect against application vulnerabilities. Users block only what they don’t want and allow the rest. Users can add their own signature rules, based on the specific security needs of user applications, to design their own customized security solutions.
-
Hybrid security Model: In addition to using signatures, users can use positive security checks to create a configuration ideally suited for user applications. Use signatures to block what users don’t want, and use positive security checks to enforce what is allowed.
To protect user applications by using signatures, users must configure one or more profiles to use their signatures object. In a hybrid security configuration, the SQL injection and cross-site scripting patterns, and the SQL transformation rules, in the user signatures object are used not only by the signature rules, but also by the positive security checks configured in the Web Application Firewall profile that is using the signatures object.
The Web Application Firewall examines the traffic to user protected websites and web services to detect traffic that matches a signature. A match is triggered only when every pattern in the rule matches the traffic. When a match occurs, the specified actions for the rule are invoked. Users can display an error page or error object when a request is blocked. Log messages can help users to identify attacks being launched against user applications. If users enable statistics, the Web Application Firewall maintains data about requests that match a Web Application Firewall signature or security check.
If the traffic matches both a signature and a positive security check, the more restrictive of the two actions are enforced. For example, if a request matches a signature rule for which the block action is disabled, but the request also matches an SQL Injection positive security check for which the action is block, the request is blocked. In this case, the signature violation might be logged as [not blocked], although the request is blocked by the SQL injection check.
Customization: If necessary, users can add their own rules to a signatures object. Users can also customize the SQL/XSS patterns. The option to add their own signature rules, based on the specific security needs of user applications, gives users the flexibility to design their own customized security solutions. Users block only what they don’t want and allow the rest. A specific fast-match pattern in a specified location can significantly reduce processing overhead to optimize performance. Users can add, modify, or remove SQL injection and cross-site scripting patterns. Built-in RegEx and expression editors help users configure user patterns and verify their accuracy.
Use Cases
Compared to alternative solutions that require each service to be deployed as a separate virtual appliance, Citrix ADC on AWS combines L4 load balancing, L7 traffic management, server offload, application acceleration, application security, flexible licensing, and other essential application delivery capabilities in a single VPX instance, conveniently available via the AWS Marketplace. Furthermore, everything is governed by a single policy framework and managed with the same, powerful set of tools used to administer on-premises Citrix ADC deployments. The net result is that Citrix ADC on AWS enables several compelling use cases that not only support the immediate needs of today’s enterprises, but also the ongoing evolution from legacy computing infrastructures to enterprise cloud data centers.
Citrix Web Application Firewall (WAF)
Citrix Web Application Firewall (WAF) is an enterprise grade solution offering state of the art protections for modern applications. Citrix WAF mitigates threats against public-facing assets, including websites, web applications, and APIs. Citrix WAF includes IP reputation-based filtering, Bot mitigation, OWASP Top 10 application threats protections, Layer 7 DDoS protection and more. Also included are options to enforce authentication, strong SSL/TLS ciphers, TLS 1.3, rate limiting and rewrite policies. Using both basic and advanced WAF protections, Citrix WAF provides comprehensive protection for your applications with unparalleled ease of use. Getting up and running is a matter of minutes. Further, using an automated learning model, called dynamic profiling, Citrix WAF saves users precious time. By automatically learning how a protected application works, Citrix WAF adapts to the application even as developers deploy and alter the applications. Citrix WAF helps with compliance for all major regulatory standards and bodies, including PCI-DSS, HIPAA, and more. With our CloudFormation templates, it has never been easier to get up and running quickly. With auto scaling, users can rest assured that their applications remain protected even as their traffic scales up.
Web Application Firewall Deployment Strategy
The first step to deploying the web application firewall is to evaluate which applications or specific data need maximum security protection, which ones are less vulnerable, and the ones for which security inspection can safely be bypassed. This helps users in coming up with an optimal configuration, and in designing appropriate policies and bind points to segregate the traffic. For example, users might want to configure a policy to bypass security inspection of requests for static web content, such as images, MP3 files, and movies, and configure another policy to apply advanced security checks to requests for dynamic content. Users can use multiple policies and profiles to protect different contents of the same application.
The next step is to baseline the deployment. Start by creating a virtual server and run test traffic through it to get an idea of the rate and amount of traffic flowing through the user system.
Then, deploy the Web Application Firewall. Use Citrix ADM and the Web Application Firewall StyleBook to configure the Web Application Firewall. See the StyleBook section below in this guide for details.
After the Web Application Firewall is deployed and configured with the Web Application Firewall StyleBook, a useful next step would be to implement the Citrix ADC WAF and OWASP Top 10.
Finally, three of the Web Application Firewall protections are especially effective against common types of Web attacks, and are therefore more commonly used than any of the others. Thus, they should be implemented in the initial deployment. They are:
-
HTML Cross-Site Scripting. Examines requests and responses for scripts that attempt to access or modify content on a different website than the one on which the script is located. When this check finds such a script, it either renders the script harmless before forwarding the request or response to its destination, or it blocks the connection.
-
HTML SQL Injection. Examines requests that contain form field data for attempts to inject SQL commands into a SQL database. When this check detects injected SQL code, it either blocks the request or renders the injected SQL code harmless before forwarding the request to the Web server.
Note:
If both of the following conditions apply to the user configuration, users should make certain that your Web Application Firewall is correctly configured:
If users enable the HTML Cross-Site Scripting check or the HTML SQL Injection check (or both), and
User protected websites accept file uploads or contain Web forms that can contain large POST body data.
For more information about configuring the Web Application Firewall to handle this case, see Configuring the Application Firewall: Configuring the Web App Firewall.
- Buffer Overflow. Examines requests to detect attempts to cause a buffer overflow on the Web server.
Configuring the Web Application Firewall (WAF)
The following steps assume that the WAF is already enabled and functioning correctly.
Citrix recommends that users configure WAF using the Web Application Firewall StyleBook. Most users find it the easiest method to configure the Web Application Firewall, and it is designed to prevent mistakes. Both the GUI and the command line interface are intended for experienced users, primarily to modify an existing configuration or use advanced options.
SQL Injection
The Application Firewall HTML SQL Injection check provides special defenses against the injection of unauthorized SQL code that might break user Application security. Citrix Web Application Firewall examines the request payload for injected SQL code in three locations: 1) POST body, 2) headers, and 3) cookies.
A default set of keywords and special characters provides known keywords and special characters that are commonly used to launch SQL attacks. Users can also add new patterns, and they can edit the default set to customize the SQL check inspection.
There are several parameters that can be configured for SQL injection processing. Users can check for SQL wildcard characters. Users can change the SQL Injection type and select one of the 4 options (SQLKeyword, SQLSplChar, SQLSplCharANDKeyword, SQLSplCharORKeyword) to indicate how to evaluate the SQL keywords and SQL special characters when processing the payload. The SQL Comments Handling parameter gives users an option to specify the type of comments that need to be inspected or exempted during SQL Injection detection.
Users can deploy relaxations to avoid false positives. The learning engine can provide recommendations for configuring relaxation rules.
The following options are available for configuring an optimized SQL Injection protection for the user application:
Block — If users enable block, the block action is triggered only if the input matches the SQL injection type specification. For example, if SQLSplCharANDKeyword is configured as the SQL injection type, a request is not blocked if it contains no key words, even if SQL special characters are detected in the input. Such a request is blocked if the SQL injection type is set to either SQLSplChar, or SQLSplCharORKeyword.
Log — If users enable the log feature, the SQL Injection check generates log messages indicating the actions that it takes. If block is disabled, a separate log message is generated for each input field in which the SQL violation was detected. However, only one message is generated when the request is blocked. Similarly, 1 log message per request is generated for the transform operation, even when SQL special characters are transformed in multiple fields. Users can monitor the logs to determine whether responses to legitimate requests are getting blocked. A large increase in the number of log messages can indicate attempts to launch an attack.
Stats — If enabled, the stats feature gathers statistics about violations and logs. An unexpected surge in the stats counter might indicate that the user application is under attack. If legitimate requests are getting blocked, users might have to revisit the configuration to see if they need to configure new relaxation rules or modify the existing ones.
Learn — If users are not sure which SQL relaxation rules might be ideally suited for their applications, they can use the learn feature to generate recommendations based on the learned data. The Web Application Firewall learning engine monitors the traffic and provides SQL learning recommendations based on the observed values. To get optimal benefit without compromising performance, users might want to enable the learn option for a short time to get a representative sample of the rules, and then deploy the rules and disable learning.
Transform SQL special characters—The Web Application Firewall considers three characters, Single straight quote (‘), Backslash (), and Semicolon (;) as special characters for SQL security check processing. The SQL Transformation feature modifies the SQL Injection code in an HTML request to ensure that the request is rendered harmless. The modified HTML request is then sent to the server. All default transformation rules are specified in the /netscaler/default_custom_settings.xml file.
-
The transform operation renders the SQL code inactive by making the following changes to the request:
-
Single straight quote (‘) to double straight quote (“).
-
Backslash () to double backslash ().
-
Semicolon (;) is dropped completely.
These three characters (special strings) are necessary to issue commands to a SQL server. Unless a SQL command is prefaced with a special string, most SQL servers ignore that command. Therefore, the changes that the Web Application Firewall performs when transformation is enabled prevent an attacker from injecting active SQL. After these changes are made, the request can safely be forwarded to the user protected website. When web forms on the user protected website can legitimately contain SQL special strings, but the web forms do not rely on the special strings to operate correctly, users can disable blocking and enable transformation to prevent blocking of legitimate web form data without reducing the protection that the Web Application Firewall provides to the user protected websites.
The transform operation works independently of the SQL Injection Type setting. If transform is enabled and the SQL Injection type is specified as a SQL keyword, SQL special characters are transformed even if the request does not contain any keywords.
Tip:
Users normally enable either transformation or blocking, but not both. If the block action is enabled, it takes precedence over the transform action. If users have blocking enabled, enabling transformation is redundant.
Check for SQL Wildcard Characters—Wild card characters can be used to broaden the selections of a SQL (SQL-SELECT) statement. These wild card operators can be used with LIKE and NOT LIKE operators to compare a value to similar values. The percent (%), and underscore (_) characters are frequently used as wild cards. The percent sign is analogous to the asterisk (*) wildcard character used with MS-DOS and to match zero, one, or multiple characters in a field. The underscore is similar to the MS-DOS question mark (?) wildcard character. It matches a single number or character in an expression.
For example, users can use the following query to do a string search to find all customers whose names contain the D character.
SELECT * from customer WHERE name like “%D%”:
The following example combines the operators to find any salary values that have 0 in the second and third place.
SELECT * from customer WHERE salary like ‘_00%’:
Different DBMS vendors have extended the wildcard characters by adding extra operators. The Citrix Web Application Firewall can protect against attacks that are launched by injecting these wildcard characters. The 5 default Wildcard characters are percent (%), underscore (_), caret (^), opening bracket ([), and closing bracket (]). This protection applies to both HTML and XML profiles.
The default wildcard chars are a list of literals specified in the *Default Signatures:
-
<wildchar type=” LITERAL”>%</wildchar>
-
<wildchar type=”LITERAL”]>_</wildchar>
-
<wildchar type=”LITERAL”>^</wildchar>
-
<wildchar type=”LITERAL”>[</wildchar>
-
<wildchar type=”LITERAL”>]</wildchar>
Wildcard characters in an attack can be PCRE, like [^A-F]. The Web Application Firewall also supports PCRE wildcards, but the literal wildcard chars shown here are sufficient to block most attacks.
Note:
The SQL wildcard character check is different from the SQL special character check. This option must be used with caution to avoid false positives.
Check Request Containing SQL Injection Type—The Web Application Firewall provides 4 options to implement the desired level of strictness for SQL Injection inspection, based on the individual need of the application. The request is checked against the injection type specification for detecting SQL violations. The 4 SQL injection type options are:
-
SQL Special Character and Keyword—Both a SQL keyword and a SQL special character must be present in the input to trigger a SQL violation. This least restrictive setting is also the default setting.
-
SQL Special Character—At least one of the special characters must be present in the input to trigger a SQL violation.
-
SQL key word—At least one of the specified SQL keywords must be present in the input to trigger a SQL violation. Do not select this option without due consideration. To avoid false positives, make sure that none of the keywords are expected in the inputs.
-
SQL Special Character or Keyword—Either the key word or the special character string must be present in the input to trigger the security check violation.
Tip:
If users configure the Web Application Firewall to check for inputs that contain a SQL special character, the Web Application Firewall skips web form fields that do not contain any special characters. Since most SQL servers do not process SQL commands that are not preceded by a special character, enabling this option can significantly reduce the load on the Web Application Firewall and speed up processing without placing the user protected websites at risk.
SQL comments handling — By default, the Web Application Firewall checks all SQL comments for injected SQL commands. Many SQL servers ignore anything in a comment, however, even if preceded by an SQL special character. For faster processing, if your SQL server ignores comments, you can configure the Web Application Firewall to skip comments when examining requests for injected SQL. The SQL comments handling options are:
-
ANSI — Skip ANSI-format SQL comments, which are normally used by UNIX-based SQL databases. For example:
-
/– (Two Hyphens) - This is a comment that begins with two hyphens and ends with end of line.
-
{} - Braces (Braces enclose the comment. The { precedes the comment, and the } follows it. Braces can delimit single- or multiple-line comments, but comments cannot be nested)
-
/*/: C style comments (Does not allow nested comments). Please note /! <comment that begins with a slash followed by an asterisk and an exclamation mark is not a comment > */
-
MySQL Server supports some variants of C-style comments. These enable users to write code that includes MySQL extensions, but is still portable, by using comments of the following form: [/*! MySQL-specific code */]
-
.#: Mysql comments : This is a comment that begins with the # character and ends with an end of the line
-
-
Nested — Skip nested SQL comments, which are normally used by Microsoft SQL Server. For example; – (Two Hyphens), and /**/ (Allows nested comments)
-
ANSI/Nested — Skip comments that adhere to both the ANSI and nested SQL comment standards. Comments that match only the ANSI standard, or only the nested standard, are still checked for injected SQL.
-
Check all Comments — Check the entire request for injected SQL without skipping anything. This is the default setting.
