Citrix ADC for Azure DNS Private Zone Deployment Guide
Introduction
Citrix ADC, formerly known as NetScaler, is a world-class product in the application delivery controller™ (ADC) space with the proven ability to load balance, manage global traffic, compression, and secure applications.
Azure DNS is a service on the Microsoft Azure infrastructure for hosting DNS domains and providing name resolution.
Azure DNS Private Zones is a service focused on resolving domain names in a private network. With Private Zones, customers can use their own custom domain names rather than the Azure-provided names available today.
Overview of Azure DNS
The Domain Name System, or DNS, is responsible for translating (or resolving) a service name to its IP address. A hosting service for DNS domains, Azure DNS provides name resolution by using the Microsoft Azure infrastructure. In addition to supporting internet-facing DNS domains, Azure DNS now also supports private DNS domains.
Azure DNS provides a reliable, secure DNS service to manage and resolve domain names in a virtual network without needing a custom DNS solution. By using private DNS zones, you can use your own custom domain names rather than the Azure-provided names available today. Using custom domain names helps you to tailor your virtual network architecture to best suit your organization’s needs. It provides name resolution for virtual machines (VMs) within a virtual network and between virtual networks. Also, customers can configure zones names with a split-horizon view, which allows a private and a public DNS zone to share a name.
Why Citrix GSLB for Azure DNS private zone?
In today’s world, businesses want to transition their workloads from on-premises to Azure cloud. The transition to cloud allows them to leverage time to market, capital expenses/price, ease of deployment and security. Azure DNS Private Zone service provides a unique proposition for the businesses that are transitioning part of their workloads to the Azure Cloud. These businesses can create their private DNS Name, which they had for years in on-premises deployments, when they use the private zone service. With this hybrid model of intranet application servers being in on-premises and Azure cloud connected via secure VPN tunnels, the one challenge is how a user can have seamless access to these intranet applications. Citrix ADC solves this unique use case with its global load balancing feature, which routes the application traffic to the most optimal distributed workloads/servers either on-premises or on Azure cloud and provides application server health status.
Use Case
Users in on-prem network and in different Azure VNETs should be able to connect to the most optimal servers in an internal network for accessing the required content. This ensures that the application is always available, optimized cost and user experience is good. Azure private traffic management (PTM) is the primary requirement here. Azure PTM ensures that users’ DNS queries resolve to an appropriate private IP address of the application server.
Use Case Solution
Citrix ADC includes the global server load balancing (GSLB) feature, which can help meet the Azure PTM requirement. GSLB acts like a DNS server, which gets the DNS requests and resolves the DNS request into an appropriate IP address to provide:
- Seamless DNS based failover
- Phased migration from on-premises to cloud
- A/B Testing a new feature
Among many load balancing methods supported, following methods can be useful in this solution:
- Round Robin
-
Static proximity (Location based server selection): It can be deployed in two ways
- EDNS Client Subnet (ECS) based GSLB on Citrix ADC
- Deploy a DNS forwarder for every Virtual network
Topology
- The Citrix ADC GSLB deployment for Azure private DNS zone logically looks shown in Figure 1.
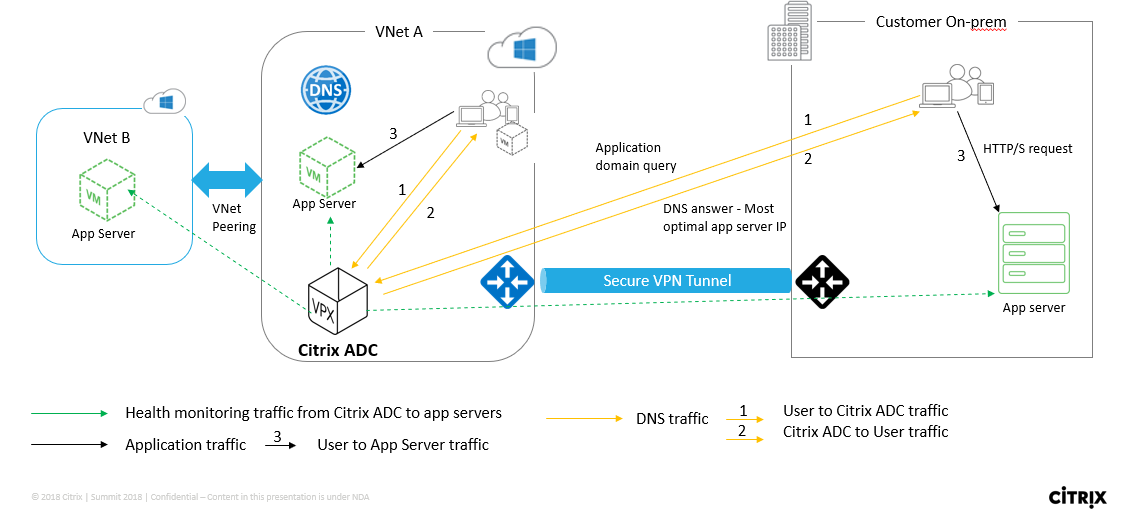
- A user can access any application server either on Azure or on-prem based on Citrix ADC GSLB load balancing method in an Azure private DNS zone
- All traffic between on-prem and Azure Virtual Network is through a secure VPN tunnel only
- Application traffic, DNS traffic, and monitoring traffic are shown in the preceding topology.
- Depending on the required redundancy, Citrix ADC and DNS forwarder can be deployed in the Virtual Networks and data centers. For simplicity purpose, only one Citrix ADC is shown here but we recommend at least one set of Citrix ADC and DNS forwarder for Azure region.
- All user DNS queries first go to the DNS forwarder that has rules defined for forwarding the queries to appropriate DNS server.
Configuring Citrix ADC for Azure DNS Private Zone
Products and Versions tested
| Product | Version |
|---|---|
| Azure | Cloud Subscription |
| Citrix ADC VPX | BYOL (Bring your own license) |
Note: The deployment is tested and remains same with Citrix ADC version 12.0 and above.
