Certificate authority configuration
This article describes the advanced configuration of Federated Authentication Service (FAS) to integrate with certificate authority servers that are not supported by the FAS administration console. The instructions use PowerShell APIs provided by FAS. You should have a basic knowledge of PowerShell before executing any instructions in this article.
Configure the Microsoft certificate authority for TCP access
By default the Microsoft certificate authority uses DCOM for access. This can result in complexities when implementing firewall security, so Microsoft has a provision to switch to a static TCP port. On the Microsoft certificate authority, open the DCOM configuration panel and edit the properties of the “CertSrv Request” DCOM application:
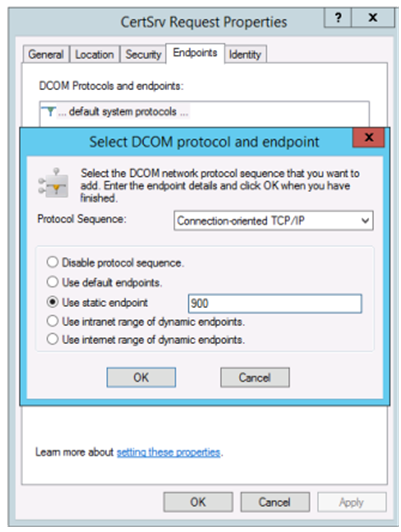
Change the “Endpoints” to select a static endpoint and specify a TCP port number (900 in the graphic above).
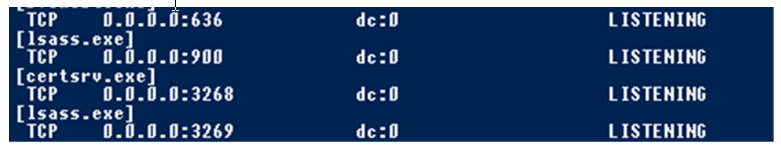
Restart the Microsoft certificate authority and submit a certificate request. If you run netstat –a –n –b you should see that certsvr is now listening on port 900:
There is no need to configure the FAS server (or any other machines using the certificate authority), because DCOM has a negotiation stage using the RPC port. When a client needs to use DCOM, it connects to the DCOM RPC Service on the certificate server and requests access to a particular DCOM server. This triggers port 900 to be opened, and the DCOM server instructs the FAS server how to connect.
Pre-generate user certificates
The logon time for users will significantly improve when user certificates are pre-generated within the FAS server. The following sections describe how it can be done, either for single or multiple FAS servers.
Get a list of Active Directory users
You can improve certificate generation by querying the AD and storing the list of users into a file (for example, a .csv file), as shown in the following example.
Import-Module ActiveDirectory
$searchbase = "cn=users,dc=bvt,dc=local" # AD User Base to Look for Users, leave it blank to search all
$filename = "user_list.csv" # Filename to save
if ($searchbase -ne ""){
Get-ADUser -Filter {(UserPrincipalName -ne "null") -and (Enabled -eq "true")} -SearchBase $searchbase -Properties UserPrincipalName | Select UserPrincipalName | Export-Csv -NoTypeInformation -Encoding utf8 -delimiter "," $filename
} else {
Get-ADUser -Filter {(UserPrincipalName -ne "null") -and (Enabled -eq "true")} -Properties UserPrincipalName | Select UserPrincipalName | Export-Csv -NoTypeInformation -Encoding utf8 -delimiter "," $filename
}
<!--NeedCopy-->
Get-ADUser is a standard cmdlet to query for a list of users. The example above contains a filter argument to list only users with a UserPrincipalName and an account status of ‘enabled.’
The SearchBase argument narrows which part of the AD to search for users. You can omit this if you want to include all users in AD. Note: This query might return a large number of users.
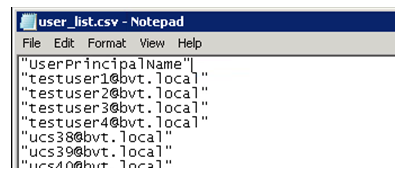
The CSV looks something like this:
FAS server
The following PowerShell script takes the previously-generated user list and creates a list of user certificates.