Tip:
In most cases, users should not choose the Nested or the ANSI/Nested option unless their back-end database runs on Microsoft SQL Server. Most other types of SQL server software do not recognize nested comments. If nested comments appear in a request directed to another type of SQL server, they might indicate an attempt to breach security on that server.
Check Request headers — Enable this option if, in addition to examining the input in the form fields, users want to examine the request headers for HTML SQL Injection attacks. If users use the GUI, they can enable this parameter in the Advanced Settings -> Profile Settings pane of the Web Application Firewall profile.
Note:
If users enable the Check Request header flag, they might have to configure a relaxation rule for the User-Agent header. Presence of the SQL keyword like and a SQL special character semi-colon (;) might trigger false positive and block requests that contain this header. Warning: If users enable both request header checking and transformation, any SQL special characters found in headers are also transformed. The Accept, Accept-Charset, Accept-Encoding, Accept-Language, Expect, and User-Agent headers normally contain semicolons (;). Enabling both Request header checking and transformation simultaneously might cause errors.
InspectQueryContentTypes — Configure this option if users want to examine the request query portion for SQL Injection attacks for the specific content-types. If users use the GUI, they can configure this parameter in the Advanced Settings -> Profile Settings pane of the Application Firewall profile.
Cross-Site Scripting
The HTML Cross-Site Scripting (cross-site scripting) check examines both the headers and the POST bodies of user requests for possible cross-site scripting attacks. If it finds a cross-site script, it either modifies (transforms) the request to render the attack harmless, or blocks the request.
Note:
The HTML Cross-Site Scripting (cross-site scripting) check works only for content type, content length, and so forth. It does not work for cookie. Also ensure to have the ‘checkRequestHeaders’ option enabled in the user Web Application Firewall profile.
To prevent misuse of the scripts on user protected websites to breach security on user websites, the HTML Cross-Site Scripting check blocks scripts that violate the same origin rule, which states that scripts should not access or modify content on any server but the server on which they are located. Any script that violates the same origin rule is called a cross-site script, and the practice of using scripts to access or modify content on another server is called cross-site scripting. The reason cross-site scripting is a security issue is that a web server that allows cross-site scripting can be attacked with a script that is not on that web server, but on a different web server, such as one owned and controlled by the attacker.
Unfortunately, many companies have a large installed base of JavaScript-enhanced web content that violates the same origin rule. If users enable the HTML Cross-Site Scripting check on such a site, they have to generate the appropriate exceptions so that the check does not block legitimate activity.
The Web Application Firewall offers various action options for implementing HTML Cross-Site Scripting protection. In addition to the Block, Log, Stats and Learn actions, users also have the option to Transform cross-site scripts to render an attack harmless by entity encoding the script tags in the submitted request. Users can configure Check complete URLs for the cross-site scripting parameter to specify if they want to inspect not just the query parameters but the entire URL to detect a cross-site scripting attack. Users can configure the InspectQueryContentTypes parameter to inspect the request query portion for a cross-site scripting attack for the specific content-types.
Users can deploy relaxations to avoid false positives. The Web Application Firewall learning engine can provide recommendations for configuring relaxation rules.
The following options are available for configuring an optimized HTML Cross-Site Scripting protection for the user application:
-
Block — If users enable
block, the block action is triggered if the cross-site scripting tags are detected in the request. -
Log — If users enable the log feature, the HTML Cross-Site Scripting check generates log messages indicating the actions that it takes. If
blockis disabled, a separate log message is generated for each header or form field in which the cross-site scripting violation was detected. However, only one message is generated when the request is blocked. Similarly, 1 log message per request is generated for the transform operation, even when cross-site scripting tags are transformed in multiple fields. Users can monitor the logs to determine whether responses to legitimate requests are getting blocked. A large increase in the number of log messages can indicate attempts to launch an attack. -
Stats — If enabled, the stats feature gathers statistics about violations and logs. An unexpected surge in the stats counter might indicate that the user application is under attack. If legitimate requests are getting blocked, users might have to revisit the configuration to see if they must configure new relaxation rules or modify the existing ones.
-
Learn — If users are not sure which relaxation rules might be ideally suited for their application, they can use the learn feature to generate HTML Cross-Site Scripting rule recommendations based on the learned data. The Web Application Firewall learning engine monitors the traffic and provides learning recommendations based on the observed values. To get optimal benefit without compromising performance, users might want to enable the learn option for a short time to get a representative sample of the rules, and then deploy the rules and disable learning.
-
Transform cross-site scripts — If enabled, the Web Application Firewall makes the following changes to requests that match the HTML Cross-Site Scripting check:
-
Left angle bracket (<) to HTML character entity equivalent (<)
-
Right angle bracket (>) to HTML character entity equivalent (>)
-
This ensures that browsers do not interpret unsafe html tags, such as <script>, and thereby run malicious code. If users enable both request-header checking and transformation, any special characters found in request headers are also modified as described above. If scripts on the user protected website contain cross-site scripting features, but the user website does not rely upon those scripts to operate correctly, users can safely disable blocking and enable transformation. This configuration ensures that no legitimate web traffic is blocked, while stopping any potential cross-site scripting attacks.
-
Check complete URLs for cross-site scripting — If checking of complete URLs is enabled, the Web Application Firewall examines entire URLs for HTML cross-site scripting attacks instead of checking just the query portions of URLs.
-
Check Request headers — If Request header checking is enabled, the Web Application Firewall examines the headers of requests for HTML cross-site scripting attacks, instead of just URLs. If users use the GUI, they can enable this parameter in the Settings tab of the Web Application Firewall profile.
-
InspectQueryContentTypes — If Request query inspection is configured, the Application Firewall examines the query of requests for cross-site scripting attacks for the specific content-types. If users use the GUI, they can configure this parameter in the Settings tab of the Application Firewall profile.
Important:
As part of the streaming changes, the Web Application Firewall processing of the cross-site scripting tags has changed. In earlier releases, the presence of either open bracket (<), or close bracket (>), or both open and close brackets (<>) was flagged as a cross-site scripting Violation. The behavior has changed in the builds that include support for request side streaming. Only the close bracket character (>) is no longer considered as an attack. Requests are blocked even when an open bracket character (<) is present, and is considered as an attack. The Cross-site scripting attack gets flagged.
Buffer Overflow Check
The Buffer Overflow check detects attempts to cause a buffer overflow on the web server. If the Web Application Firewall detects that the URL, cookies, or header are longer than the configured length, it blocks the request because it can cause a buffer overflow.
The Buffer Overflow check prevents attacks against insecure operating-system or web-server software that can crash or behave unpredictably when it receives a data string that is larger than it can handle. Proper programming techniques prevent buffer overflows by checking incoming data and either rejecting or truncating overlong strings. Many programs, however, do not check all incoming data and are therefore vulnerable to buffer overflows. This issue especially affects older versions of web-server software and operating systems, many of which are still in use.
The Buffer Overflow security check allows users to configure the Block, Log, and Stats actions. In addition, users can also configure the following parameters:
-
Maximum URL Length. The maximum length the Web Application Firewall allows in a requested URL. Requests with longer URLs are blocked. Possible Values: 0–65535. Default: 1024
-
Maximum Cookie Length. The maximum length the Web Application Firewall allows for all cookies in a request. Requests with longer cookies trigger the violations. Possible Values: 0–65535. Default: 4096
-
Maximum Header Length. The maximum length the Web Application Firewall allows for HTTP headers. Requests with longer headers are blocked. Possible Values: 0–65535. Default: 4096
-
Query string length. Maximum length allowed for a query string in an incoming request. Requests with longer queries are blocked. Possible Values: 0–65535. Default: 1024
-
Total request length. Maximum request length allowed for an incoming request. Requests with a longer length are blocked. Possible Values: 0–65535. Default: 24820
Virtual Patching/Signatures
The signatures provide specific, configurable rules to simplify the task of protecting user websites against known attacks. A signature represents a pattern that is a component of a known attack on an operating system, web server, website, XML-based web service, or other resource. A rich set of preconfigured built-in or native rules offers an easy to use security solution, applying the power of pattern matching to detect attacks and protect against application vulnerabilities.
Users can create their own signatures or use signatures in the built-in templates. The Web Application Firewall has two built-in templates:
- Default Signatures: This template contains a preconfigured list of over 1,300 signatures, in addition to a complete list of SQL injection keywords, SQL special strings, SQL transform rules, and SQL wildcard characters. It also contains denied patterns for cross-site scripting, and allowed attributes and tags for cross-site scripting. This is a read-only template. Users can view the contents, but they cannot add, edit, or delete anything in this template. To use it, users must make a copy. In their own copy, users can enable the signature rules that they want to apply to their traffic, and specify the actions to be taken when the signature rules match the traffic.
The signatures are derived from the rules published by SNORT: SNORT, which is an open source intrusion prevention system capable of performing real-time traffic analysis to detect various attacks and probes.
- *Xpath Injection Patterns: This template contains a preconfigured set of literal and PCRE keywords and special strings that are used to detect XPath (XML Path Language) injection attacks.
Blank Signatures: In addition to making a copy of the built-in Default Signatures template, users can use a blank signatures template to create a signature object. The signature object that users create with the blank signatures option does not have any native signature rules, but, just like the *Default template, it has all the SQL/XSS built-in entities.
External-Format Signatures: The Web Application Firewall also supports external format signatures. Users can import the third-party scan report by using the XSLT files that are supported by the Citrix Web Application Firewall. A set of built-in XSLT files is available for selected scan tools to translate external format files to native format (see the list of built-in XSLT files later in this section).
While signatures help users to reduce the risk of exposed vulnerabilities and protect the user mission critical Web Servers while aiming for efficacy, Signatures do come at a Cost of additional CPU Processing.
It is important to choose the right Signatures for user Application needs. Enable only the signatures that are relevant to the Customer Application/environment.
Citrix offers signatures in more than 10 different categories across platforms/OS/Technologies.
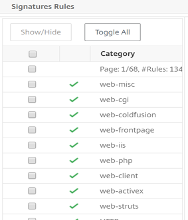
The signature rules database is substantial, as attack information has built up over the years. So, most of the old rules may not be relevant for all networks as Software Developers may have patched them already or customers are running a more recent version of the OS.
Signatures Updates
Citrix Web Application Firewall supports both Auto & Manual Update of Signatures. We also suggest enabling Auto-update for signatures to stay up to date.
These signatures files are hosted on the AWS Environment and it is important to allow outbound access to NetScaler® IPs from Network Firewalls to fetch the latest signature files. There is no effect of updating signatures to the ADC while processing Real Time Traffic
Application Security Analytics
The Application Security Dashboard provides a holistic view of the security status of user applications. For example, it shows key security metrics such as security violations, signature violations, and threat indexes. Application Security dashboard also displays attack related information such as syn attacks, small window attacks, and DNS flood attacks for the discovered Citrix ADC instances.
Note:
To view the metrics of the Application Security Dashboard, AppFlow® for Security insight should be enabled on the Citrix ADC instances that users want to monitor.
To view the security metrics of a Citrix ADC instance on the application security dashboard
-
Log on to Citrix ADM using the administrator credentials.
-
Navigate to Applications > App Security Dashboard, and select the instance IP address from the Devices list.
Users can further drill down on the discrepancies reported on the Application Security Investigator by clicking the bubbles plotted on the graph.
Centralized Learning on ADM
Citrix Web Application Firewall (WAF) protects user web applications from malicious attacks such as SQL injection and cross-site scripting (XSS). To prevent data breaches and provide the right security protection, users must monitor their traffic for threats and real-time actionable data on attacks. Sometimes, the attacks reported might be false-positives and those need to be provided as an exception.
The Centralized Learning on Citrix ADM is a repetitive pattern filter that enables WAF to learn the behavior (the normal activities) of user web applications. Based on monitoring, the engine generates a list of suggested rules or exceptions for each security check applied on the HTTP traffic.
It is much easier to deploy relaxation rules using the Learning engine than to manually deploy it as necessary relaxations.
To deploy the learning feature, users must first configure a Web Application Firewall profile (set of security settings) on the user Citrix ADC appliance. For more information, see Creating Web Application Firewall profiles: Creating Web App Firewall Profiles.
Citrix ADM generates a list of exceptions (relaxations) for each security check. As an administrator, users can review the list of exceptions in Citrix ADM and decide to deploy or skip.
Using the WAF learning feature in Citrix ADM, users can:
-
Configure a learning profile with the following security checks
-
Buffer Overflow
-
HTML Cross-Site Scripting
Note:
The cross-site script limitation of location is only FormField.
- HTML SQL Injection
Note:
For the HTML SQL Injection check, users must configure
set -sqlinjectionTransformSpecialCharsto ON andset -sqlinjectiontype sqlspclcharorkeywordsin the Citrix ADC instance. -
-
Check the relaxation rules in Citrix ADM and decide to take necessary action (deploy or skip)
-
Get the notifications through email, slack, and ServiceNow
-
Use the dashboard to view relaxation details
To use the WAF learning in Citrix ADM:
-
Configure the learning profile: Configure the Learning Profile
-
See the relaxation rules: View Relaxation Rules and Idle Rules
-
Use the WAF learning dashboard: View WAF Learning Dashboard
StyleBook
Citrix Web Application Firewall is a Web Application Firewall (WAF) that protects web applications and sites from both known and unknown attacks, including all application-layer and zero-day threats.
Citrix ADM now provides a default StyleBook with which users can more conveniently create an application firewall configuration on Citrix ADC instances.
Deploying Application Firewall Configurations
The following task assists you in deploying a load balancing configuration along with the application firewall and IP reputation policy on Citrix ADC instances in your business network.
To Create an LB Configuration with Application Firewall Settings
In Citrix ADM, navigate to Applications > Configurations > StyleBooks. The StyleBooks page displays all the StyleBooks available for customer use in Citrix
- ADM. Scroll down and find HTTP/SSL Load Balancing StyleBook with application firewall policy and IP reputation policy. Users can also search for the StyleBook by typing the name as
lb-appfw. Click Create Configuration.
The StyleBook opens as a user interface page on which users can enter the values for all the parameters defined in this StyleBook.
-
Enter values for the following parameters:
-
Load Balanced Application Name. Name of the load balanced configuration with an application firewall to deploy in the user network.
-
Load balanced App Virtual IP address. Virtual IP address at which the Citrix ADC instance receives client requests.
-
Load Balanced App Virtual Port. The TCP Port to be used by the users in accessing the load balanced application.
-
Load Balanced App Protocol. Select the front-end protocol from the list.
-
Application Server Protocol. Select the protocol of the application server.
-