Prerequisites and configuration notes
The following are general prerequisites and configuration tested for this guide, please cross-check before configuring Citrix ADC:
- Microsoft Azure portal account with a valid subscription
- Ensure connectivity (Secure VPN Tunnel) between on-prem and Azure cloud. To set up a secure VPN tunnel in Azure, see Step-By-Step: Configuring a site-to-site VPN Gateway between Azure and on-premises
Solution description
Let suppose Customer want to host one application Azure DNS private zone (rr.ptm.mysite.net) which runs on HTTPs and is deployed across Azure and On-premises with intranet access based on round robin GSLB load balancing method. To achieve this deployment by enabling GSLB for Azure private DNS zone with Citrix ADC consists of two parts – configuring the Azure, On-premises and the Citrix ADC appliance.
Part 1: Configure Azure, On-premises Setup
As shown in Topology, set up Azure Virtual Network (VNet A, VNet B in this case) and on-premises setup.
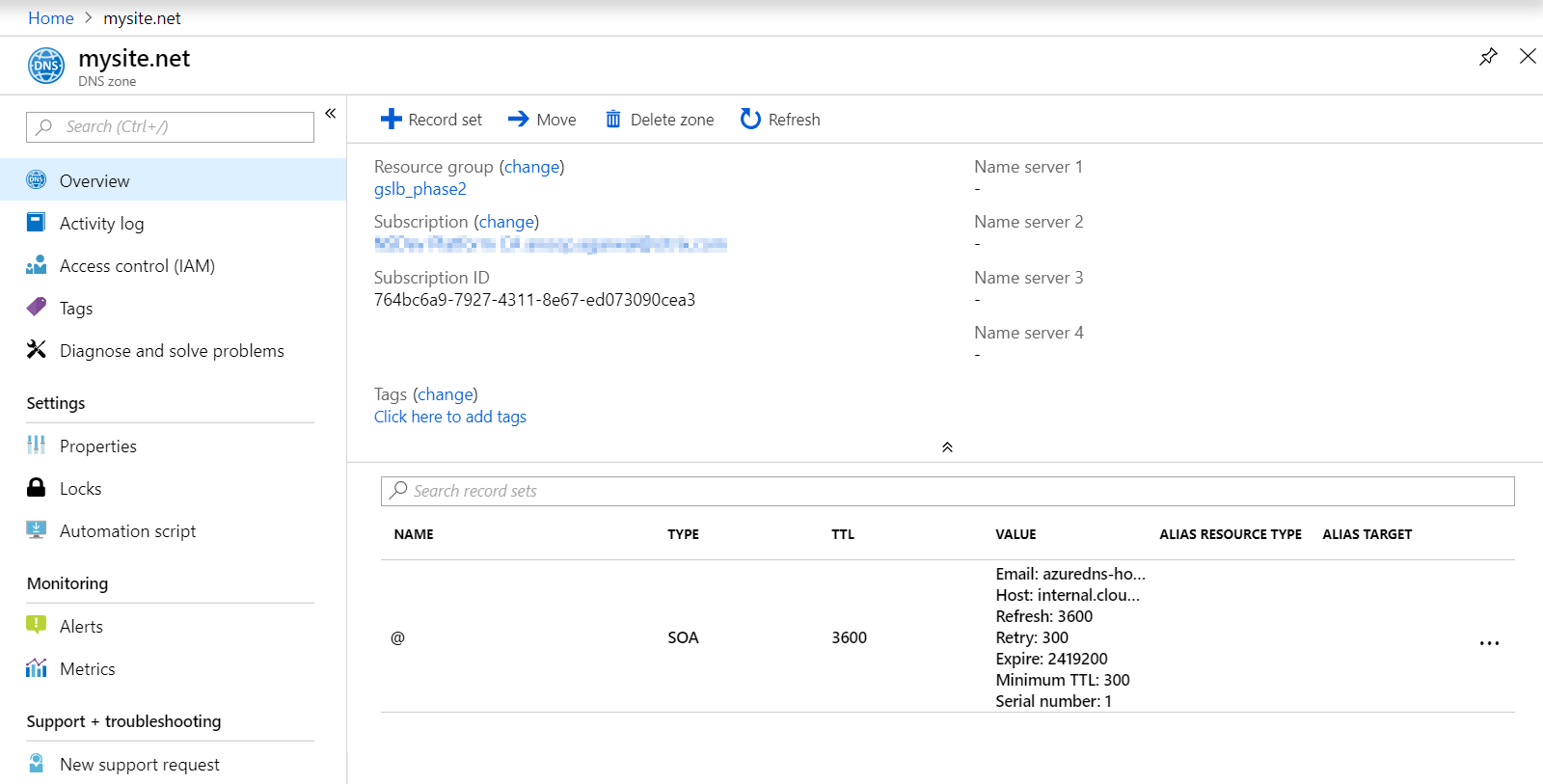
Step 1: Create an Azure private DNS zone with domain name (mysite.net)
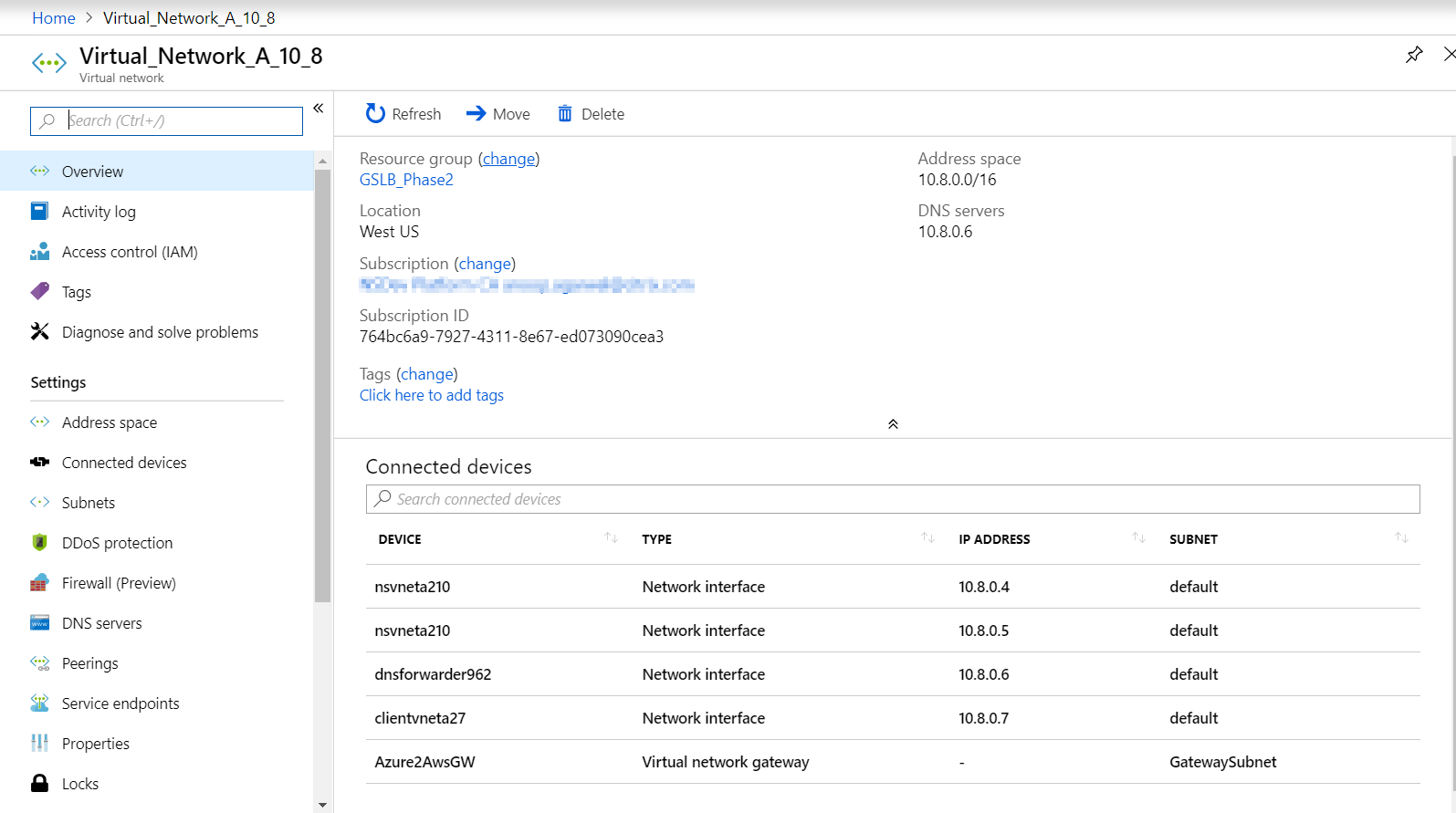
Step 2: Create two Virtual Networks (VNet A, VNet B) in Hub and Spoke model in an Azure region
Step 3: Deploy App Server, DNS Forwarder, Windows 10 Pro client, Citrix ADC in VNet A
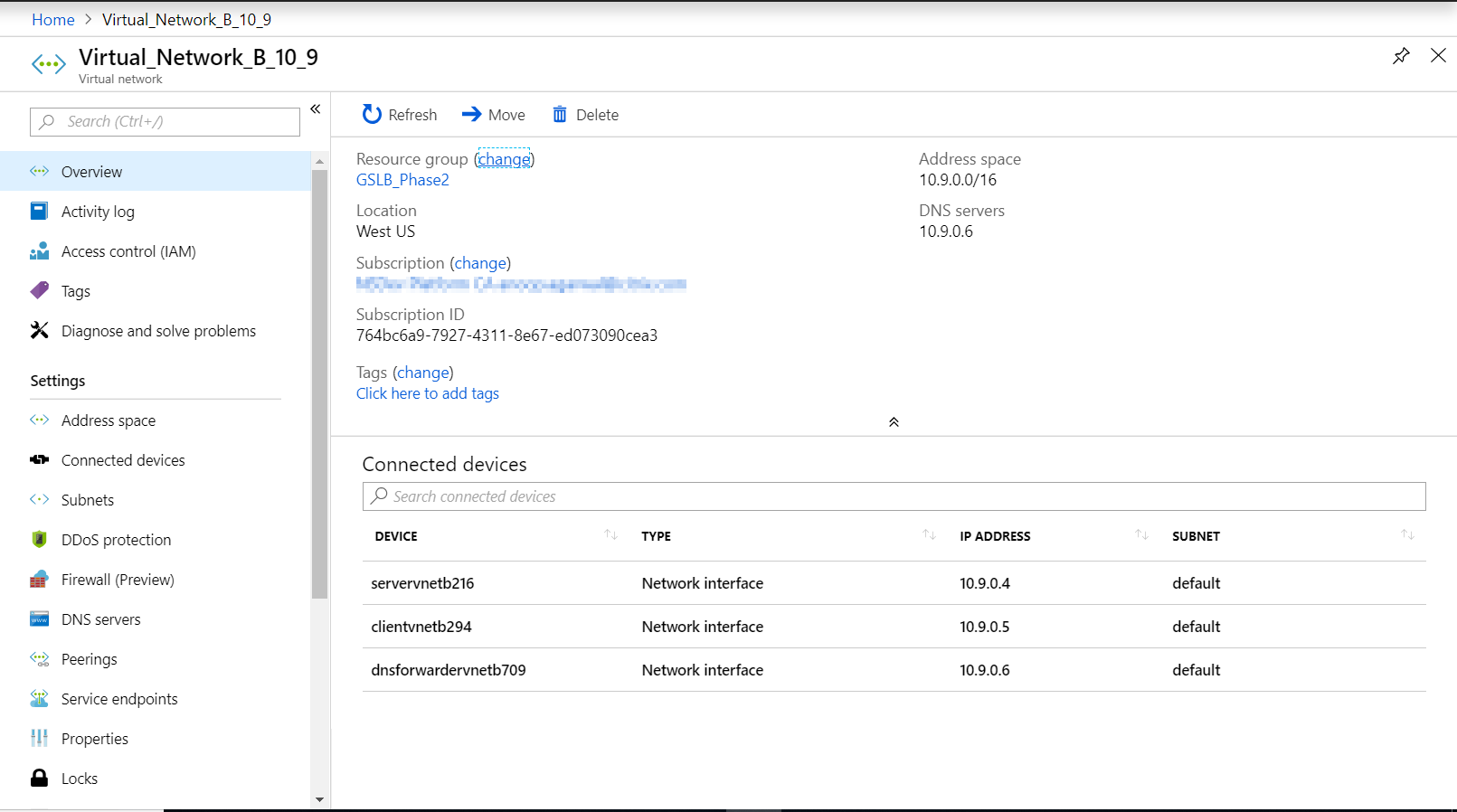
Step 4: Deploy App Server and deploy a DNS Forwarder if any clients are in VNet B
Step 5: Deploy App server, DNS Forwarder, and Windows 10 pro client on on-premises
Azure private DNS Zone
Log into the Azure Portal and select or create a dashboard. Now click create a resource and search for DNS zone to create one (mysite.net in this case) as shown in the following image.