Add-PSSnapin Citrix.A*
$csv = "user_list.csv"
$rule = "default" # rule/role in your admin console
$users = Import-Csv -encoding utf8 $csv
foreach ( $user in $users )
{
$server = Get-FasServerForUser -UserPrincipalNames $user.UserPrincipalName
if( $server.Server -ne $NULL) {
New-FasUserCertificate -Address $server.Server -UserPrincipalName $user.UserPrincipalName -CertificateDefinition $rule"_Definition" -Rule $rule
}
if( $server.Failover -ne $NULL) {
New-FasUserCertificate -Address $server.Failover -UserPrincipalName $user.UserPrincipalName -CertificateDefinition $rule"_Definition" -Rule $rule
}
}
<!--NeedCopy-->
If you have more than one FAS server, a particular user’s certificate will be generated twice: one in the main server, and the other in the failover server.
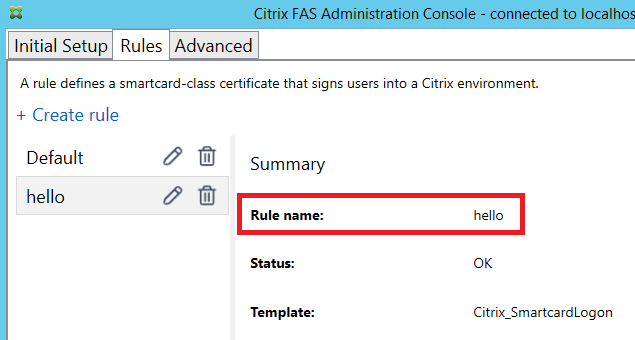
The script above is catered for a rule named ‘default’. If you have a different rule name (for example, ‘hello’), just change the $rule variable in the script.
Renew registration authority certificates
If more than one FAS server is in use, you can renew a FAS authorization certificate without affecting logged-on users.
Note:
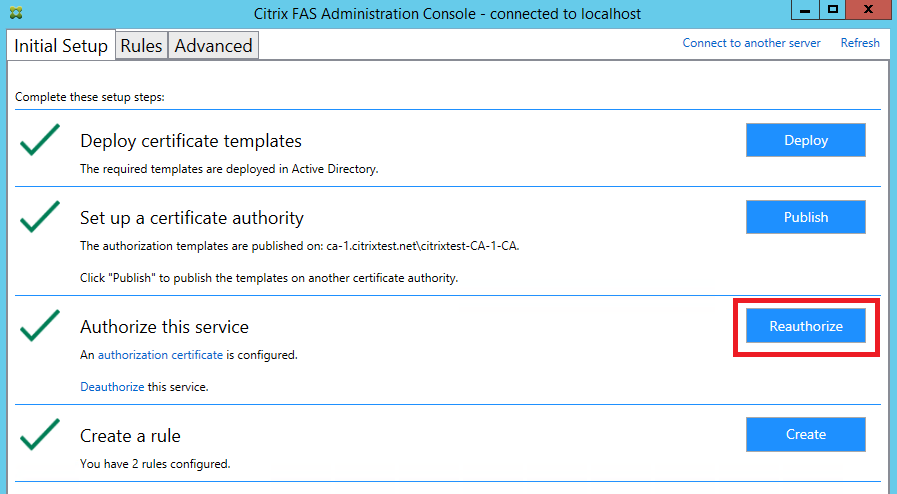
You can also use the GUI to reauthorize FAS:
Complete the following sequence:
-
Create a new authorization certificate:
New-FasAuthorizationCertificate -
Note the GUID of the new authorization certificate, as returned by:
Get-FasAuthorizationCertificate -
Place the FAS server into maintenance mode:
Set-FasServer –Address <FAS server> -MaintenanceMode $true -
Swap the new authorization certificate:
Set-FasCertificateDefinition –AuthorizationCertificate <GUID> -
Take the FAS server out of maintenance mode:
Set-FasServer –Address <FAS server> -MaintenanceMode $false -
Delete the old authorization certificate:
Remove-FasAuthorizationCertificate
Related information
- The Install and configure article is the primary reference for FAS installation and configuration.
- The common Federated Authentication Service deployments are summarized in the Deployment architectures article.
- Other “how-to” articles are introduced in the Advanced configuration article.