- As an option, users can enable and configure the Advanced Load Balancer Settings.

- Optionally, users can also set up an authentication server for authenticating traffic for the load balancing virtual server.
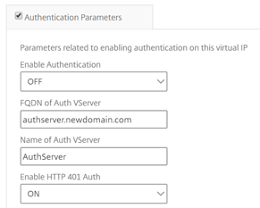
- Click “+” in the server IPs and Ports section to create application servers and the ports that they can be accessed on.
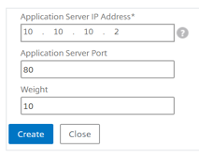
- Users can also create FQDN names for application servers.
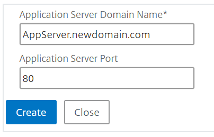
- Users can also specify the details of the SSL certificate.
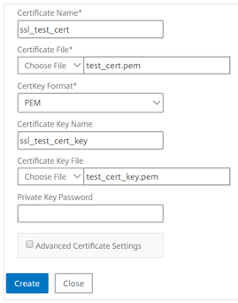
- Users can also create monitors in the target Citrix ADC instance.
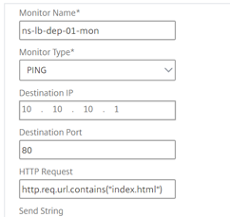
- To configure the application firewall on the virtual server, enable WAF Settings.
Ensure that the application firewall policy rule is true if users want to apply the application firewall settings to all traffic on that VIP. Otherwise, specify the Citrix ADC policy rule to select a subset of requests to which to apply the application firewall settings. Next, select the type of profile that has to be applied - HTML or XML.
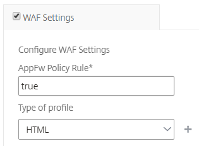
-
Optionally, users can configure detailed application firewall profile settings by enabling the application firewall Profile Settings check box.
-
Optionally, if users want to configure application firewall signatures, enter the name of the signature object that is created on the Citrix ADC instance where the virtual server is to be deployed.
Note:
Users cannot create signature objects by using this StyleBook.
- Next, users can also configure any other application firewall profile settings such as, StartURL settings, DenyURL settings and others.
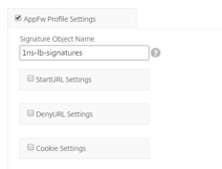
For more information on application firewall and configuration settings, see Application Firewall.
- In the Target Instances section, select the Citrix ADC instance on which to deploy the load balancing virtual server with the application firewall.
Note:
Users can also click the refresh icon to add recently discovered Citrix ADC instances in Citrix ADM to the available list of instances in this window.
- Users can also enable IP Reputation check to identify the IP address that is sending unwanted requests. Users can use the IP reputation list to preemptively reject requests that are coming from the IP with the bad reputation.
Tip:
Citrix recommends that users select Dry Run to check the configuration objects that must be created on the target instance before they run the actual configuration on the instance.
When the configuration is successfully created, the StyleBook creates the required load balancing virtual server, application server, services, service groups, application firewall labels, application firewall policies, and binds them to the load balancing virtual server.
The following figure shows the objects created in each server:
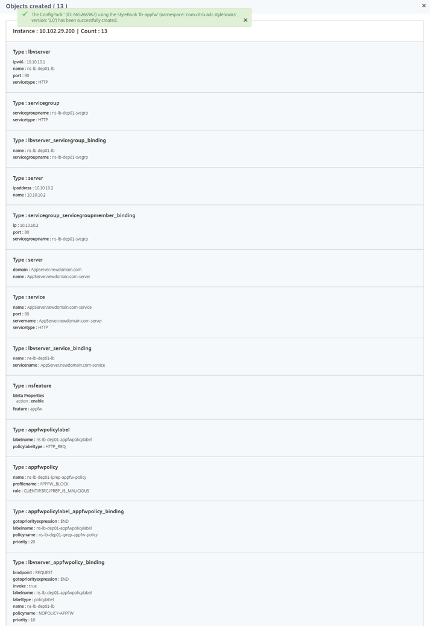
- To see the ConfigPack created on Citrix ADM, navigate to Applications > Configurations.