Azure virtual Networks (VNet A, VNet B) in Hub and spoke Model
Select the same dashboard and click create a resource and search for virtual networks to create two virtual networks namely VNet A, VNet B in same region and peer them to form a Hub and Spoke model as shown in the following image. See Implement a hub-spoke network topology in Azure for information about how to set up a hub and spoke topology.
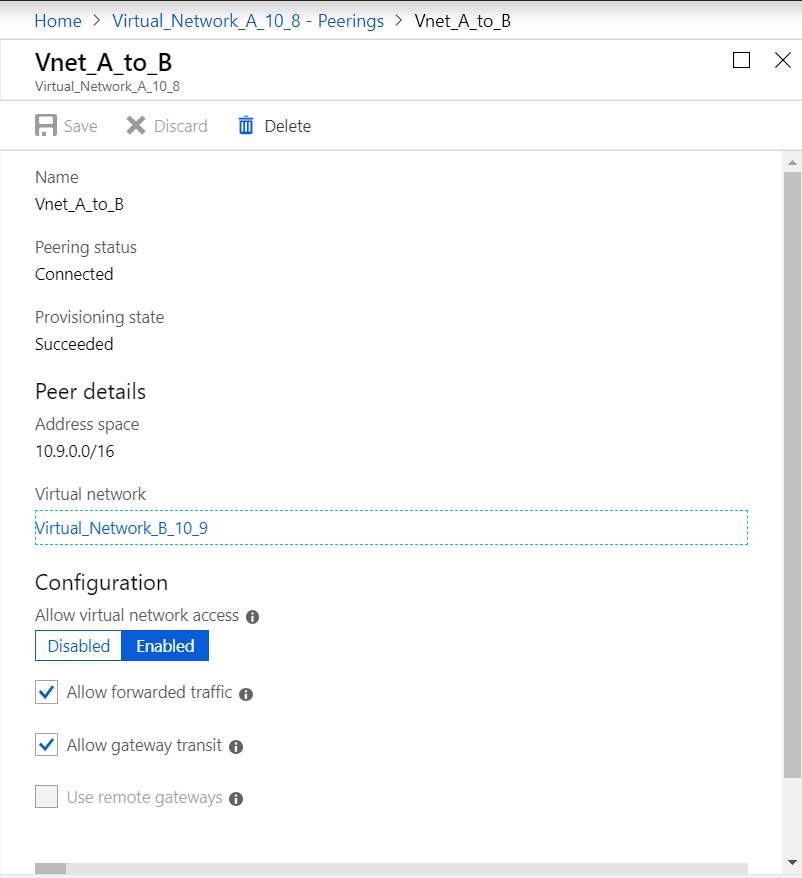
VNet A to VNet B peering
To peer VNet A and VNet B click peerings from settings menu of VNet A and peer VNet B, enable Allow forwarded traffic and Allow gateway transit as shown in the following image.