Security Insight Analytics
Web and web service applications that are exposed to the Internet have become increasingly vulnerable to attacks. To protect applications from attack, users need visibility into the nature and extent of past, present, and impending threats, real-time actionable data on attacks, and recommendations on countermeasures. Security Insight provides a single-pane solution to help users assess user application security status and take corrective actions to secure user applications.
How Security Insight Works
Security Insight is an intuitive dashboard-based security analytics solution that gives users full visibility into the threat environment associated with user applications. Security insight is included in Citrix ADM, and it periodically generates reports based on the user Application Firewall and ADC system security configurations. The reports include the following information for each application:
- Threat index. A single-digit rating system that indicates the criticality of attacks on the application, regardless of whether the application is protected by an ADC appliance. The more critical the attacks on an application, the higher the threat index for that application. Values range from 1 through 7.
The threat index is based on attack information. The attack-related information, such as violation type, attack category, location, and client details, gives users insight into the attacks on the application. Violation information is sent to Citrix ADM only when a violation or attack occurs. Many breaches and vulnerabilities lead to a high threat index value.
- Safety index. A single-digit rating system that indicates how securely users have configured the ADC instances to protect applications from external threats and vulnerabilities. The lower the security risks for an application, the higher the safety index. Values range from 1 through 7.
The safety index considers both the application firewall configuration and the ADC system security configuration. For a high safety index value, both configurations must be strong. For example, if rigorous application firewall checks are in place but ADC system security measures, such as a strong password for the nsroot user, have not been adopted, applications are assigned a low safety index value.
- Actionable Information. Information that users need for lowering the threat index and increasing the safety index, which significantly improves application security. For example, users can review information about violations, existing and missing security configurations for the application firewall and other security features, the rate at which the applications are being attacked, and so on.
Configuring Security Insight
Note:
Security Insight is supported on ADC instances with Premium license or ADC Advanced with AppFirewall license only.
To configure security insight on an ADC instance, first configure an application firewall profile and an application firewall policy, and then bind the application firewall policy globally.
Then, enable the AppFlow feature, configure an AppFlow collector, action, and policy, and bind the policy globally. When users configure the collector, they must specify the IP address of the Citrix ADM service agent on which they want to monitor the reports.
Configure Security Insight on an ADC Instance
- Run the following commands to configure an application firewall profile and policy, and bind the application firewall policy globally or to the load balancing virtual server.
add appfw profile <name> [-defaults ( basic or advanced )]
set appfw profile <name> [-startURLAction <startURLAction> …]
add appfw policy <name> <rule> <profileName>
bind appfw global <policyName> <priority>
or,
bind lb vserver <lb vserver> -policyName <policy> -priority <priority>
Sample:
add appfw profile pr_appfw -defaults advanced
set appfw profile pr_appfw -startURLaction log stats learn
add appfw policy pr_appfw_pol "HTTP.REQ.HEADER(\"Host\").EXISTS" pr_appfw
bind appfw global pr_appfw_pol 1
or,
bind lb vserver outlook –policyName pr_appfw_pol –priority "20"
<!--NeedCopy-->
- Run the following commands to enable the AppFlow feature, configure an AppFlow collector, action, and policy, and bind the policy globally or to the load balancing virtual server:
add appflow collector <name> -IPAddress <ipaddress>
set appflow param [-SecurityInsightRecordInterval <secs>] [-SecurityInsightTraffic ( ENABLED or DISABLED )]
add appflow action <name> -collectors <string>
add appflow policy <name> <rule> <action>
bind appflow global <policyName> <priority> [<gotoPriorityExpression>] [-type <type>]
or,
bind lb vserver <vserver> -policyName <policy> -priority <priority>
Sample:
add appflow collector col -IPAddress 10.102.63.85
set appflow param -SecurityInsightRecordInterval 600 -SecurityInsightTraffic ENABLED
add appflow action act1 -collectors col
add appflow action af_action_Sap_10.102.63.85 -collectors col
add appflow policy pol1 true act1
add appflow policy af_policy_Sap_10.102.63.85 true af_action_Sap_10.102.63.85
bind appflow global pol1 1 END -type REQ_DEFAULT
or,
bind lb vserver Sap –policyName af_action_Sap_10.102.63.85 –priority "20"
<!--NeedCopy-->
Enable Security Insight from Citrix ADM
-
Navigate to Networks > Instances > Citrix ADC and select the instance type. For example, VPX.
-
Select the instance and from the Select Action list, select Configure Analytics.
-
On the Configure Analytics on virtual server window:
- Select the virtual servers that you want to enable security insight and click Enable Analytics.
The Enable Analytics window is displayed.
-
Select Security Insight
-
Under Advanced Options, select Logstream or IPFIX as the Transport Mode
-
The Expression is true by default
-
Click OK
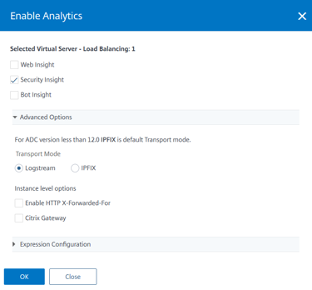
Note:
If users select virtual servers that are not licensed, then Citrix ADM first licenses those virtual servers and then enables analytics
For admin partitions, only Web Insight is supported
After users click OK, Citrix ADM processes to enable analytics on the selected virtual servers.
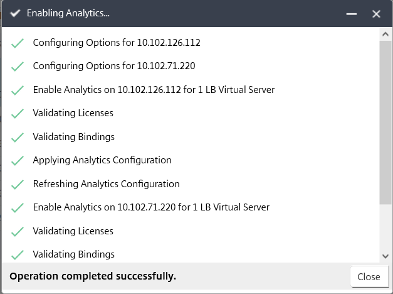
Note:
When users create a group, they can assign roles to the group, provide application-level access to the group, and assign users to the group. Citrix ADM analytics now supports virtual IP address-based authorization. Customer users can now see reports for all Insights for only the applications (virtual servers) for which they are authorized. For more information on groups and assigning users to the group, see Configure Groups on Citrix ADM: Configure Groups on Citrix ADM.
Thresholds
Users can set and view thresholds on the safety index and threat index of applications in Security Insight.
To set a threshold
-
Navigate to System > Analytics Settings > Thresholds, and select Add.
-
Select the traffic type as Security in the Traffic Type field, and enter required information in the other appropriate fields such as Name, Duration, and entity.
-
In the Rule section, use the Metric, Comparator, and Value fields to set a threshold. For example, “Threat Index” “>” “5”
-
Click Create.
To view the threshold breaches
-
Navigate to Analytics > Security Insight > Devices, and select the ADC instance.
-
In the Application section, users can view the number of threshold breaches that have occurred for each virtual server in the Threshold Breach column.
Security Insight Use Case
The following use cases describe how users can use security insight to assess the threat exposure of applications and improve security measures.
Obtain an Overview of the Threat Environment
In this use case, users have a set of applications that are exposed to attacks, and they have configured Citrix ADM to monitor the threat environment. Users need to frequently review the threat index, safety index, and the type and severity of any attacks that the applications might have experienced, so that they can focus first on the applications that need the most attention. The security insight dashboard provides a summary of the threats experienced by the user applications over a time period of user choosing, and for a selected ADC device. It displays the list of applications, their threat and safety indexes, and the total number of attacks for the chosen time period.
For example, users might be monitoring Microsoft Outlook, Microsoft Lync, SharePoint, and an SAP application, and users might want to review a summary of the threat environment for these applications.
To obtain a summary of the threat environment, log on to Citrix ADM, and then navigate to Analytics > Security Insight.
Key information is displayed for each application. The default time period is 1 hour.
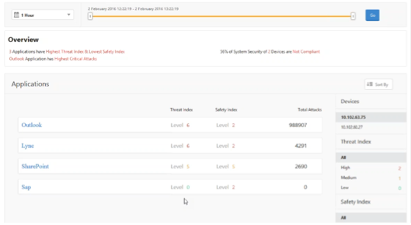
To view information for a different time period, from the list at the top-left, select a time period.
To view a summary for a different ADC instance, under Devices, click the IP address of the ADC instance. To sort the application list by a given column, click the column header.
Determine the Threat Exposure of an Application
After reviewing a summary of the threat environment on the Security Insight dashboard to identify the applications that have a high threat index and a low safety index, users want to determine their threat exposure before deciding how to secure them. That is, users want to determine the type and severity of the attacks that have degraded their index values. Users can determine the threat exposure of an application by reviewing the application summary.
In this example, Microsoft Outlook has a threat index value of 6, and users want to know what factors are contributing to this high threat index.
To determine the threat exposure of Microsoft Outlook, on the Security Insight dashboard, click Outlook. The application summary includes a map that identifies the geographic location of the server.
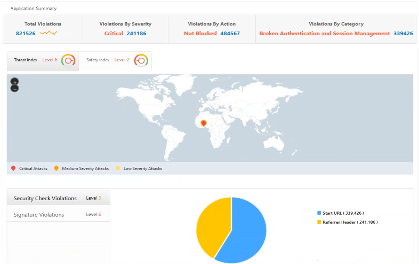
Click Threat Index > Security Check Violations and review the violation information that appears.
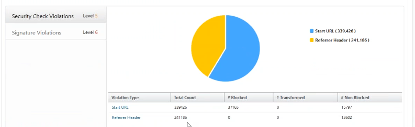
Click Signature Violations and review the violation information that appears.
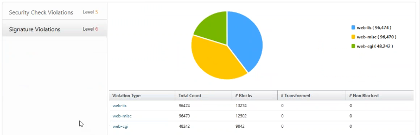
Determine Existing and Missing Security Configurations for an Application
After reviewing the threat exposure of an application, users want to determine what application security configurations are in place and what configurations are missing for that application. Users can obtain this information by drilling down into the application’s safety index summary.
The safety index summary gives users information about the effectiveness of the following security configurations:
-
Application Firewall Configuration. Shows how many signature and security entities are not configured.
-
Citrix ADM System Security. Shows how many system security settings are not configured.

In the previous use case, users reviewed the threat exposure of Microsoft Outlook, which has a threat index value of 6. Now, users want to know what security configurations are in place for Outlook and what configurations can be added to improve its threat index.
On the Security Insight dashboard, click Outlook, and then click the Safety Index tab. Review the information provided in the Safety Index Summary area.

On the Application Firewall Configuration node, click Outlook_Profile and review the security check and signature violation information in the pie charts.

Review the configuration status of each protection type in the application firewall summary table. To sort the table on a column, click the column header.
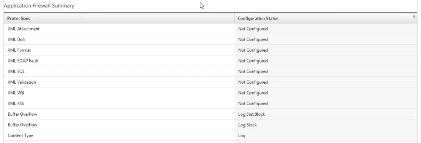
Click the Citrix ADM System Security node and review the system security settings and Citrix recommendations to improve the application safety index.
Identify Applications That Require Immediate Attention
The applications that need immediate attention are those having a high threat index and a low safety index.
In this example, both Microsoft Outlook and Microsoft Lync have a high threat index value of 6, but Lync has the lower of the two safety indexes. Therefore, users might have to focus their attention on Lync before improving the threat environment for Outlook.
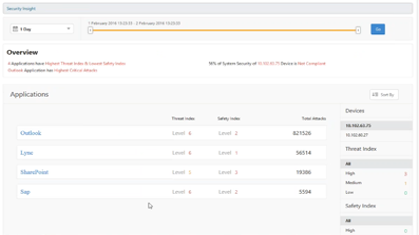
Determine the Number of Attacks in a Given Period of Time
Users might want to determine how many attacks occurred on a given application at a given point in time, or they might want to study the attack rate for a specific time period.
On the Security Insight page, click any application and in the Application Summary, click the number of violations. The Total Violations page displays the attacks in a graphical manner for one hour, one day, one week, and one month.