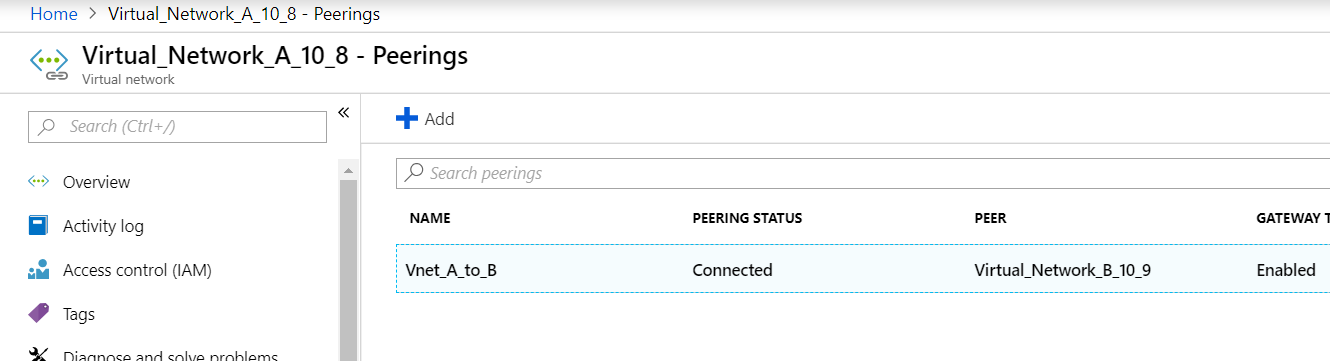
After successful peering you see as shown in the following image:
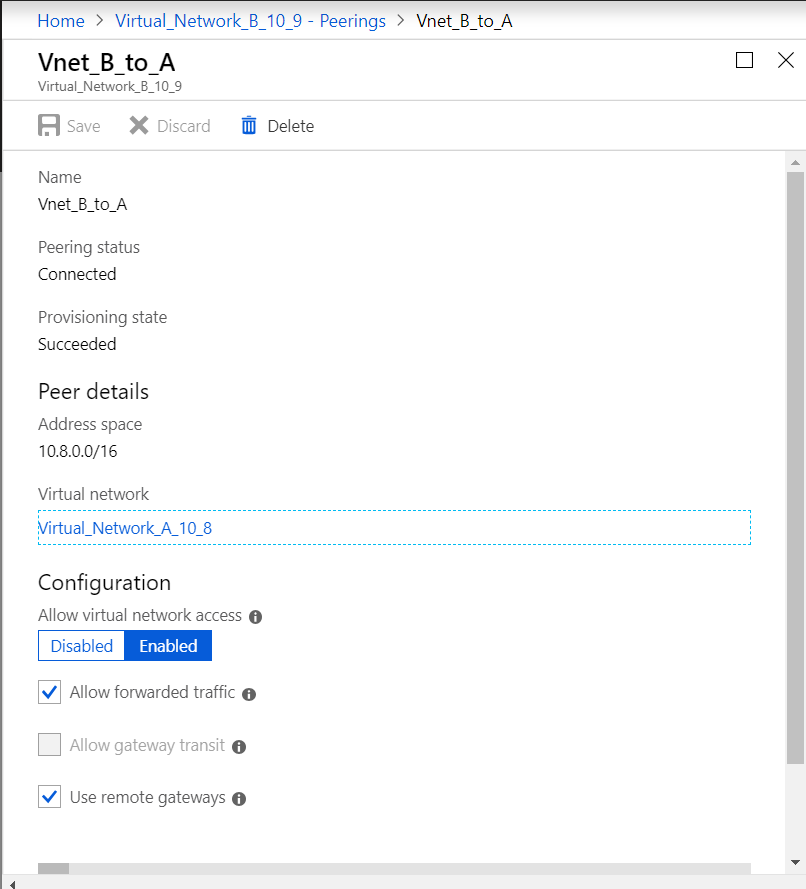
VNet B to VNet A peering
To peer VNet B and VNet A click peerings from settings menu of VNet B and peer VNet A, enable Allow forwarded traffic and Use remote gateways as shown in the following image.
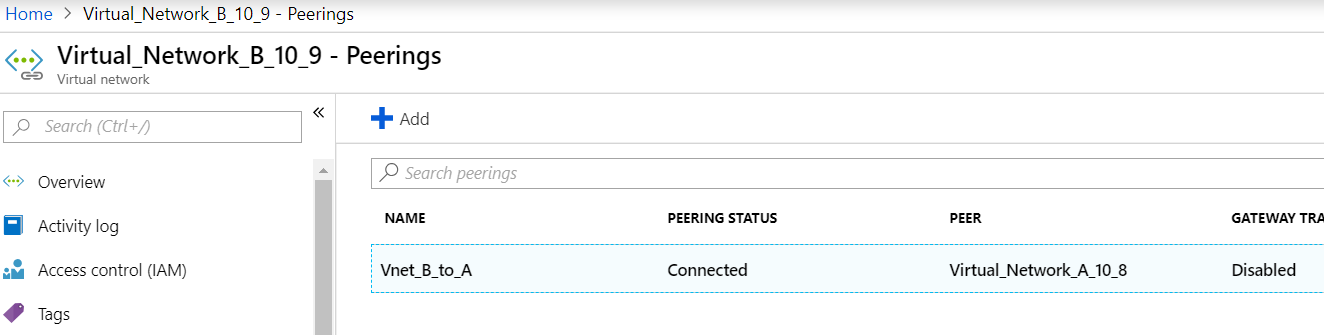
After successful peering you see as shown in the following image:
Deploy App Server, DNS Forwarder, Windows 10 Pro client, Citrix ADC in VNet A
We discuss briefly about App server, DNS forwarder, Windows 10 pro client, and Citrix ADC on VNet A. Select the same dashboard, click create a resource, search for the respective instances and assign an IP from VNet A subnet
App Server
App server is nothing but the web server (HTTP server) where an Ubuntu server 16.04 is deployed as an instance on Azure or on-premises VM and run a CLI command: sudo apt install apache2 to make it as a web server
Windows 10 Pro Client
Launch Windows 10 pro instance as Client Machine on VNet A and on-premises too.
Citrix ADC
Citrix ADC compliments the Azure DNA private zone by health check and Analytics from Citrix MAS. Launch a Citrix ADC from Azure Marketplace based on your requirement, here we have used Citrix ADC (BYOL) for this deployment. Please refer below URL for detailed steps on How to deploy Citrix ADC on Microsoft Azure. After deployment, use Citrix ADC IP to configure Citrix ADC GSLB. See Deploy a NetScaler VPX Instance on Microsoft Azure
DNS Forwarder
It is used to forward the client requests of hosted domains bound to Citrix ADC GSLB (ADNS IP).Launch an Ubuntu server 16.04 as Linux instance (Ubuntu server 16.04) and refer below URL on how to set up it as a DNS forwarder.
Note: For Round Robin GSLB load balancing method one DNS forwarder for Azure Region is sufficient but for Static proximity we need one DNS forwarder per virtual Network.
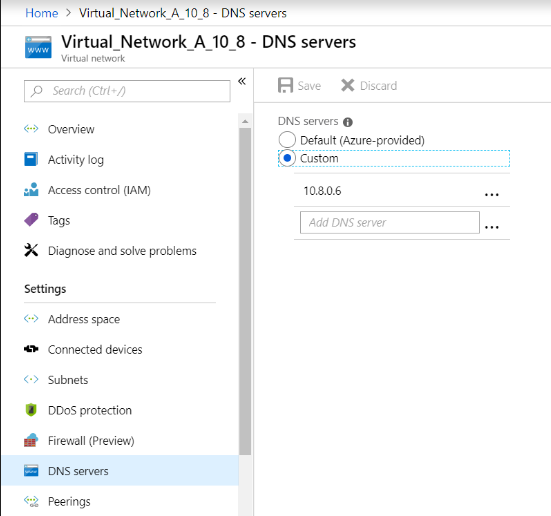
After deploying forwarder change the DNS server settings of Virtual network A from default to custom with VNet A DNS forwarder IP as shown in the following image, and then modify the named.conf.options file in VNet A DNS forwarder to add forwarding rules for domain (mysite.net) and subdomain (ptm.mysite.net) to the ADNS IP of Citrix ADC GSLB. Now, restart the DNS forwarder to reflect the changes made in file named.conf.options.
VNet A DNS Forwarder Settings
zone "mysite.net" {
type forward;
forwarders { 168.63.129.16; };
};
zone "ptm.mysite.net" {
type forward;
forwarders { 10.8.0.5; };
}; > **Note:** For the domain ("mysite.net") zone IP address, use the DNS IP of your Azure region. For the subdomain ("ptm.mysite.net") zone IP address, use all ADNS IP addresses of your GSLB instances.
Deploy App Server and deploy a DNS Forwarder if any clients are in VNet B
Now for Virtual Network B, select the same dashboard, click create a resource, then search for the respective instances, and assign an IP from VNet B subnet. Launch App server and DNS Forwarder if there is static proximity GSLB load balancing similar to VNet A.
Edit the VNet B DNS Forwarder settings in named.conf.options as shown:
VNet B DNS Forwarder Settings:
zone "ptm.mysite.net" {
type forward;
forwarders { 10.8.0.5; };
};
Deploy app server, DNS Forwarder, and Windows 10 pro client on on-premises
Now for on-premises, launch the VMs on bare metal and bring App server, DNS Forwarder and Windows 10 pro client similar to VNet A.
Edit the on-premises DNS Forwarder settings in the named.conf.options as shown in the following example.
On-Premises DNS Forwarder Settings
zone "mysite.net" {
type forward;
forwarders { 10.8.0.6; };
};
zone "ptm.mysite.net" {
type forward;
forwarders { 10.8.0.5; };
};
Here for mysite.net we have given DNS forwarder IP of VNet A instead of Azure private DNS zone server IP because it is a special IP not reachable from on-premises. Hence this change is required in the DNS forwarder setting of on-premises.
Part 2: Configure the Citrix ADC
As shown in Topology, deploy the Citrix ADC on Azure Virtual Network (VNet A in this case) and access it through Citrix ADC GUI.
Configuring Citrix ADC GSLB
Step 1: Create ADNS Service Step 2: Create sites – local and remote Step 3: Create services for the local virtual servers Step 4: Create virtual servers for the GSLB services
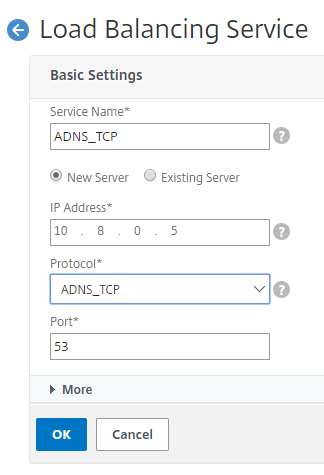
Add ADNS Service
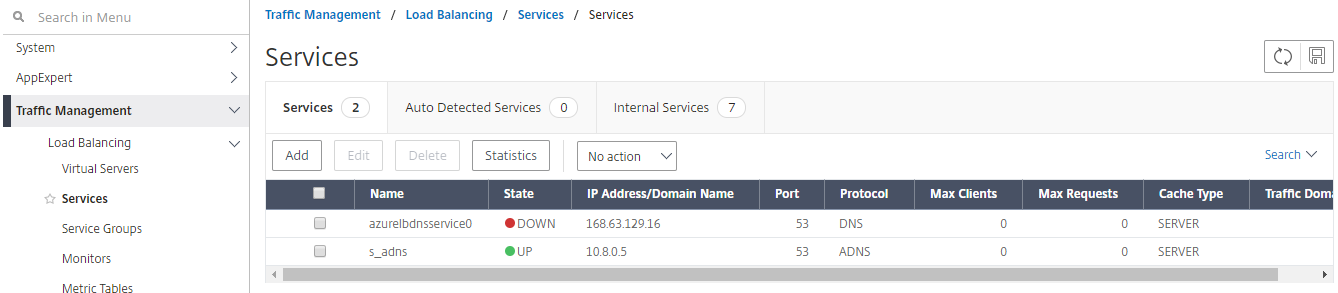
Log into the Citrix ADC GUI. On the Configuration tab, navigate to Traffic Management>Load Balancing > Services. Add a service. It is recommended to configure ADNS service both in TCP and UDP as shown here:

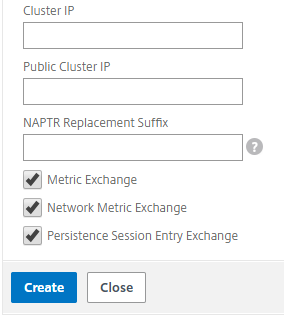
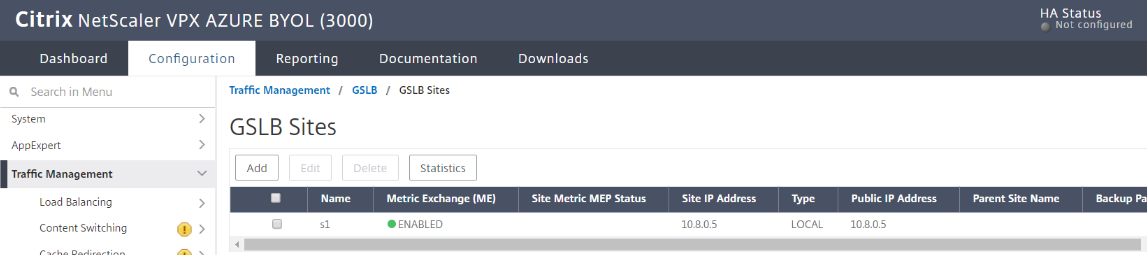
Add GSLB Sites
Add local and remote sites between which GSLB will be configured. On the Configuration tab, navigate to Traffic Management > GSLB > GSLB Sites. Add a site as shown here and repeat the same procedure for other sites.