The Application Summary table provides the details about the attacks. Some of them are as follows:
-
Attack time
-
IP address of the client from which the attack happened
-
Severity
-
Category of violation
-
URL from which the attack originated, and other details.
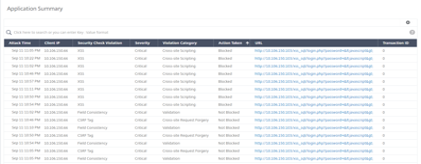
While users can always view the time of attack in an hourly report as seen in the image, now they can view the attack time range for aggregated reports even for daily or weekly reports. If users select “1 Day” from the time-period list, the Security Insight report displays all attacks that are aggregated and the attack time is displayed in a one-hour range. If users choose “1 Week” or “1 Month,” all attacks are aggregated and the attack time is displayed in a one-day range.
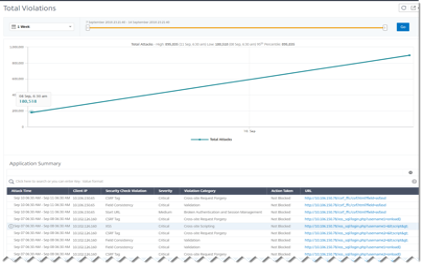
Obtain Detailed Information about Security Breaches
Users might want to view a list of the attacks on an application and gain insights into the type and severity of attacks, actions taken by the ADC instance, resources requested, and the source of the attacks.
For example, users might want to determine how many attacks on Microsoft Lync were blocked, what resources were requested, and the IP addresses of the sources.
On the Security Insight dashboard, click Lync > Total Violations. In the table, click the filter icon in the Action Taken column header, and then select Blocked.
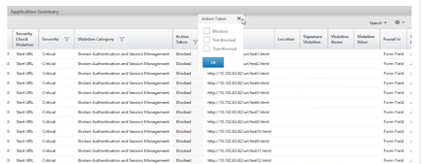
For information about the resources that were requested, review the URL column. For information about the sources of the attacks, review the Client IP column.
View Log Expression Details
Citrix ADC instances use log expressions configured with the Application Firewall profile to take action for the attacks on an application in the user enterprise. In Security Insight, users can view the values returned for the log expressions used by the ADC instance. These values include, request header, request body and so on. In addition to the log expression values, users can also view the log expression name and the comment for the log expression defined in the Application Firewall profile that the ADC instance used to take action for the attack.
Prerequisites
Ensure that users:
-
Configure log expressions in the Application Firewall profile. For more information, see Application Firewall.
-
Enable log expression-based Security Insights settings in Citrix ADM. Do the following:
-
Navigate to Analytics > Settings, and click Enable Features for Analytics.
-
In the Enable Features for Analytics page, select Enable Security Insight under the Log Expression Based Security Insight Setting section and click OK.
-
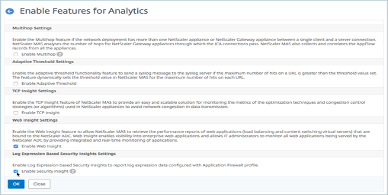
For example, users might want to view the values of the log expression returned by the ADC instance for the action it took for an attack on Microsoft Lync in the user enterprise.
On the Security Insight dashboard, navigate to Lync > Total Violations. In the Application Summary table, click the URL to view the complete details of the violation in the Violation Information page including the log expression name, comment, and the values returned by the ADC instance for the action.
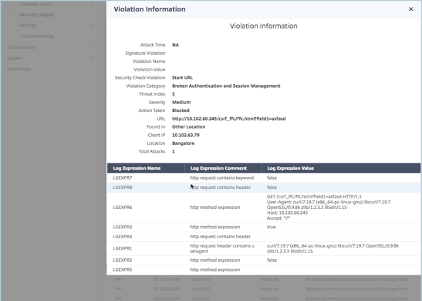
Determine the Safety Index before Deploying the Configuration
Security breaches occur after users deploy the security configuration on an ADC instance, but users might want to assess the effectiveness of the security configuration before they deploy it.
For example, users might want to assess the safety index of the configuration for the SAP application on the ADC instance with IP address 10.102.60.27.
On the Security Insight dashboard, under Devices, click the IP address of the ADC instance that users configured. Users can see that both the threat index and the total number of attacks are 0. The threat index is a direct reflection of the number and type of attacks on the application. Zero attacks indicate that the application is not under any threat.
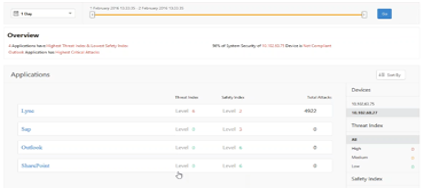
Click Sap > Safety Index > SAP_Profile and assess the safety index information that appears.
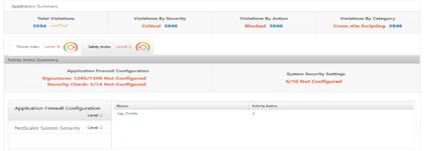
In the application firewall summary, users can view the configuration status of different protection settings. If a setting is set to log or if a setting is not configured, the application is assigned a lower safety index.
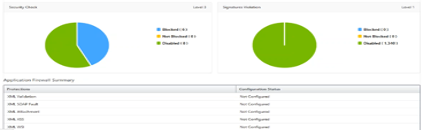
Security Violations
View Application Security Violation Details
Web applications that are exposed to the internet have become drastically more vulnerable to attacks. Citrix ADM enables users to visualize actionable violation details to protect applications from attacks. Navigate to Security > Security Violations for a single-pane solution to:
-
Access the application security violations based on their categories such as Network, Bot, and WAF
-
Take corrective actions to secure the applications
To view the security violations in Citrix ADM, ensure:
-
Users have a premium license for the Citrix ADC instance (for WAF and BOT violations).
-
Users have applied a license on the load balancing or content switching virtual servers (for WAF and BOT). For more information, see Manage Licensing on Virtual Servers.
-
Users enable more settings. For more information, see the procedure available at the Setting up section in the Citrix product documentation: Setting up.
Violation Categories**
Citrix ADM enables users to view the following violations:
| NETWORK | Bot | WAF |
|---|---|---|
| HTTP Slow Loris | Excessive Client Connections | Unusually High Upload Transactions |
| DNS Slow Loris | Account Takeover** | Unusually High Download Transactions |
| HTTP Slow Post | Unusually High Upload Volume | Excessive Unique IPs |
| NXDomain Flood Attack | Unusually High Request Rate | Excessive Unique IPs Per Geo |
| HTTP desync attack | Unusually High Download Volume | |
| Bleichenbacher Attack | ||
| Segment smack Attack | ||
| Syn Flood Attack | ||
** - Users must configure the account takeover setting in Citrix ADM. See the prerequisite mentioned in Account Takeover: Account Takeover.
Apart from these violations, users can also view the following Security Insight and Bot Insight violations under the WAF and Bot categories respectively:
| WAF | Bot |
|---|---|
| Buffer Overflow | Crawler |
| Content type | Feed Fetcher |
| Cookie Consistency | Link Checker |
| CSRF Form Tagging | Marketing |
| Deny URL | Scraper |
| Form Field Consistency | Screenshot Creator |
| Field Formats | Search Engine |
| Maximum Uploads | Service Agent |
| Referrer Header | Site Monitor |
| Safe Commerce | Speed Tester |
| Safe Object | Tool |
| HTML SQL Inject | Uncategorized |
| Start URL | Virus Scanner |
| XSS | Vulnerability Scanner |
| XML DoS | DeviceFP Wait Exceeded |
| XML Format | Invalid DeviceFP |
| XML WSI | Invalid Captcha Response |
| XML SSL | Captcha Attempts Exceeded |
| XML Attachment | Valid Captcha Response |
| XML SOAP Fault | Captcha Client Muted |
| XML Validation | Captcha Wait Time Exceeded |
| Others | Request Size Limit Exceeded |
| IP Reputation | Rate Limit Exceeded |
| HTTP DOS | Block list (IP, subnet, policy expression) |
| TCP Small Window | Allow list (IP, subnet, policy expression) |
| Signature Violation | Zero Pixel Request |
| File Upload Type | Source IP |
| JSON XSS | Host |
| JSON SQL | Geo Location |
| JSON DOS | URL |
| Command Injection | |
| Infer Content Type XML | |
| Cookie Hijack | |
Setting up
Users must enable Advanced Security Analytics and set Web Transaction Settings to All to view the following violations in Citrix ADM:
-
Unusually High Upload Transactions (WAF)
-
Unusually High Download Transactions (WAF)
-
Excessive Unique IPs (WAF)
-
Account takeover (BOT)
For other violations, ensure whether Metrics Collector is enabled. By default, Metrics Collector is enabled on the Citrix ADC instance. For more information, see: Configure Intelligent App Analytics.
Enable Advanced Security Analytics
-
Navigate to Networks > Instances > Citrix ADC, and select the instance type. For example, MPX.
-
Select the Citrix ADC instance and from the Select Action list, select Configure Analytics.
-
Select the virtual server and click Enable Analytics.
-
On the Enable Analytics window:
- Select Web Insight. After users select Web Insight, the read-only Advanced Security Analytics option is enabled automatically.
Note: The Advanced Security Analytics option is displayed only for premium licensed ADC instances.
-
Select Logstream as Transport Mode
-
The Expression is true by default
-
Click OK
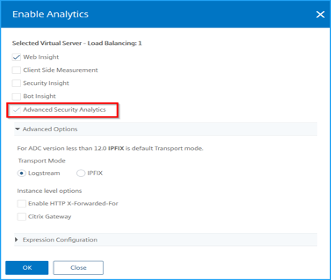
Enable Web Transaction settings
- Navigate to Analytics > Settings.
The Settings page is displayed.
-
Click Enable Features for Analytics.
-
Under Web Transaction Settings, select All.
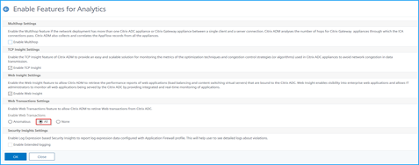
- Click Ok.
Security violations dashboard
In the security violations dashboard, users can view:
- Total violations occurred across all ADC instances and applications. The total violations are displayed based on the selected time duration.

- Total violations under each category.

- Total ADCs affected, total applications affected, and top violations based on the total occurrences and the affected applications.