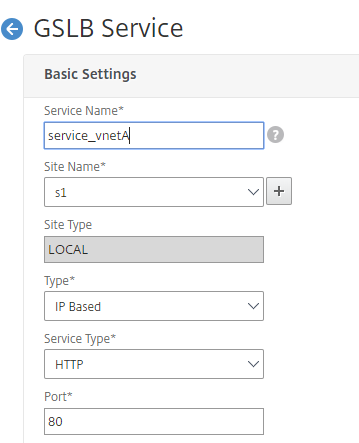
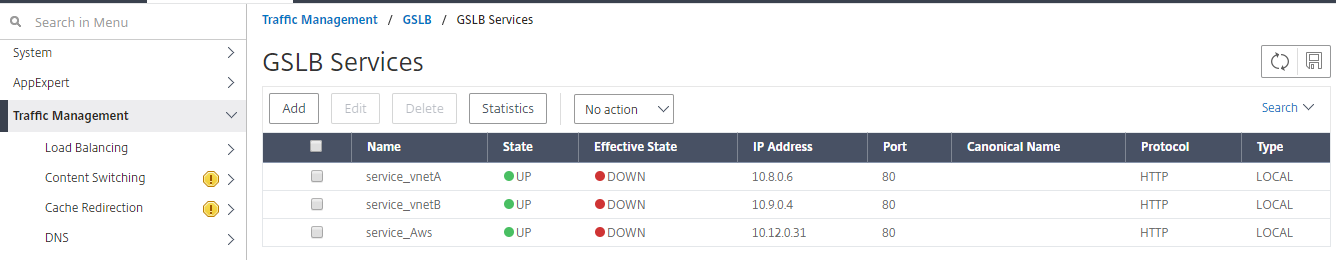
Add GSLB Services
Add GSLB services for the local and remote virtual servers which load balances App servers. On the Configuration tab, navigate to Traffic Management>GSLB > GSLB Services. Add the services as shown in the following examples. Bind HTTP monitor to check server status.
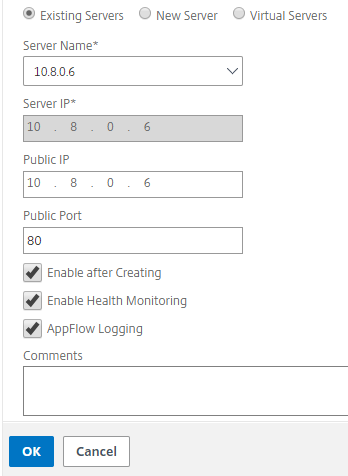
After creating the service, go to the advanced settings tab inside the GSLB service and add Monitors tab to bind GSLB service with an HTTP monitor to bring up the state of service
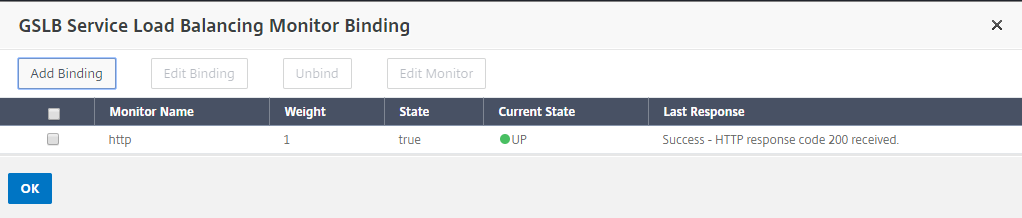
Once you bind with HTTP monitor, the state of services are UP as shown here:
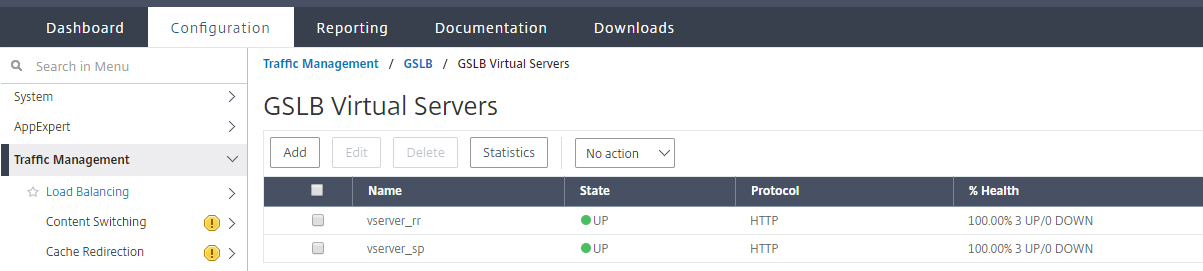
Add GSLB Virtual Server
Add GSLB virtual server through which App servers’ alias GSLB Services are accessible. On the Configuration tab, navigate to Traffic Management>GSLB > GSLB Virtual Servers. Add the virtual servers as shown in the following example. Bind GSLB services and domain name to it.