Violation details
For each violation, Citrix ADM monitors the behavior for a specific time duration and detects violations for unusual behaviors. Click each tab to view the violation details. Users can view details such as:
-
The total occurrences, last occurred, and total applications affected
-
Under event details, users can view:
-
The affected application. Users can also select the application from the list if two or more applications are affected with violations.
-
The graph indicating violations.
Drag and select on the graph that lists the violations to narrow down the violation search.
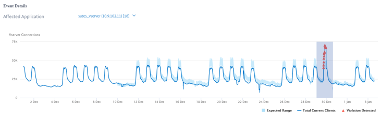
Click Reset Zoom to reset the zoom result
-
Recommended Actions that suggest users troubleshoot the issue
-
Other violation details such as violence occurrence time and detection message
-
Bot Insight
Using Bot Insight in Citrix ADM
After users configure the bot management in Citrix ADC, they must enable Bot Insight on virtual servers to view insights in Citrix ADM.
To enable Bot Insight:
-
Navigate to Networks > Instances > Citrix ADC and select the instance type. For example, VPX.
-
Select the instance and from the Select Action list, select Configure Analytics.
-
Select the virtual server and click Enable Analytics.
-
On the Enable Analytics window:
-
Select Bot Insight
-
Under Advanced Option, select Logstream.
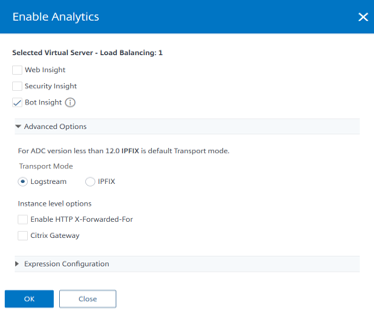
- Click OK.
-
After enabling Bot Insight, navigate to Analytics > Security > Bot Insight.
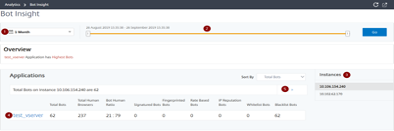
-
Time list to view bot details
-
Drag the slider to select a specific time range and click Go to display the customized results
-
Total instances affected from bots
-
Virtual server for the selected instance with total bot attacks
-
Total Bots – Indicates the total bot attacks (inclusive of all bot categories) found for the virtual server.
-
Total Human Browsers – Indicates the total human users accessing the virtual server.
-
Bot Human Ratio – Indicates the ratio between human users and bots accessing the virtual server.
-
Signature Bots, Fingerprinted Bot, Rate Based Bots, IP Reputation Bots, allow list Bots, and block list Bots – Indicates the total bot attacks occurred based on the configured bot category. For more information about bot categories, see: Configure Bot Detection Techniques in Citrix ADC.
-
-
Click > to view bot details in a graph format.
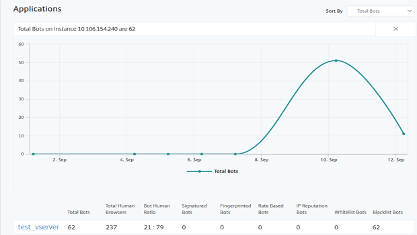
View events history
Users can view the bot signature updates in the Events History, when:
-
New bot signatures are added in Citrix ADC instances.
-
Existing bot signatures are updated in Citrix ADC instances.
You can select the time duration on the bot insight page to view the events history.
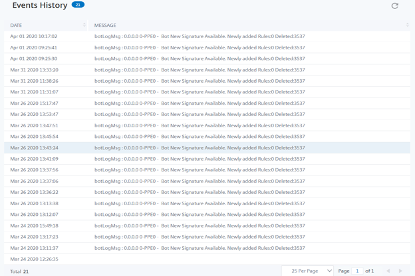
The following diagram shows how the bot signatures are retrieved from the AWS cloud, updated on Citrix ADC and view signature update summary on Citrix ADM.
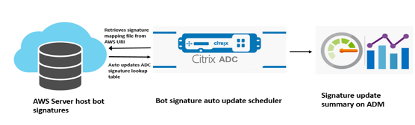
-
The bot signature auto update scheduler retrieves the mapping file from the AWS URI.
-
Checks the latest signatures in the mapping file with the existing signatures in the ADC appliance.
-
Downloads the new signatures from AWS and verifies the signature integrity.
-
Updates the existing bot signatures with the new signatures in the bot signature file.
-
Generates an SNMP alert and sends the signature update summary to Citrix ADM.
View Bots
Click the virtual server to view the Application Summary
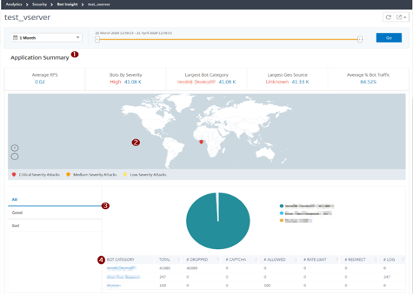
-
Provides the Application Summary details such as:
-
Average RPS – Indicates the average bot transaction requests per second (RPS) received on virtual servers.
-
Bots by Severity – Indicates the highest bot transactions occurred based on the severity. The severity is categorized based on Critical, High, Medium, and Low.
For example, if the virtual servers have 11770 high severity bots and 1550 critical severity bots, then Citrix ADM displays Critical 1.55 K under Bots by Severity.
-
Largest Bot Category – Indicates the highest bot attacks occurred based on the bot category.
For example, if the virtual servers have 8000 block listed bots, 5000 allow listed bots, and 10000 Rate Limit Exceeded bots, then Citrix ADM displays Rate Limit Exceeded 10 K under Largest Bot Category.
-
Largest Geo Source – Indicates the highest bot attacks occurred based on a region.
For example, if the virtual servers have 5000 bot attacks in Santa Clara, 7000 bot attacks in London, and 9000 bot attacks in Bangalore, then Citrix ADM displays Bangalore 9 K under Largest Geo Source.
-
Average % Bot Traffic – Indicates the human bot ratio.
-
-
Displays the severity of the bot attacks based on locations in map view
-
Displays the types of bot attacks (Good, Bad, and All)
-
Displays the total bot attacks along with the corresponding configured actions. For example, if you have configured:
-
IP address range (192.140.14.9 to 192.140.14.254) as block list bots and selected Drop as an action for these IP address ranges
-
IP range (192.140.15.4 to 192.140.15.254) as block list bots and selected to create a log message as an action for these IP ranges
In this scenario, Citrix ADM displays:
-
Total block listed bots
-
Total bots under Dropped
-
Total bots under Log
-
-
View CAPTCHA bots
In webpages, CAPTCHAs are designed to identify if the incoming traffic is from a human or an automated bot. To view the CAPTCHA activities in Citrix ADM, users must configure CAPTCHA as a bot action for IP reputation and device fingerprint detection techniques in a Citrix ADC instance. For more information, see: Configure Bot Management.
The following are the CAPTCHA activities that Citrix ADM displays in Bot insight:
-
Captcha attempts exceeded – Denotes the maximum number of CAPTCHA attempts made after login failures
-
Captcha client muted – Denotes the number of client requests that are dropped or redirected because these requests were detected as bad bots earlier with the CAPTCHA challenge
-
Human – Denotes the captcha entries performed from the human users
-
Invalid captcha response – Denotes the number of incorrect CAPTCHA responses received from the bot or human, when Citrix ADC sends a CAPTCHA challenge
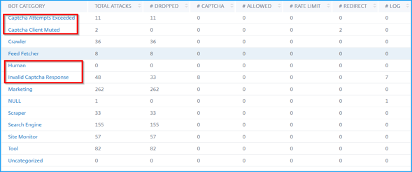
View bot traps
To view bot traps in Citrix ADM, you must configure the bot trap in the Citrix ADC instance. For more information, see Configure Bot Management.

To identify the bot trap, a script is enabled in the webpage and this script is hidden from humans, but not to bots. Citrix ADM identifies and reports the bot traps, when this script is accessed by bots.
Click the virtual server and select Zero Pixel Request

View bot details
For further details, click the bot attack type under Bot Category.
The details such as attack time and total number of bot attacks for the selected captcha category are displayed.
Users can also drag the bar graph to select the specific time range to be displayed with bot attacks.
To get additional information of the bot attack, click to expand.
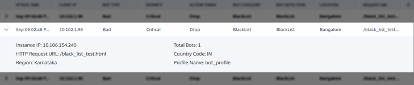
-
Instance IP – Indicates the Citrix ADC instance IP address
-
Total Bots – Indicates the total bot attacks occurred for that particular time
-
HTTP Request URL – Indicates the URL that is configured for captcha reporting
-
Country Code – Indicates the country where the bot attack occurred
-
Region – Indicates the region where the bot attack occurred
-
Profile Name – Indicates the profile name that users provided during the configuration
Advanced search
Users can also use the search text box and time duration list, where they can view bot details as per the user requirement. When users click the search box, the search box gives them the following list of search suggestions.
-
Instance IP – Citrix ADC instance IP address
-
Client-IP – Client IP address
-
Bot-Type – Bot type such as Good or Bad
-
Severity – Severity of the bot attack
-
Action-Taken – Action taken after the bot attack such as Drop, No action, Redirect
-
Bot-Category – Category of the bot attack such as block list, allow list, fingerprint, and so on. Based on a category, users can associate a bot action to it
-
Bot-Detection – Bot detection types (block list, allow list, and so on) that users have configured on Citrix ADC instance
-
Location – Region/country where the bot attack has occurred
-
Request-URL – URL that has the possible bot attacks
Users can also use operators in the user search queries to narrow the focus of the user search. For example, if users want to view all bad bots:
-
Click the search box and select Bot-Type
-
Click the search box again and select the operator =
-
Click the search box again and select Bad
-
Click Search to display the results

Bot violation details
Excessive Client Connections
When a client tries to access the web application, the client request is processed in Citrix ADC appliance, instead of connecting to the server directly. Web traffic comprises bots and bots can perform various actions at a faster rate than a human.
Using the Excessive Client Connections indicator, users can analyze scenarios when an application receives unusually high client connections through bots.
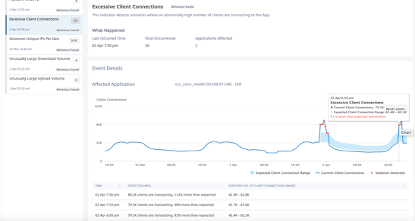
Under Event Details, users can view:
-
The affected application. Users can also select the application from the list if two or more applications are affected with violations.
-
The graph indicating all violations
-
The violation occurrence time
-
The detection message for the violation, indicating the total IP addresses transacting the application
-
The accepted IP address range that the application can receive
Account Takeover
Note:
Ensure users enable the advanced security analytics and web transaction options. For more information, see Setting up: Setting up.
Some malicious bots can steal user credentials and perform various kinds of cyberattacks. These malicious bots are known as bad bots. It is essential to identify bad bots and protect the user appliance from any form of advanced security attacks.
Prerequisite
Users must configure the Account Takeover settings in Citrix ADM.
-
Navigate to Analytics > Settings > Security Violations
-
Click Add

-
On the Add Application page, specify the following parameters:
-
Application - Select the virtual server from the list.
-
Method - Select the HTTP method type from the list. The available options are GET, PUSH, POST, and UPDATE.
-
Login URL and Success response code - Specify the URL of the web application and specify the HTTP status code (for example, 200) for which users want Citrix ADM to report the account takeover violation from bad bots.
-
Click Add.
-
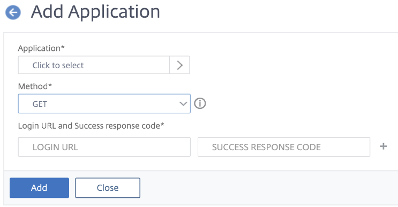
After users configure the settings, using the Account Takeover indicator, users can analyze if bad bots attempted to take over the user account, giving multiple requests along with credentials.

Under Event Details, users can view:
-
The affected application. Users can also select the application from the list if two or more applications are affected with violations.
-
The graph indicating all violations
-
The violation occurrence time
-
The detection message for the violation, indicating total unusual failed login activity, successful logins, and failed logins
-
The bad bot IP address. Click to view details such as time, IP address, total successful logins, total failed logins, and total requests made from that IP address.

Unusually High Upload Volume
Web traffic also comprises data that is processed for uploading. For example, if the user average upload data per day is 500 MB and if users upload 2 GB of data, then this can be considered as an unusually high upload data volume. Bots are also capable to process uploading of data more quickly than humans.
Using the Unusually High Upload Volume indicator, users can analyze abnormal scenarios of upload data to the application through bots.
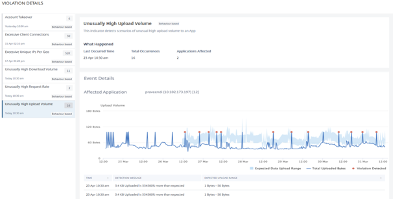
Under Event Details, users can view:
-
The affected application. Users can also select the application from the list if two or more applications are affected with violations.
-
The graph indicating all violations
-
The violation occurrence time
-
The detection message for the violation, indicating the total upload data volume processed
-
The accepted range of upload data to the application
Unusually High Download Volume
Similar to high upload volume, bots can also perform downloads more quickly than humans.
Using the Unusually High Download Volume indicator, users can analyze abnormal scenarios of download data from the application through bots.
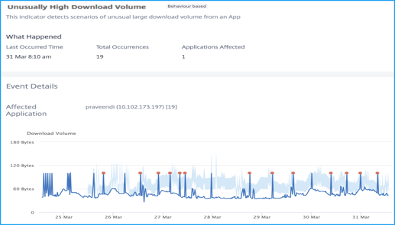
Under Event Details, users can view:
-
The affected application. Users can also select the application from the list if two or more applications are affected with violations.
-
The graph indicating all violations
-
The violation occurrence time
-
The detection message for the violation, indicating the total download data volume processed
-
The accepted range of download data from the application
Unusually High Request Rate
Users can control the incoming and outgoing traffic from or to an application. A bot attack can perform an unusually high request rate. For example, if users configure an application to allow 100 requests/minute and if users observe 350 requests, then it might be a bot attack.
Using the Unusually High Request Rate indicator, users can analyze the unusual request rate received to the application.
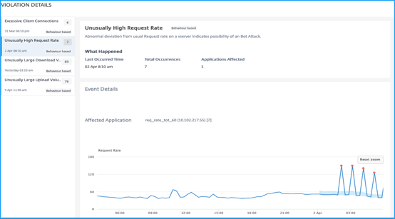
Under Event Details, users can view:
-
The affected application. Users can also select the application from the list if two or more applications are affected with violations.
-
The graph indicating all violations
-
The violation occurrence time
-
The detection message for the violation, indicating the total requests received and % of excessive requests received than the expected requests
-
The accepted range of expected request rate range from the application
Use Cases
Bot
Sometimes the incoming web traffic is comprised of bots and most organizations suffer from bot attacks. Web and mobile applications are significant revenue drivers for business and most companies are under the threat of advanced cyberattacks, such as bots. A bot is a software program that automatically performs certain actions repeatedly at a much faster rate than a human. Bots can interact with webpages, submit forms, run actions, scan texts, or download content. They can access videos, post comments, and tweet on social media platforms. Some bots, known as chatbots, can hold basic conversations with human users. A bot that performs a helpful service, such as customer service, automated chat, and search engine crawlers are good bots. At the same time, a bot that can scrape or download content from a website, steal user credentials, spam content, and perform other kinds of cyberattacks are bad bots. With a good number of bad bots performing malicious tasks, it is essential to manage bot traffic and protect the user web applications from bot attacks. By using Citrix bot management, users can detect the incoming bot traffic and mitigate bot attacks to protect the user web applications. Citrix bot management helps identify bad bots and protect the user appliance from advanced security attacks. It detects good and bad bots and identifies if incoming traffic is a bot attack. By using bot management, users can mitigate attacks and protect the user web applications.
Citrix ADC bot management provides the following benefits:
-
Defends against bots, scripts, and toolkits. Provides real-time threat mitigation using static signature-based defense and device fingerprinting.
-
Neutralizes automated basic and advanced attacks. Prevents attacks, such as App layer DDoS, password spraying, password stuffing, price scrapers, and content scrapers.
-
Protects user APIs and investments. Protects user APIs from unwarranted misuse and protects infrastructure investments from automated traffic.
Some use cases where users can benefit by using the Citrix bot management system are:
-
Brute force login. A government web portal is constantly under attack by bots attempting brute force user logins. The organization discovers the attack by looking through web logs and seeing specific users being hit over and over again with rapid login attempts and passwords incrementing using a dictionary attack approach. By law, they must protect themselves and their users. By deploying the Citrix bot management, they can stop brute force login using device fingerprinting and rate limiting techniques.
-
Block bad bots and device fingerprint unknown bots. A web entity gets 100,000 visitors each day. They have to upgrade the underlying footprint and they are spending a fortune. In a recent audit, the team discovered that 40 percent of the traffic came from bots, scraping content, picking news, checking user profiles, and more. They want to block this traffic to protect their users and reduce their hosting costs. Using bot management, they can block known bad bots, and fingerprint unknown bots that are hammering their site. By blocking these bots, they can reduce bot traffic by 90 percent.
-
Permit good bots. “Good” bots are designed to help businesses and consumers. They have been around since the early 1990s when the first search engine bots were developed to crawl the Internet. Google, Yahoo, and Bing would not exist without them. Other examples of good bots—mostly consumer-focused—include:
-
Chatbots (a.k.a. chatterbots, smart bots, talk bots, IM bots, social bots, conversation bots) interact with humans through text or sound. One of the first text uses was for online customer service and text messaging apps like Facebook Messenger and iPhone Messages. Siri, Cortana, and Alexa are chatbots; but so are mobile apps that let users order coffee and then tell them when it will be ready, let users watch movie trailers and find local theater showtimes, or send users a picture of the car model and license plate when they request a ride service.
-
Shopbots scour the Internet looking for the lowest prices on items users are searching for.
-
Monitoring bots check on the health (availability and responsiveness) of websites. Downdetector is an example of an independent site that provides real-time status information, including outages, of websites and other kinds of services. For more information about Downdetector, see: Downdetector.
-
Bot Detection
Configuring Bot Management by using Citrix ADC GUI
Users can configure Citrix ADC bot management by first enabling the feature on the appliance. Once users enable, they can create a bot policy to evaluate the incoming traffic as bot and send the traffic to the bot profile. Then, users create a bot profile and then bind the profile to a bot signature. As an alternative, users can also clone the default bot signature file and use the signature file to configure the detection techniques. After creating the signature file, users can import it into the bot profile. All these steps are performed in the following sequence:
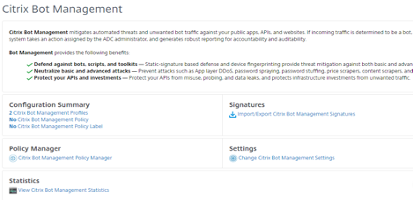
-
Enable bot management feature
-
Configure bot management settings
-
Clone Citrix bot default signature
-
Import Citrix bot signature
-
Configure bot signature settings
-
Create bot profile
-
Create bot policy
Enable Bot Management Feature
-
On the navigation pane, expand System and then click Settings.
-
On the Configure Advanced Features page, select the Bot Management check box.
-
Click OK, and then click Close.
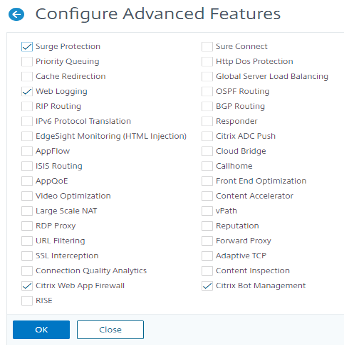
Clone Bot Signature File
-
Navigate to Security > Citrix Bot Management > Signatures.
-
In Citrix Bot Management Signatures page, select the default bot signatures record and click Clone.
-
In the Clone Bot Signature page, enter a name and edit the signature data.
-
Click Create.
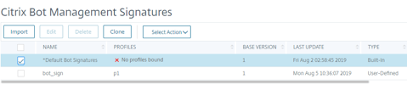
Import Bot Signature File
If users have their own signature file, then they can import it as a file, text, or URL. Perform the following the steps to import the bot signature file:
-
Navigate to Security > Citrix Bot Management and Signatures.
-
On the Citrix Bot Management Signatures page, import the file as URL, File, or text.
-
Click Continue.
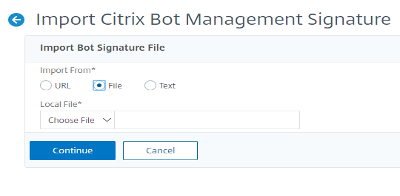
-
On the Import Citrix Bot Management Signature page, set the following parameters.
-
Name. Name of the bot signature file.
-
Comment. Brief description about the imported file.
-
Overwrite. Select the check box to allow overwriting of data during file update.
-
Signature Data. Modify signature parameters
-
-
Click Done.
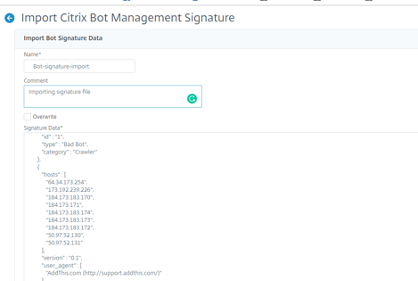
IP Reputation
Configure IP Reputation by using Citrix ADC GUI
This configuration is a prerequisite for the bot IP reputation feature. The detection technique enables users to identify if there is any malicious activity from an incoming IP address. As part of the configuration, we set different malicious bot categories and associate a bot action to each of them.
-
Navigate to Security > Citrix Bot Management and Profiles.
-
On the Citrix Bot Management Profiles page, select a signature file and click Edit.
-
On the Citrix Bot Management Profile page, go to Signature Settings section and click IP Reputation.
-
On the IP Reputation section, set the following parameters:
-
Enabled. Select the check box to validate incoming bot traffic as part of the detection process.
-
Configure Categories. Users can use the IP reputation technique for incoming bot traffic under different categories. Based on the configured category, users can drop or redirect the bot traffic. Click Add to configure a malicious bot category.
-
In the Configure Citrix Bot Management Profile IP Reputation Binding page, set the following parameters:
-
Category. Select a malicious bot category from the list. Associate a bot action based on category.
-
Enabled. Select the check box to validate the IP reputation signature detection.
-
Bot action. Based on the configured category, users can assign no action, drop, redirect, or CAPTCHA action.
-
Log. Select the check box to store log entries.
-
Log Message. Brief description of the log.
-
Comments. Brief description about the bot category.
-
-
-
Click OK.
-
Click Update.
-
Click Done.
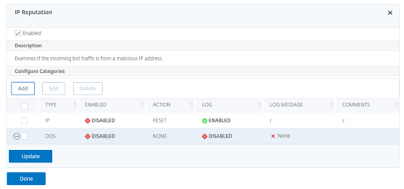
Auto Update for Bot Signatures
The bot static signature technique uses a signature lookup table with a list of good bots and bad bots. The bots are categorized based on user-agent string and domain names. If the user-agent string and domain name in incoming bot traffic matches a value in the lookup table, a configured bot action is applied. The bot signature updates are hosted on the AWS cloud and the signature lookup table communicates with the AWS database for signature updates. The auto signature update scheduler runs every 1-hour to check the AWS database and updates the signature table in the ADC appliance.
The Bot signature mapping auto update URL to configure signatures is: Bot Signature Mapping.
Note:
Users can also configure a proxy server and periodically update signatures from the AWS cloud to the ADC appliance through a proxy. For proxy configuration, users must set the proxy IP address and port address in the bot settings.
Configure Bot Signature Auto Update
For configuring bot signature auto update, complete the following steps:
Enable Bot Signature Auto Update
Users must enable the auto update option in the bot settings on the ADC appliance.
At the command prompt, type:
set bot settings –signatureAutoUpdate ON
Configure Bot Signature Auto Update using the Citrix ADC GUI
Complete the following steps to configure bot signature auto update:
-
Navigate to Security > Citrix Bot Management.
-
In the details pane, under Settings click Change Citrix Bot Management Settings.
-
In the Configure Citrix Bot Management Settings, select the Auto Update Signature check box.
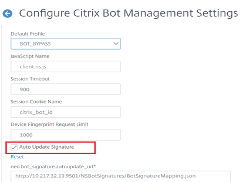
- Click OK and Close.
For more information on configuring IP Reputation using the CLI, see: Configure the IP Reputation Feature Using the CLI.
References
For information on using SQL Fine Grained Relaxations, see: SQL Fine Grained Relaxations.
For information on how to configure the SQL Injection Check using the command line, see: HTML SQL Injection Check.
For information on how to configure the SQL Injection Check using the GUI, see: Using the GUI to Configure the SQL Injection Security Check.
For information on using the Learn Feature with the SQL Injection Check, see: Using the Learn Feature with the SQL Injection Check.
For information on using the Log Feature with the SQL Injection Check, see: Using the Log Feature with the SQL Injection Check.
For information on Statistics for the SQL Injection violations, see: Statistics for the SQL Injection Violations.
For information on SQL Injection Check Highlights, see: Highlights.
For information about XML SQL Injection Checks, see: XML SQL Injection Check.
For information on using Cross-Site Scripting Fine Grained Relaxations, see: SQL Fine Grained Relaxations.
For information on configuring HTML Cross-Site Scripting using the command line, see: Using the Command Line to Configure the HTML Cross-Site Scripting Check.