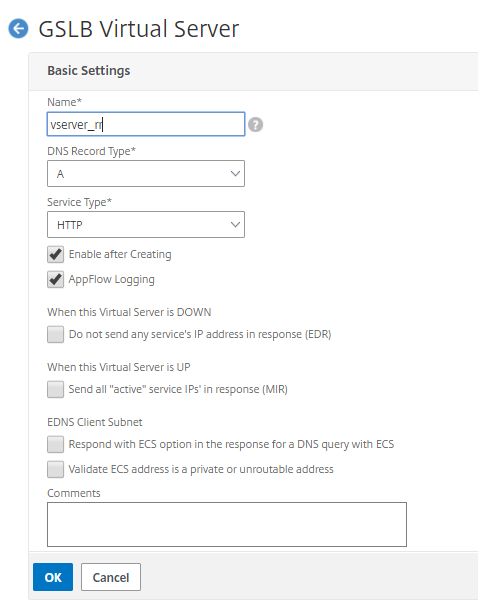
After creating the GSLB virtual server and selecting the appropriate load balancing method (Round Robin in this case), bind GSLB services and domains to complete the step
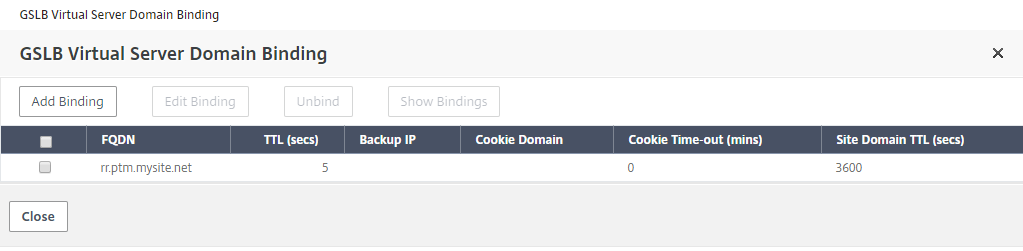
Go to the advanced settings tab inside the virtual server and add Domains tab to bind a domain
Go to Advanced > Services and click the arrow to bind a GSLB service and bind all three services (VNet A, VNet B, On-premises) to virtual server
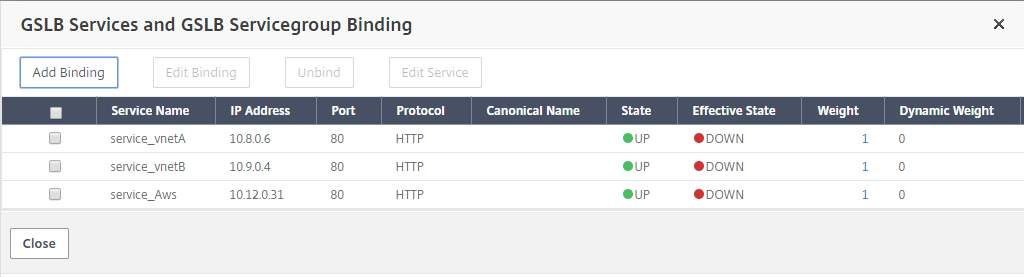
After binding GSLB services and Domain to the virtual server it appears as shown here:
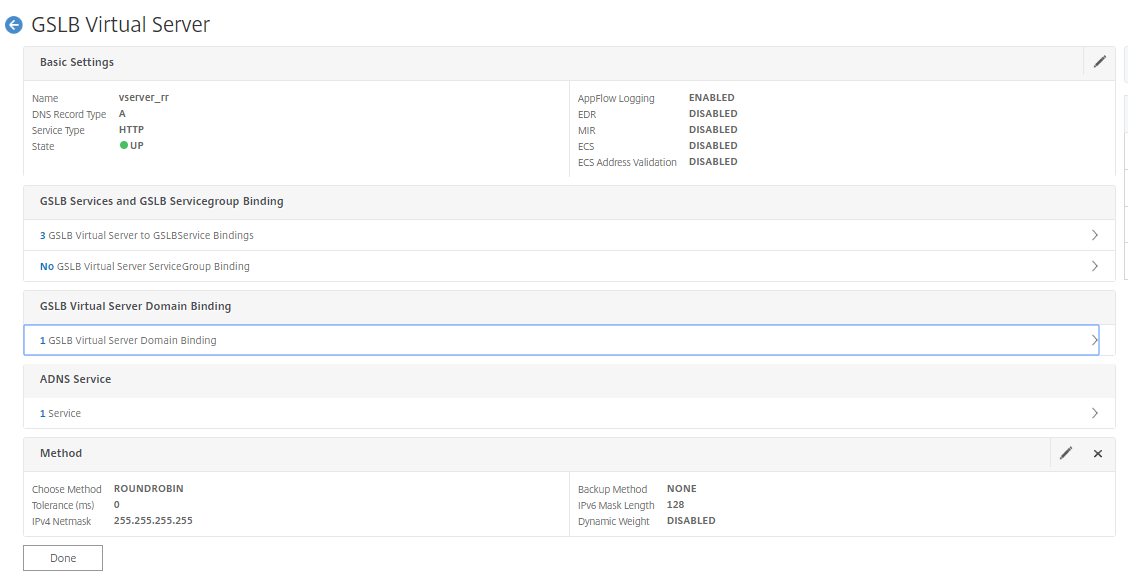
Check if GSLB virtual server is up and 100% healthy. When the monitor shows that the server is up and healthy, it means that sites are in sync and back end services are available.
To test the deployment now access domain URL rr.ptm.mysite.net from either Cloud client machine or on-premises client machine. For suppose access it from cloud windows client machine see that even on-premises App server is accessed in a private DNS zone without any need for third party or custom DNS solutions.
Conclusion
Citrix ADC, the leading application delivery solution, is best suited to provide load balancing and GSLB capabilities for Azure DNS private zone. By subscribing to Azure DNS Private Zone, the business can rely on Citrix ADC Global Server Load Balancing’s (GSLB) power and intelligence to distribute intranet traffic across workloads located in multiple geographies and across data centers, connected via secure VPN tunnels. This collaboration guarantees businesses seamless access to part of their workload they want to move to Azure public cloud.