For information on configuring HTML Cross-Site Scripting using the GUI, see: Using the GUI to Configure the HTML Cross-Site Scripting Check.
For information on using the Learn Feature with the HTML Cross-Site Scripting Check, see: Using the Learn Feature with the HTML Cross-Site Scripting Check.
For information on using the Log Feature with the HTML Cross-Site Scripting Check, see: Using the Log Feature with the HTML Cross-Site Scripting Check.
For information on statistics for the HTML Cross-Site Scripting violations, see: Statistics for the HTML Cross-Site Scripting Violations.
For information on HTML Cross-Site Scripting highlights, see: Highlights.
For information about XML Cross-Site Scripting, visit: XML Cross-Site Scripting Check.
For information on using the command line to configure the Buffer Overflow Security Check, see: Using the Command Line to Configure the Buffer Overflow Security Check.
For information on using the GUI to configure the Buffer Overflow Security Check, see: Configure Buffer Overflow Security Check by using the Citrix ADC GUI.
For information on using the Log Feature with the Buffer Overflow Security Check, see: Using the Log Feature with the Buffer Overflow Security Check.
For information on Statistics for the Buffer Overflow violations, see: Statistics for the Buffer Overflow Violations.
For information on the Buffer Overflow Security Check Highlights, see: Highlights.
For information on Adding or Removing a Signature Object, see: Adding or Removing a Signature Object.
For information on creating a signatures object from a template, see: To Create a Signatures Object from a Template.
For information on creating a signatures object by importing a file, see: To Create a Signatures Object by Importing a File.
For information on creating a signatures object by importing a file using the command line, see: To Create a Signatures Object by Importing a File using the Command Line.
For information on removing a signatures object by using the GUI, see: To Remove a Signatures Object by using the GUI.
For information on removing a signatures object by using the command line, see: To Remove a Signatures Object by using the Command Line.
For information on configuring or modifying a signatures object, see: Configuring or Modifying a Signatures Object.
For more information on updating a signature object, see: Updating a Signature Object.
For information on using the command line to update Web Application Firewall Signatures from the source, see: To Update the Web Application Firewall Signatures from the Source by using the Command Line.
For information on updating a signatures object from a Citrix format file, see: Updating a Signatures Object from a Citrix Format File.
For information on updating a signatures object from a supported vulnerability scanning tool, see: Updating a Signatures Object from a Supported Vulnerability Scanning Tool.
For information on Snort Rule Integration, see: Snort Rule Integration.
For information on configuring Snort Rules, see: Configure Snort Rules.
For information about configuring Bot Management using the command line, see: Configure Bot Management.
For information about configuring bot management settings for device fingerprint technique, see: Configure Bot Management Settings for Device Fingerprint Technique.
For information on configuring bot allow lists by using the Citrix ADC GUI, see: Configure Bot White List by using Citrix ADC GUI.
For information on configuring bot block lists by using the Citrix ADC GUI, see: Configure Bot Black List by using Citrix ADC GUI.
For more information on configuring Bot management, see: Configure Bot Management.
Prerequisites
Before attempting to create a VPX instance in AWS, users should ensure they have the following:
-
An AWS account to launch a Citrix ADC VPX AMI in an Amazon Web Services (AWS) Virtual Private Cloud (VPC). Users can create an AWS account for free at Amazon Web Services: AWS.
-
An AWS Identity and Access Management (IAM) user account to securely control access to AWS services and resources for users. For more information about how to create an IAM user account, see the topic: Creating IAM Users (Console).
An IAM role is mandatory for both standalone and high availability deployments. The IAM role must have the following privileges:
-
ec2:DescribeInstances
-
ec2:DescribeNetworkInterfaces
-
ec2:DetachNetworkInterface
-
ec2:AttachNetworkInterface
-
ec2:StartInstances
-
ec2:StopInstances
-
ec2:RebootInstances
-
ec2:DescribeAddresses
-
ec2:AssociateAddress
-
ec2:DisassociateAddress
-
ec2:AssignPrivateIpAddresses
-
autoscaling:*
-
sns:*
-
sqs:*
-
cloudwatch:*
-
iam:SimulatePrincipalPolicy
-
iam:GetRole
For more information on IAM permissions, see: AWS Managed Policies for Job Functions.
If the Citrix CloudFormation template is used, the IAM role is automatically created. The template does not allow selecting an already created IAM role.
Note:
When users log on the VPX instance through the GUI, a prompt to configure the required privileges for the IAM role appears. Ignore the prompt if the privileges have already been configured. Note:
AWS CLI is required to use all the functionality provided by the AWS Management Console from the terminal program. For more information, see the AWS CLI user guide: What Is the AWS Command Line Interface?. Users also need the AWS CLI to change the network interface type to SR-IOV.
For more information about Citrix ADC and AWS including support for the Citrix Networking VPX within AWS see Citrix ADC and Amazon Web Services Validated Reference Design guide: Citrix ADC and Amazon Web Services Validated Reference Design.
Limitations and Usage Guidelines
The following limitations and usage guidelines apply when deploying a Citrix ADC VPX instance on AWS:
-
Users should read the AWS terminology listed above before starting a new deployment.
-
The clustering feature is supported only when provisioned with Citrix ADM Auto Scale Groups.
-
For the high availability setup to work effectively, associate a dedicated NAT device to the management Interface or associate an Elastic IP (EIP) to NSIP. For more information on NAT, in the AWS documentation, see: NAT Instances.
-
Data traffic and management traffic must be segregated with ENIs belonging to different subnets.
-
Only the NSIP address must be present on the management ENI.
-
If a NAT instance is used for security instead of assigning an EIP to the NSIP, appropriate VPC level routing changes are required. For instructions on making VPC level routing changes, in the AWS documentation, see: Scenario 2: VPC with Public and Private Subnets.
-
A VPX instance can be moved from one EC2 instance type to another (for example, from m3.large to an m3.xlarge). For more information, visit: Limitations and Usage Guidelines.
-
For storage media for VPX on AWS, Citrix recommends EBS, because it is durable and the data is available even after it is detached from the instance.
-
Dynamic addition of ENIs to VPX is not supported. Restart the VPX instance to apply the update. Citrix recommends users to stop the standalone or HA instance, attach the new ENI, and then restart the instance. The primary ENI cannot be changed or attached to a different subnet once it is deployed. Secondary ENIs can be detached and changed as needed while the VPX is stopped.
-
Users can assign multiple IP addresses to an ENI. The maximum number of IP addresses per ENI is determined by the EC2 instance type, see the section “IP Addresses Per Network Interface Per Instance Type” in Elastic Network Interfaces: Elastic Network Interfaces. Users must allocate the IP addresses in AWS before they assign them to ENIs. For more information, see Elastic Network Interfaces: Elastic Network Interfaces.
-
Citrix recommends that users avoid using the enable and disable interface commands on Citrix ADC VPX interfaces.
-
The Citrix ADC
set ha node \<NODE\_ID\> -haStatus STAYPRIMARYandset ha node \<NODE\_ID\> -haStatus STAYSECONDARYcommands are disabled by default. -
IPv6 is not supported for VPX.
-
Due to AWS limitations, these features are not supported:
-
Gratuitous ARP(GARP)
-
L2 mode (bridging). Transparent virtual servers are supported with L2 (MAC rewrite) for servers in the same subnet as the SNIP.
-
Tagged VLAN
-
Dynamic Routing
-
Virtual MAC
-
-
For RNAT, routing, and Transparent virtual server to work, ensure Source/Destination Check is disabled for all ENIs in the data path. For more information, see “Changing the Source/Destination Checking” in Elastic Network Interfaces: Elastic Network Interfaces.
-
In a Citrix ADC VPX deployment on AWS, in some AWS regions, the AWS infrastructure might not be able to resolve AWS API calls. This happens if the API calls are issued through a non-management interface on the Citrix ADC VPX instance. As a workaround, restrict the API calls to the management interface only. To do that, create an NSVLAN on the VPX instance and bind the management interface to the NSVLAN by using the appropriate command.
-
For example:
-
set ns config -nsvlan <vlan id> -ifnum 1/1 -tagged NO
-
save config
-
-
Restart the VPX instance at the prompt.
-
For more information about configuring
nsvlan, see Configuring NSVLAN: Configuring NSVLAN. -
In the AWS console, the vCPU usage shown for a VPX instance under the Monitoring tab might be high (up to 100 percent), even when the actual usage is much lower. To see the actual vCPU usage, navigate to View all CloudWatch metrics. For more information, see: Monitor your Instances using Amazon CloudWatch. Alternately, if low latency and performance are not a concern, users may enable the CPU Yield feature allowing the packet engines to idle when there is no traffic. Visit Citrix Support Knowledge Center for more details about the CPU Yield feature and how to enable it.
Technical Requirements
Before users launch the Quick Start Guide to begin a deployment, the user account must be configured as specified in the following table. Otherwise, the deployment might fail.
Resources
If necessary, sign in to the user amazon account and request service limit increases for the following resources here: AWS/Sign in. You might need to do this if you already have an existing deployment that uses these resources, and you think you might exceed the default limits with this deployment. For default limits, see the AWS Service Quotas in the AWS documentation: AWS Service Quotas.
The AWS Trusted Advisor, found here: AWS/Sign in, offers a service limits check that displays usage and limits for some aspects of some services.
| Resource | This deployment uses |
|---|---|
| VPCs | 1 |
| Elastic IP addresses | 0/1(for Bastion host) |
| IAM security groups | 3 |
| IAM roles | 1 |
| Subnets | 6(3/Availability zone) |
| Internet Gateway | 1 |
| Route Tables | 5 |
| WAF VPX instances | 2 |
| Bastion host | 0/1 |
| NAT gateway | 2 |
Regions
Citrix WAF on AWS isn’t currently supported in all AWS Regions. For a current list of supported Regions, see AWS Service Endpoints in the AWS documentation: AWS Service Endpoints.
For more information on AWS regions and why cloud infrastructure matters, see: Global Infrastructure.
Key Pair
Make sure that at least one Amazon EC2 key pair exists in the user AWS account in the Region where users are planning to deploy using the Quick Start Guide. Make note of the key pair name. Users are prompted for this information during deployment. To create a key pair, follow the instructions for Amazon EC2 Key Pairs and Linux Instances in the AWS documentation: Amazon EC2 Key Pairs and Linux Instances.
If users are deploying the Quick Start Guide for testing or proof-of-concept purposes, we recommend that they create a new key pair instead of specifying a key pair that’s already being used by a production instance.
In this article
- Overview
- Citrix ADC VPX
- Amazon Web Services
- AWS Terminology
- Sample Citrix WAF on AWS Architecture
- Logical Flow of Citrix WAF on AWS
- Cost and Licensing
- Deployment Options
- Deployment Steps using a Quick Start Guide
- Citrix Application Delivery Management
- Deploying Citrix ADC VPX Instances on AWS using Citrix ADM
- Architecture Diagram
- Configuration Tasks
- Citrix ADC WAF and OWASP Top 10 – 2017
- A1:2017- Injection
- A2:2017 – Broken Authentication
- A3:2017 - Sensitive Data Exposure
- A4:2017 XML External Entities (XXE)
- A5:2017 Broken Access Control
- A6:2017 - Security Misconfiguration
- A7:2017 - Cross Site Scripting (XSS)
- A8:2017 - Insecure Deserialization
- A9:2017 - Using Components with Known Vulnerabilities
- A10:2017 - Insufficient Logging & Monitoring
- Application Security Protection
- Citrix ADM
- Use Cases
- Citrix Web Application Firewall (WAF)
- Web Application Firewall Deployment Strategy
- Configuring the Web Application Firewall (WAF)
- SQL Injection
- Cross-Site Scripting
- Buffer Overflow Check
- Virtual Patching/Signatures
- Application Security Analytics
- Centralized Learning on ADM
- StyleBook
- Deploying Application Firewall Configurations
- Security Insight Analytics
- Configuring Security Insight
- Thresholds
- Security Insight Use Case
- Security Violations
- View Application Security Violation Details
- Violation Categories**
- Setting up
- Security violations dashboard
- Violation details
- Bot Insight
- Using Bot Insight in Citrix ADM
- View events history
- View Bots
- View bot details
- Advanced search
- Bot violation details
- Excessive Client Connections
- Account Takeover
- Unusually High Upload Volume
- Unusually High Download Volume
- Unusually High Request Rate
- Use Cases
- Bot Detection
- IP Reputation
- References
- Prerequisites
- Limitations and Usage Guidelines
- Technical Requirements